Let’s see how to configure Microsoft Defender SmartScreen using Intune, aka Endpoint Manager. Microsoft Defender SmartScreen protects against phishing or malware websites and applications, and the downloading of potentially malicious files.
Microsoft Defender SmartScreen determines whether a site is potentially malicious by analyzing visited web pages looking for indications of suspicious behavior.
SmartScreen also helps us whether a downloaded app or app installer is potentially malicious by checking downloaded files against a list of reported malicious software sites and programs known to be unsafe.
If you turn on Microsoft Defender SmartScreen in organizations, additionally, when enabling this feature, you must also pick whether Microsoft Defender SmartScreen should Warn your employees or Warn and prevent bypassing the message (effectively blocking the employee from the site)
Most important SmartScreen only protects against malicious files from the internet. It does not protect against malicious files on internal locations or network shares, such as shared folders with UNC paths or SMB/CIFS shares.
- Configure Potentially Unwanted Applications PUA Protection in Microsoft Edge using Intune MEM
- Disable Removable Storage Write Access Using Intune
- Intune Logs Event IDs IME Logs Details For Windows Client Side Troubleshooting
Configure Microsoft Defender SmartScreen to Protect Apps Files Using Intune
This section will help you assign the policy set up protection by configuing Defender SmartScreen the block potentially unwanted apps, files using Intune setting catalog policies. You can refer to the following guide to Create Intune Settings Catalog Policy and deploy it only to a set of Intune Managed Windows 11 or Windows 10 devices using Intune Filters.
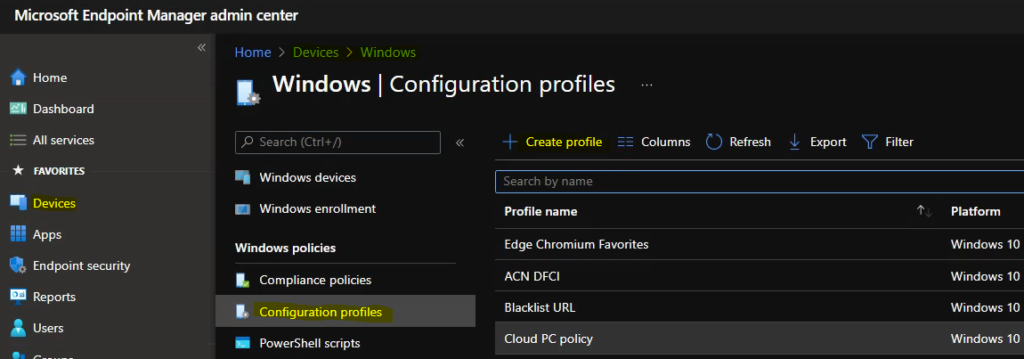
- Sign in to the Endpoint Manager Intune portal https://endpoint.microsoft.com/
- Select Devices > Windows > Configuration profiles > Create profile
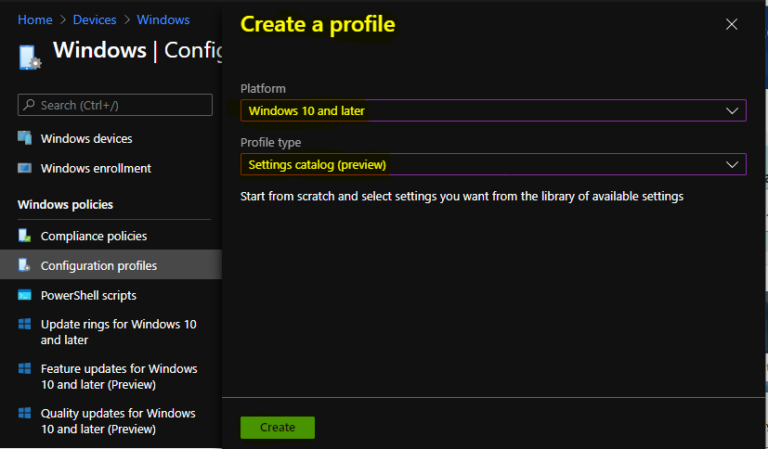
In Create Profile, Select Platform, Windows 10, and later and Profile, Select Profile Type as Settings catalog. Click on Create button.
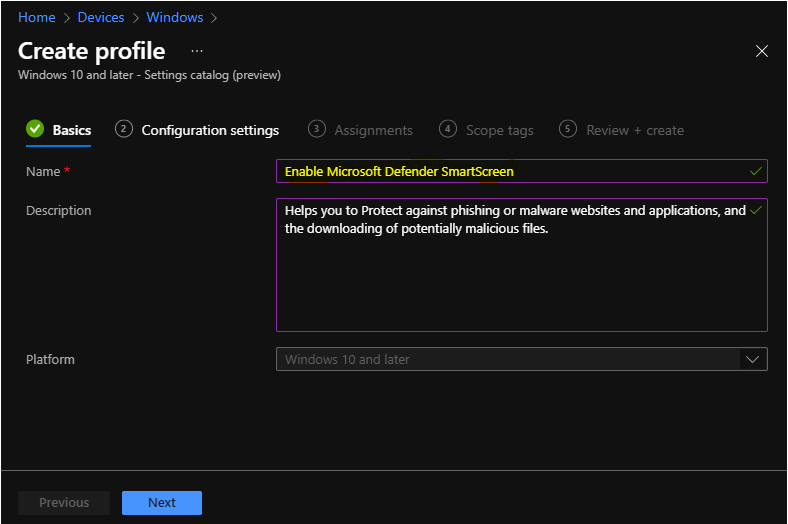
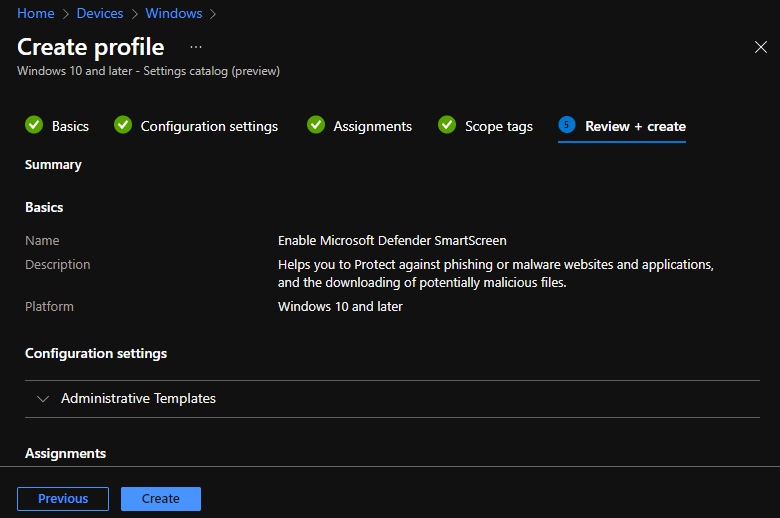
On the Basics tab, enter a descriptive name, such as Enable Microsoft Defender SmartScreen. Optionally, enter a Description for the policy, then select Next.
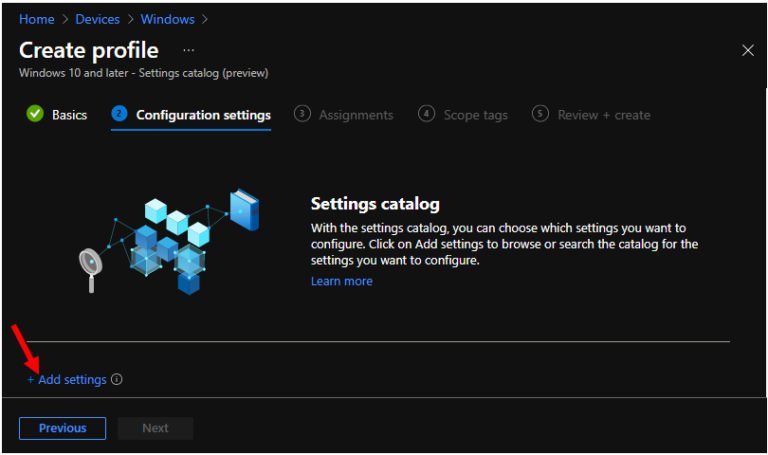
In Configuration settings, click Add settings to browse or search the catalog for the settings you want to configure.
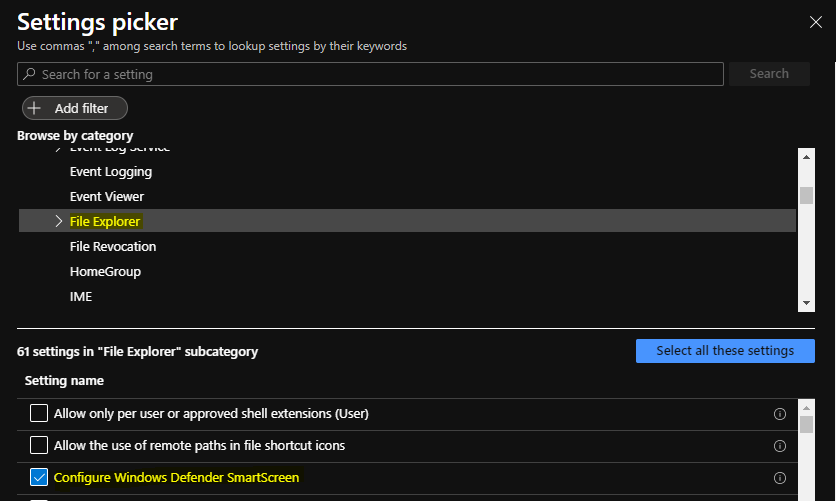
On the Settings Picker windows, Select Administrative Templates > Windows Components > File Explorer to see all the settings in this category. Here, you need to select the below settings Configure Windows Defender SmartScreen. After adding your settings, click the cross mark at the right-hand corner to close the settings picker.
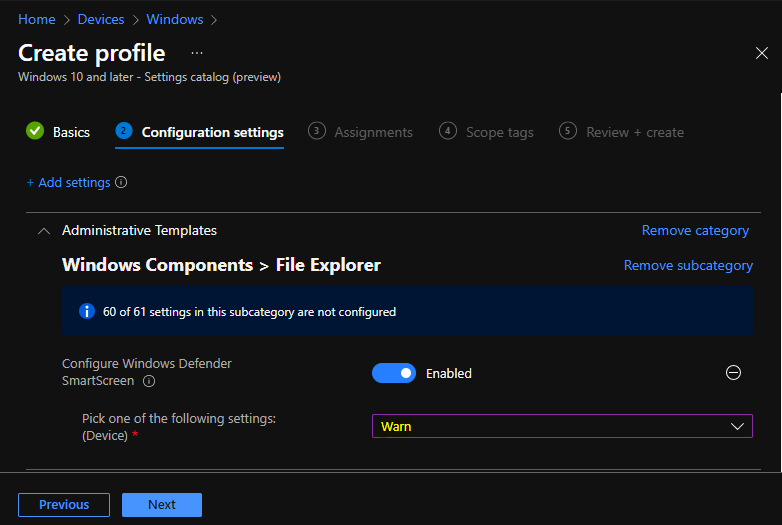
The setting is shown and configured with a default value Disabled. Set Configure Microsoft Defender SmartScreen to Enabled. Additionally, It’s good to configure the following available options and Click Next.
If you enable this policy, SmartScreen will be turned on for all users. Its behavior can be controlled by the following options:
- Warn and prevent bypass – This policy with the “Warn and prevent bypass” option, SmartScreen’s dialogs will not present the user with the option to disregard the warning and run the app. SmartScreen will continue to show the warning on subsequent attempts to run the app.
- Warn – If you enable this policy with the “Warn” option, SmartScreen’s dialogs will warn the user that the app appears suspicious, but will permit the user to disregard the warning and run the app anyway. SmartScreen will not warn the user again for that app if the user tells SmartScreen to run the app.
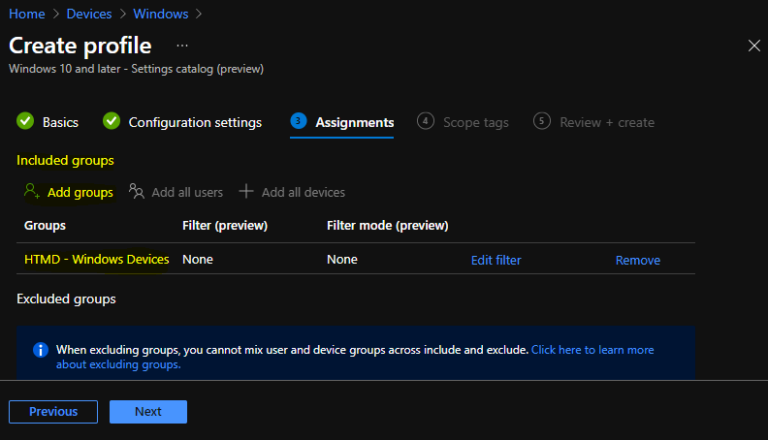
Under Assignments, In Included groups, click Add groups and then choose Select groups to include one or more groups. Click Next to continue.
In Scope tags, you can assign a tag to filter the profile to specific IT groups. Add scope tags (if required) and click Next.
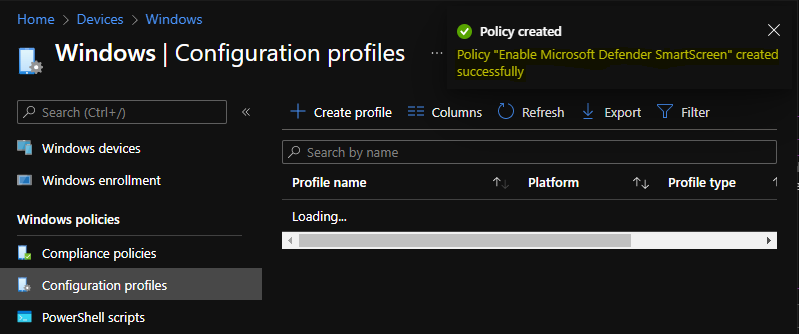
In Review + create, review your settings. When you select Create, your changes are saved, and the profile is assigned.
A notification will appear automatically in the top right-hand corner with a message. Here you can see that Policy “Control Running Background Windows Apps” created successfully. The policy is also shown in the Configuration profiles list.
Your groups will receive your profile settings when the devices check-in with the Intune service. Once the policy applies to the devices.
Windows SmartScreen prevented an unrecognized or unknown app or file downloaded from the Internet and come from another PC.
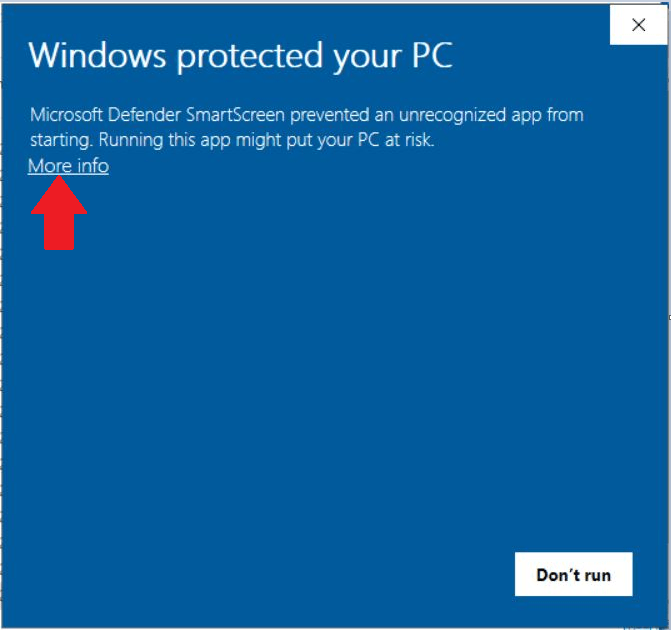
To allow running the app or file, Click on More info and unblock the apps, for more details you can check out post how to Unblock App Files in Windows 10 that are blocked by Open File – Security Warning and Windows SmartScreen.
While unblocking or running applications or files make sure to check security concerns. Sometimes using from trusted source might interfere while using your PC. You can add an app or files to the list of safe or allowed apps to prevent them from being blocked
You can check Intune settings catalog profile report from Intune Portal, which provides an overall view of device configuration policies deployment status.
Author
About Author -> Jitesh has over 5 years of working experience in the IT Industry. He writes and shares his experiences related to Microsoft device management technologies and IT Infrastructure management. His primary focus area is Windows 10, Windows 11 Deployment solution with Configuration Manager, Microsoft Deployment Toolkit (MDT), and Microsoft Intune.

