In this post, let’s have a look at the current world’s Top 5 Windows Security Challenges as per Microsoft’s data analytics and threat intelligence. This post is based on the Windows security session by David Weston, Katherine Holdsworth, and Ron Aquino.
Windows security gets better with every release. See how Windows is a hardened OS at the core that keeps your devices protected and productive end to end. We’ll also offer a sneak peek at where we’re investing our engineering muscle to take Windows platform security even further.
Top 5 Windows Security Challenges
Let’s check the top 5 Windows security challenges in today’s world.
- Phishing – Impersonating oneself as a trustworthy entity in a digital communication
- Untrusted Code – Anything coming to your network or Windows 10 device from non trusted source. This can be an attachment/macro virus/tricking an update install.
- Credential Harvesting – Once an attacker gets onto the machine as a malware application to steal the passwords/credentials.
- Data Theft – Losing a laptop / Remote hacker get into your network and steals information data.
- Unpatched Vulnerabilities – Known Vulnerabilities issue with Windows 10.
More details – This is Windows security! – Microsoft Tech Community
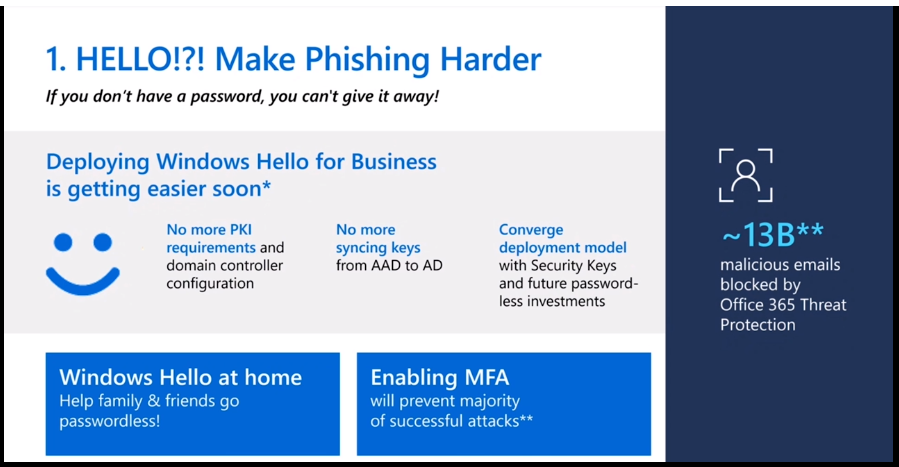
How to Stop Phishing
How to make phishing harder on Windows 10 devices? It seems Microsoft is suggesting using Windows Hello for Business in the enterprise world to make phishing harder by eliminating the passwords from the echo system.
How to Isolate Untrusted Code
You can use Microsoft’s Application Guard for Office to isolate untrusted documents and files in a virtual sandbox containing the damage from bad macros.
- You can use Microsoft Defender Application Control powered by AI to rate the trusted sources around the world.
How to Prevent Credential Harvesting
- You can raise the bar with hardware-backed and VBS (Virtualization-Based Security) protection.
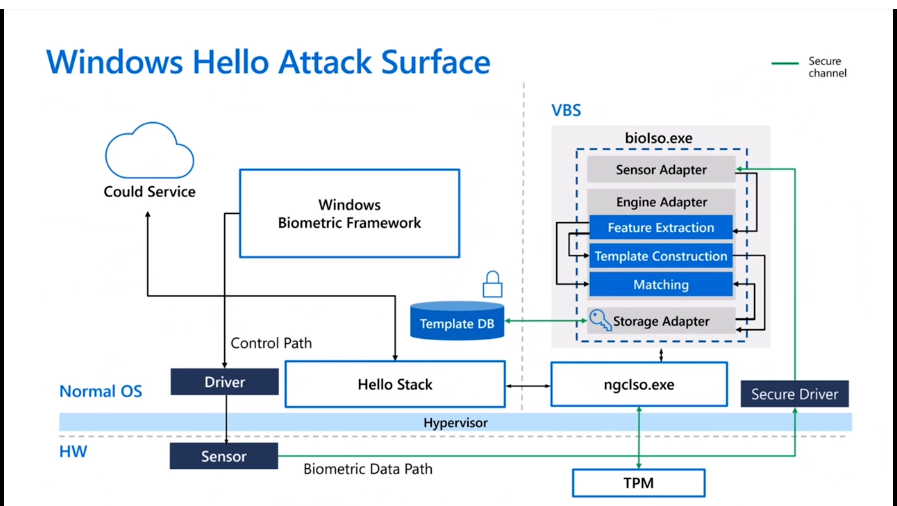
- Windows Hello Attack Surface diagram to help to prevent Credential Harvesting.
How to Prevent Data Theft in Windows 10
- Securing Data from Lost or Stolen Devices with encryption and other methods listed down.
- Virtualized Based Security
- Security-core PC
- Secure Memory Encryption and Total Memory Encryption.
- Hardware Security Processor (Pluton)
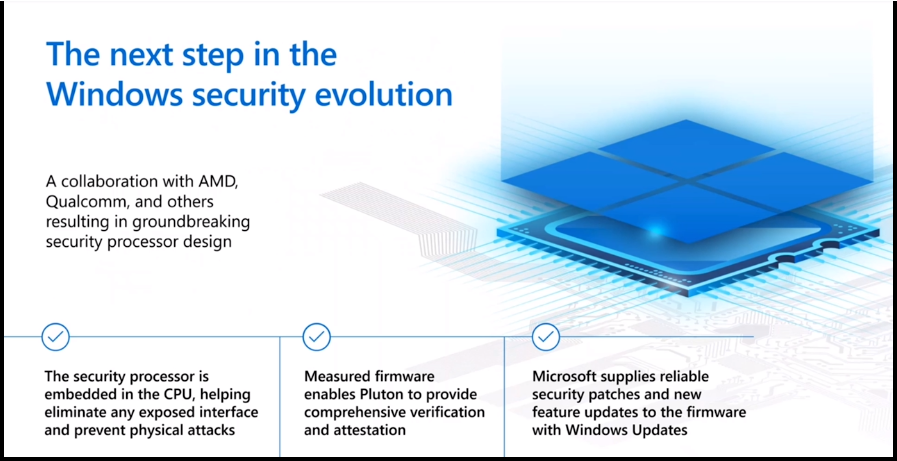
- The next step in the Windows security evolution as per Microsoft is given below.
- A collaboration with AMD, Qualcomm, and others resulted in groundbreaking security process design.
- The security processor is embedded in the CPU, helping eliminate any exposed interface and preventing physical attacks.
- Measured firmware enables Pluton to provide comprehensive verification and attestation.
- Microsoft supplied reliable security patches and new features to the firmware with Windows updates.
How to Handle Known Vulnerabilities issue with Windows 10
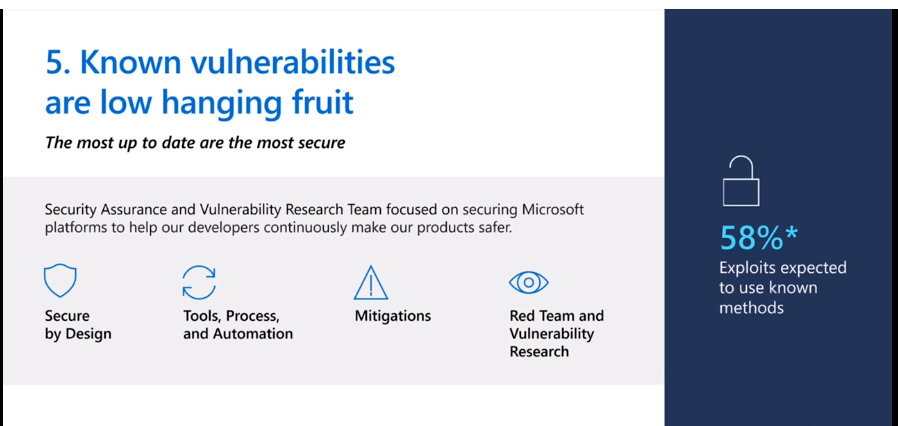
Microsoft is working with internal teams and world-class PEN testers to secure their products like Windows 10. Microsoft’s security assurance and vulnerability research team focused on securing Microsoft platforms to help our developers continuously make Windows 10 safer.
The following are the strategies that Microsoft uses to secure Windows 10:
- Secure by Design
- Tools, Process, and Automation
- Mitigations
- Red Team and Vulnerability Research
Resources
Author
Anoop is Microsoft MVP! He is a Solution Architect in enterprise client management with more than 20 years of experience (calculation done in 2021) in IT. He is a blogger, Speaker, and Local User Group HTMD Community leader. His main focus is on Device Management technologies like SCCM 2012, Current Branch, and Intune. E writes about ConfigMgr, Windows 11, Windows 10, Azure AD, Microsoft Intune, Windows 365, AVD, etc…

