US schools have lost 24.5 million records in breaches since 2005
Tech Republic Security
JULY 2, 2020
A report from Comparitech found that since 2005 K–12 districts and colleges/universities have been attacked more than 1,300 times.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
JULY 2, 2020
A report from Comparitech found that since 2005 K–12 districts and colleges/universities have been attacked more than 1,300 times.

Tech Republic Security
JANUARY 21, 2021
The number of breaches may have fallen, but the number of exposed records hit a high not seen since 2005, says Risk Based Security.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
GeekWire
OCTOBER 5, 2021
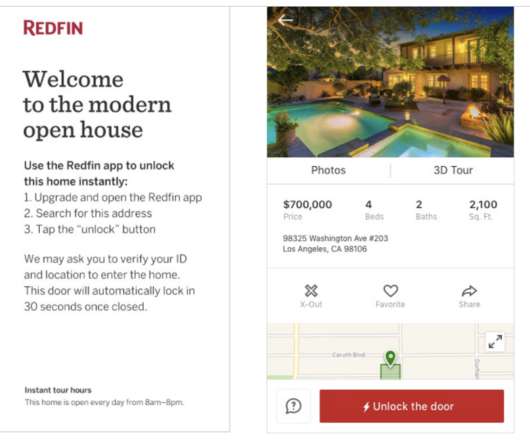
Redfin will now build on its tech offerings by partnering with security company ADT to monitor homes in the real estate brokerage company’s Direct Access program, which enables buyers to tour homes without an agent. ADT will provide additional security to the program, keeping sellers informed about entry and exits on the property.

CIO Business Intelligence
MARCH 19, 2024
With VCF, our customers will achieve a highly efficient cloud operating model that combines public cloud scale and agility with private cloud security and resiliency. From September 2005 to January 2008, he served as chairman of the board of Integrated Device Technology. He has held this position since March 2006.

CTOvision
MAY 3, 2015
HIPAA was enacted in 1996, and by April 2005 security standards were required to be in place for most covered entities. This post provides an overview of key elements we believe security and technology professionals (and most citizens) should be tracking. In 2013 key portions of this law were updated. Related articles.

CTOvision
SEPTEMBER 4, 2013
It is also good news strategically for the cyber security community. Here is more from the press release : NATIONAL EXPERT TO LEAD BROAD CYBER SECURITY. in Cyber Security,computer science professor, Tower Center Senior Fellow. Lyle Endowed Centennial Distinguished Chair in Cyber Security. Frederick R. Gerald Turner. “Dr.

Tech Republic Security
APRIL 29, 2020
A new compilation of data says the home of Hollywood and Silicon Valley has seen nearly 19 million records lost in attacks since 2005.

Vox
APRIL 12, 2024
Getty Images The internet is far less secure than it ought to be. One of the most fascinating and frightening incidents in computer security history started in 2022 with a few pushy emails to the mailing list for a small, one-person open source project. The security ramifications would have been huge.

CIO Business Intelligence
MAY 23, 2023
By extending our multi-cloud strategy, we will invest in extending Vmware’s software stack to run and manage workloads across private and public clouds, which means any enterprise can run application workloads easily, securely, and seamlessly on-prem, or in any cloud platform they prefer. Securities Act of 1933, as amended.

The Verge
DECEMBER 15, 2021
Reddit announced late Wednesday that it has started the process of taking the company public, by filing a confidential S-1 with the Securities and Exchange Commission. Reddit, founded in 2005, had grown to around 52 million daily users as of August, with more than 100,000 active sub-reddits. Illustration by Alex Castro / The Verge.

CTOvision
MARCH 5, 2014
government security clearances. Data Tactics adds key capabilities in Big Data analytics to L-3’s portfolio, a very attractive and specialized domain that immediately enhances L-3’s existing National Security Solutions business and supports its growth as a solutions integrator for the national security and international markets.

CIO Business Intelligence
MARCH 19, 2024
November 2005: Autonomy agrees to buy search technology developer Verity for $500 milllion, its third acquisition of the year after NCorp (in February) and etalk (in June). This is hardly a surprise as the SFO has a reputation for failing to secure convictions. March 2004: Autonomy acquires NativeMinds and Cardiff Software.

Network World
FEBRUARY 23, 2017
Security researchers have achieved the first real-world collision attack against the SHA-1 hash function, producing two different PDF files with the same SHA-1 signature. This shows that the algorithm's use for security-sensitive functions should be discontinued as soon as possible. 1, 2016, although some exemptions have been made.

CIO Business Intelligence
FEBRUARY 24, 2023
A combined Broadcom-VMware will empower customers to modernize and architect their IT infrastructure with large-scale, secure, and reliable yet flexible solutions. The move to multi-cloud is changing the way modern software applications are designed and built. Securities Exchange Act of 1934, as amended, and Section 27A of the U.S.

CIO Business Intelligence
AUGUST 1, 2023
Customers can also operate with confidence as a result of our actions in software, such as our migration of Symantec Web Security Service and Cloud Access Security Broker onto Google Cloud. From September 2005 to January 2008, he served as chairman of the board of Integrated Device Technology. Securities Act of 1933, as amended.

CTOvision
JULY 9, 2014
The Federal Government has a tremendous responsibility to protect the safety and security of Americans both at home and abroad. David joined Basis Technology in 2005. Analysis Cyber Security DoD and IC Events Basis Technology' of Engineering, Basis Technology. Thursday, July 24, 2014. 2:00 pm – 3:00 pm (EST). About the Speaker.

GeekWire
JANUARY 12, 2021
He originally joined the travel company’s board in 2005. AskJeeves was acquired in 2005 by IAC, the internet media company run by Barry Diller, who is also chairman of Seattle-based Expedia Group. The 9-year old company provides security technology and analysts, with a focus on healthcare, financial and government organizations.

Dataconomy
FEBRUARY 27, 2024
For instance, those who invested $1,000 in Nvidia when it was recommended by Stock Advisor on April 15, 2005, would have seen their investment grow to $482,894. The information contained herein is not an offer to sell or a solicitation to buy any securities.

CTOvision
FEBRUARY 9, 2016
Intelligence Community: Security of Information systems: Allow me to turn now to a transnational threat that is, at present, difficult to measure -- the threat of attack against our information systems and information-based infrastructures. Bob Gourley. While there you can find similar warnings delivered every year up to today.

CTOvision
FEBRUARY 24, 2014
By Bob Gourley Editor’s note: We have watched Endgame since their founding and believe their make very positive contributions to the security ecosystem. Alan Wade Alan Wade retired from federal service at the end of 2005 after a thirty-five year career in the Central Intelligence Agency. Related Posts. Endgame, Inc.

GeekWire
JANUARY 13, 2023
” Spencer worked 12-hour days for almost two months to put the new Capitol Hill store together, which included installing heightened security measures from the ground up. That new Pink Gorilla is in a 1,400-square-foot venue on 613 E. Pike Street, about seven blocks east from the Washington State Convention Center.

Network World
MAY 10, 2017
Browser vendors and certificate authorities have been engaged in a coordinated effort to phase out the use of SHA-1 certificates on the web for the past few years, because the hashing function no longer provides sufficient security against spoofing. National Institute of Standards and Technology has banned the use of SHA-1 by U.S.

CIO Business Intelligence
MARCH 7, 2023
Together, we’ll be better positioned to help customers speed app modernization, move to the cloud faster and support a more secure and hybrid workforce. Securities Exchange Act of 1934, as amended, and Section 27A of the U.S. Securities Act of 1933, as amended.

CIO Business Intelligence
SEPTEMBER 14, 2023
But Nasdaq is far more than a financial exchange, offers Peterson; it is a global technology company that is expanding into surveillance and security, continuing to build its SaaS business, and applying AI to many financial applications, he says. The company, which reported net revenues of $3.6

Network World
JULY 20, 2016
With SQL Server 2005 now out of support, if you haven’t already started migrating your older databases onto a newer, supported release to stay in compliance with regulations like PCI DSS, that’s now urgent. The new security options will be significant for many businesses.
The Verge
APRIL 12, 2022
Filed March 4th in the famously patentholder-friendly Western District of Texas court, the four lawsuits claim that techniques fundamental to modern malware detection are based on patented technology — and that the company’s competitors are infringing on intellectual property rights with their implementation of network security software.

CIO Business Intelligence
OCTOBER 31, 2022
This will also empower our customers to modernize and architect their IT infrastructure while ensuring there will be large-scale, secure, and reliable, yet flexible, solutions to do so. We discussed the increasing need for financial institutions to adopt innovative solutions and ensure legacy infrastructure is efficient and secure.

GeekWire
JUNE 25, 2021
She will serve on the nominating and corporate governance committee and as the company’s national security director, a role required through the wireless carrier’s merger with Sprint. A longtime veteran of Amazon’s cloud computing arm, Valdez joined the company as a senior manager of business development in 2005.

Social, Agile and Transformation
JULY 15, 2008
Security Dangers. Im always looking for good articles describing real security issues on Web 2.0 Hopefully products that address these issues are inexpensive and easy to implement: products that address this issue and provide security with real-time scanning or real-time content inspection. Labels: security , web 2.0.

GeekWire
MARCH 2, 2021
million, according to a filing with the Securities and Exchange Commission. With McGeer as CEO and von Flotow as chairman, the two Stanford classmates built Insitu into a $20 million-a-year business before leaving in 2005. Aerovel raised $2.4 We’ve reached out to the company for more details about the new funding.

GeekWire
SEPTEMBER 25, 2023
Founded in 2005, YC is one of the leading startup accelerators. Watto securely uses this contextual data to build high quality documents/reports that employees spend quarters in writing and getting reviewed. Neum AI, a platform designed to assist companies in maintaining the relevancy of their AI applications with the latest data.
Galido
DECEMBER 4, 2019
They get an option like a business, culture, science, ideas, security, transportation, and many others. Michal Arrington found it in 2005 and later in 2010 was acquired by AOL. It is shaping the economy of the 21st century as it introduces burning topics to the readers on Mobile apps, Cloud, data security, and the Internet of Things.

GeekWire
MARCH 24, 2021
Crimmins, a Seattle tech veteran, founded Startup Haven in 2005. F5 Networks hired Microsoft CVP Yvette Smith as SVP of customer success and business transformation and promoted Gail Coury to SVP and chief information security officer. Security compliance startup Strike Graph named Dan Adams as its new VP of sales.

Trends in the Living Networks
DECEMBER 19, 2007
Financial market traders started using IM because it was useful, but banks were concerned about security and audit trails. Services then became available that provided secure, auditable IM. This is turning out to be a very similar story to instant messaging in financial services. The same thing is happening with social networks.

GeekWire
JUNE 4, 2021
He previously spent 11 years at Microsoft from 2005 to 2016, leading the company’s global sales and marketing teams. Founded in 2017, Core Scientific is building blockchain infrastructure technology related to hosting, transaction processing and application development.

ForAllSecure
NOVEMBER 3, 2021
Moss noted that security people he'd known for years were started getting salaried jobs … and started using their legal names. In the Coming of Age era, 2005-2019, provided "free" long distance and "free" internet access, we're always online, but this gives rise to surveillance capitalism. It will have social impact.

The Verge
NOVEMBER 9, 2020
On Tuesday, it’s expected to announce the first Macs that will run off Apple-designed processors and graphics cards instead of the Intel chips it’s used since 2005. Even recent Macs have started to see Apple’s chips trickle in, with onboard T2 security chips and Touch Bars that run on similar hardware as the Apple Watch does.
Phil Windley
JUNE 14, 2021
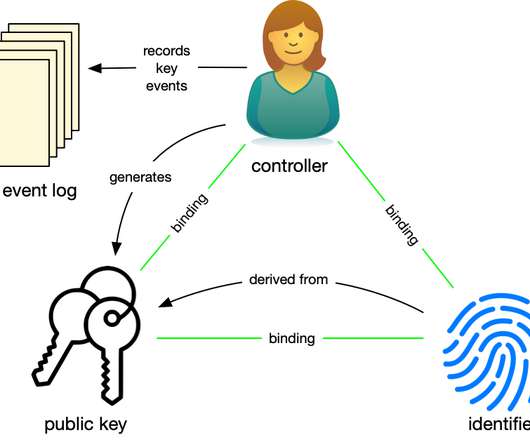
If you're not up to speed with DIDComm and how it creates a secure overlay network on TCP/IP, you should be. DIDs and DID-based Communication or DIDComm form the second layer of the SSI stack, providing a secure communications layer for the exchange of identity information via verifiable credentials. Protocological Power. Generativity.

CIO Business Intelligence
AUGUST 15, 2022
Department of Defense, gaining a security clearance as part of the work we did on the radar systems for the Patriot anti-missile program. It was while working at ICS that I first had the opportunity to collaborate directly with the U.S.

CIO Business Intelligence
NOVEMBER 23, 2022
EA is also used in systems development, IT management and decision-making, and IT risk management to eliminate errors, system failures, and security breaches. Gartner: After acquiring The Meta Group in 2005, Gartner established best practices for EAP and adapted them into the company’s general consulting practices.

Phil Windley
NOVEMBER 9, 2021
There's a saying in security: "Don't roll your own crypto." Kim Cameron gave us a model back in 2005 when he introduced Information Cards. I think we need a corollary in identity: "Don't roll your own interface." But how do we do that? And what should the interface be?

CIO Business Intelligence
JUNE 12, 2023
COBIT 4 was released in 2005, followed by the refreshed COBIT 4.1 COBIT 2019 components COBIT 2019 updates the framework for modern enterprises by addressing new trends, technologies, and security needs. These updates included more information regarding governance surrounding information and communication technology.

Trends in the Living Networks
SEPTEMBER 21, 2005
September 23, 2005 5:43 PM About the blog author Ross Dawson is globally recognized as a leading futurist, entrepreneur, keynote speaker , strategy advisor, and bestselling author. m Kaya wrote:Thank you Ross for the great articl.[ more ] ABC TV interview: The future of direct selling (1) James wrote:Ross,I have followed your work fo.[

CTOvision
FEBRUARY 4, 2015
Data Security—What’s New and What’s Next? Chief Security Architect, Office of the CTO, Cloudera. Security Spotlight: Focus on HIPAA and PCI Compliance. Chief Security Architect, Office of the CTO, Cloudera. Security and Compliance in the Era of Big Data. Chief Security Architect, Office of the CTO, Cloudera.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content