6 Best Authenticator Apps for 2024
Tech Republic Security
MARCH 26, 2024
Authenticator apps provide an extra layer of security. Learn about the best authenticator apps to secure your online accounts and protect your privacy.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
MARCH 26, 2024
Authenticator apps provide an extra layer of security. Learn about the best authenticator apps to secure your online accounts and protect your privacy.
Tech Republic Security
APRIL 2, 2024
Discover the top passwordless authentication solutions that can enhance security and user experience. Find the best solution for your business needs.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
MARCH 20, 2024
Explore top multi-factor authentication solutions for enhanced security and user authentication. Learn about the benefits and features of leading MFA providers.

SecureWorld News
JANUARY 16, 2024
The clock is ticking for organizations worldwide as a maelstrom of cybersecurity compliance deadlines looms in 2024. March 29, 2024: California Privacy Rights Act enforcement begins Get ready, California! March 31, 2024: First compliance phase for PCI DSS v4.0 Hold onto your credit cards! The highly-anticipated PCI DSS v4.0

Kitaboo
FEBRUARY 22, 2024
Types of eBook Protection Strategies to Explore in 2024 Digital Rights Management (DRM) Watermarking Securing eBook Files Secure Distribution Platforms Limit eBook Downloads III. Most readers prefer buying or reading books from authentic sources or platforms. Table of Contents: I. What Is eBook Protection?

SecureWorld News
JANUARY 10, 2024
A quick intro to security keys: A security key can work in place of other forms of two-factor authentication such as receiving a code through SMS or pressing a button in an authentication app. Let's hope to see some change in this department in 2024. When it came to authenticating, both keys worked just fine.

Dataconomy
FEBRUARY 26, 2024
In light of the recent ISC chemistry 2024 paper leak, the HindustanTimes has reported a significant update: the ISC Chemistry Paper 1 (Theory) exam, originally slated for Monday (February 26) at 2 pm, has been unexpectedly postponed. How did ISC chemistry 2024 paper leak surface?

Kitaboo
FEBRUARY 21, 2024
Factors to Consider When Selecting Digital Rights Management Software in 2024 Compatibility Security Features Flexibility and Customization User Experience Compliance and Legal Considerations Cost and Pricing Model Support and Maintenance Customer Reviews III.

Dataconomy
FEBRUARY 7, 2024
The Ivanti vulnerability 2024, identified as CVE-2024-21893 and affecting Ivanti Connect Secure and Ivanti Policy Secure, is currently facing widespread exploitation by numerous adversaries due to a server-side request forgery (SSRF) flaw. Ivanti promptly shared provisional countermeasures following their discovery.

CIO Business Intelligence
JANUARY 15, 2024
As workers at all levels put together their development plans for 2024, IT leaders, recruiters, researchers, and advisors share here what actions CIOs can take to advance their careers if they want to embrace a growth mindset. Make 2024 the year to change that. He says to do otherwise would risk being left behind. “AI

Kitaboo
FEBRUARY 21, 2024
Blockchain for Content Authenticity: As misinformation becomes a growing concern, blockchain technology can be employed to verify the origin and ownership of content, providing readers with confidence in the information they consume.

The Verge
AUGUST 17, 2021
Mastercard says the transition will start in 2024, when the stripe will no longer be required on new cards in regions like Europe where chip cards are already widely used. These are typically authenticated using a PIN, but biometric fingerprint authentication is also emerging as a more secure alternative.

CIO Business Intelligence
JANUARY 22, 2024
Implement strong authentication methods for key internet-facing systems, such as multi-factor authentication. Change your vulnerability mindset to identify legacy vulnerability management systems. This will assist your organization in resolving issues before they become mission-critical.
Kitaboo
APRIL 25, 2024
Encryption Access Control Watermarking Authentication V. Authentication DRM systems often utilize authentication mechanisms to verify the identity of users or devices attempting to access protected content. What Methods Does DRM Use? Wrapping Up What is ePUB DRM?
Kitaboo
FEBRUARY 21, 2024
When it comes to exploring the full potential of your digital creations in 2024, there’s one indispensable tool that stands out for authors, publishers, content creators, and scriptwriters – Digital Rights Management software (DRM). Why Should You Use Digital Rights Management Software in 2024? Let’s dive in!

Network World
MARCH 8, 2021
SASE, pronounced "sassy," blends SD-WAN's network optimization features with security capabilities such as zero-trust authentication, data loss prevention, threat detection, and encryption. Gartner estimates at least 40% of enterprises will have explicit strategies to adopt SASE by 2024, up from less than 1% at the end of 2018.

Kitaboo
APRIL 25, 2024
The authorization can be conferred through various means, such as license keys, digital certificates, or online authentication. Controls and Permissions Various control and permission mechanisms like password protection, time-limited access, restricted viewing, restricted printing, user authentication, location control etc.,

Kitaboo
MARCH 30, 2024
Benefits of Using DRM Software Enables Customization of Access Protects the Authenticity of Content Tracks eBook Usage Prevents IP Theft Ensures Regulatory Compliance Supports Cross-Platform Distribution Facilitates Secure Global Distribution Protects Revenue III. How Does Drm Software Protect Your eBooks?

Kitaboo
MARCH 28, 2024
How DRM Protects eBook Content Encryption License Management Digital Watermarking Authentication Mechanisms IV. Authentication Mechanisms DRM software also employs authentication mechanisms to verify the identity and credentials of users seeking access to protected eBook content. Implementing DRM in Digital Publishing V.

Kitaboo
FEBRUARY 29, 2024
In this blog, we will explore the key differences between traditional and digital reading and delve further into the immense advantages that digital reading offers in 2024. Let’s get started! Table of Contents I.
Dataconomy
FEBRUARY 27, 2024
This platform allows you to employ text prompts for creating authentic artwork and offers the flexibility to modify the art style model, enabling the translation of your imagination into art. Maze Guru Maze Guru stands as a notable Discord AI art generator, swiftly transforming your ideas into stunning digital art.
Kitaboo
MARCH 26, 2024
eBook DRM implements total control over resources using technologies such as encryption and authentication. It includes methods like user authentication, verification, licensing of eBooks, encryption, etc. The possibility of piracy, theft, or redistribution need not worry publishers or content creators.

SecureWorld News
JANUARY 10, 2024
This highlights the importance of robust two-factor authentication (MFA) protocols, which were not enabled for the SEC's X account. Strengthening authentication mechanisms and reviewing access controls are equally important priorities. " This incident serves as a powerful wake-up call for both organizations and individuals.

Kitaboo
APRIL 22, 2024
Features like user authentication, password protection and restricted printing/viewing options ensure that content is accessed only by authorized users and under specified conditions. This authorization process is facilitated through various methods, such as digital certificates, license keys, or online authentication.

SecureWorld News
FEBRUARY 29, 2024
A : Please use multi-factor authentication (MFA) everywhere possible. Authenticator apps or physical tokens are best, but text-based (SMS) MFA/2FA is better than nothing. Q : Lastly, what are you most looking forward to at your regional SecureWorld 2024 conference? This will likely afford you more opportunities in the future.

Kitaboo
MARCH 26, 2024
Security Features: The DRM solution must offer robust security measures like encryption, watermarks, and device authentication to protect against unauthorized use and piracy. Blog , Digital Publishing , eBook solution / January 29, 2024 The post Secure Your Writing with Top DRM Software Picks for Your eBooks appeared first on Kitaboo.

Kitaboo
MARCH 21, 2024
Encrypting content and controlling access through licensing and authentication mechanisms deter piracy and ensure legitimate readers have authorized access. User authentication ensures that only legitimate readers with valid credentials can access the content.

Kitaboo
MARCH 27, 2024
The need for unique access codes or authentication mechanisms allows DRM to ensure that only authorized users can view or download the content. DRM guarantees that their intellectual rights are valued and they also get reasonable settlement for their job.

Kitaboo
APRIL 23, 2024
Moreover, Colibrio empowers developers to extend and customize the framework through its API to allow integration of DRM services, user authentication, and user interface elements that perfectly match the application’s design.

Phil Windley
OCTOBER 23, 2023
In closing circle someone said (paraphrashing) that authentication is solved and the next frontier is authorization. IIW 38 will be held April 16-18, 2024 at the Computer History Museum. The energy was high and I enjoyed seeing so many people who are working on identity talking with each other and sharing their ideas. I tend to agree.

Kitaboo
MARCH 13, 2024
Consider factors like budget and features such as user authentication, access control, and encryption strength. This involves organizing the content, ensuring proper layout, and preparing it for digital distribution. Select the Right DRM System Choose a DRM system that fits your needs.

SecureWorld News
NOVEMBER 23, 2022
Zero Trust uses continuous multi-factor authentication, micro segmentation, advanced encryption, endpoint security, analytics, and robust auditing, among other capabilities, to fortify data, applications, assets, and services to deliver cyber resiliency," the strategy document says.

Dataconomy
FEBRUARY 14, 2024
pic.twitter.com/hCnNfcireg — bodiggles (@bodigglesL) February 13, 2024 Following the shocking incident during his Twitch stream, Bodiggles took to social media to provide an update on his condition. Viewers were left shocked and puzzled, wondering what had just happened. god is clutch!!!

GeekWire
DECEMBER 30, 2023
” The “toothbrush test” for AI: “What happens next in 2024, is what somebody once called the toothbrush test. So I think that in 2024, the toothbrush test for AI is going to explode. … In addition, we do need watermarking, authentication, provenance, so we know where things come from.

CIO Business Intelligence
JANUARY 30, 2024
If you want to sell anything to anyone under 40, you will need a compellingly composed and authentically executed sustainability strategy. 2024 is going to be a big year for political, economic, and technology decisions. As CIO, you need a data strategy. You need a cloud strategy. You need a security strategy.
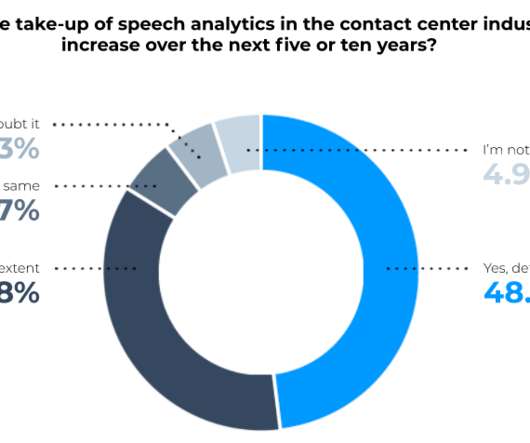
Spearline Testing
MAY 10, 2021
of contact centers will likely reach that point by 2024, voice will still remain the preferred mode of communication. Voice biometrics records a unique imprint of a caller’s voice, and since all voices are unique, they can be analysed by software that can quickly determine authenticity. While another 11.5%

Kitaboo
FEBRUARY 21, 2024
Among these access control mechanisms are user authentication, password protection, or restricted viewing options. There can be various ways to grant this authorization, such as digital certificates, license keys, or online authentication.

Dataconomy
JANUARY 29, 2024
With its advanced features and user-centric design, this technology brings a new level of authenticity to virtual meetings, blurring the lines between the physical and digital worlds. Apple has announced that Vision Pro will hit the US market on February 2, 2024. The pre-orders began on January 19, 2024, and were a spectacle.

CIO Business Intelligence
JANUARY 9, 2024
in order to meet the March 31, 2024, deadline, when v3.2.1 Indeed, as per FAQ 1328 , after March 31, 2024, PCI DSS v4.0 Let’s explore some examples: Multifactor authentication (MFA) technology Requirement 8.4.2 This approach should help usher in a successful transition to PCI DSS version 4.0 is set to expire.

Kitaboo
JANUARY 31, 2024
Experiential learning , on the other hand, offers a more engaging and authentic way of learning that taps into the innate curiosity and potential of every student. Traditional classrooms that rely on passive and memorized learning cannot prepare students for these challenges. appeared first on Kitaboo.
Dataconomy
JANUARY 17, 2024
Watch here: Tesla robot folding shirts This is the video showing the Tesla robot folding shirt: Optimus folds a shirt pic.twitter.com/3F5o3jVLq1 — Elon Musk (@elonmusk) January 15, 2024 While Musk likely expected this demonstration of the robot’s capabilities to awe viewers, my reaction was one of underwhelment.

Dataconomy
MARCH 3, 2024
As we move closer to 2024, besides swift tech progress, it’s vital to assess which solution best fits your business needs strategically. Diverging from VPNs that grant unrestricted access post-authentication, ZTNA implements strict controls and continuous identity verification throughout the user session.

Dataconomy
FEBRUARY 2, 2024
pic.twitter.com/zZMcpspXch — Teortaxes (@teortaxesTex) January 30, 2024 The story began to unfold when a user named “Miqu Dev” uploaded files to HuggingFace, allegedly showcasing a new Large Language Model (LLM) closely related to the technology developed by Mistral, a Paris-based front-runner in open-source AI.

Dataconomy
JANUARY 23, 2024
databreach #CTI #DarkWeb pic.twitter.com/Fim9jOwUzn — HackManac (@H4ckManac) January 17, 2024 Trello data breach hasn’t been confirmed yet Now, before we all hit the panic button, there’s an important update. Use Two-Factor Authentication (2FA) : This adds an extra layer of security.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content