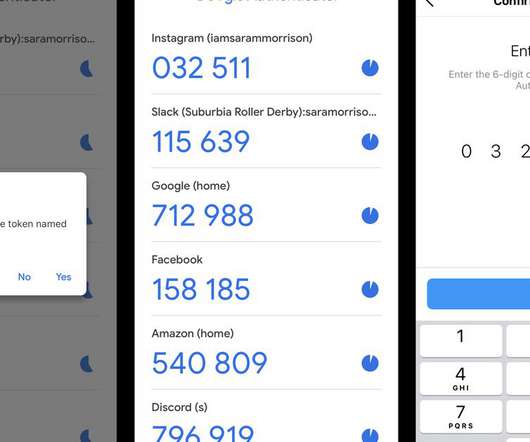
Google Authenticator gets cloud 2FA code backups, doesn't yet provide end-to-end encryption
TechSpot
APRIL 27, 2023
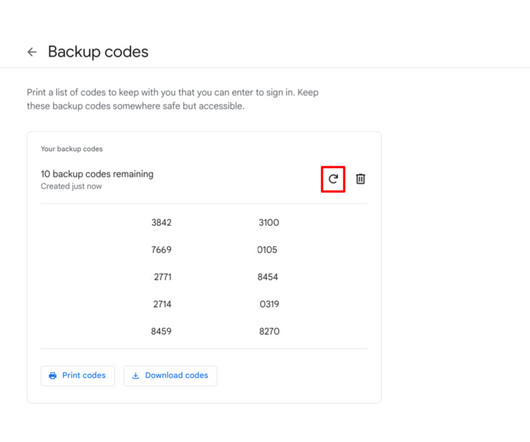
While cloud backups of OTP codes were one major piece of feedback from Google Authenticator users over the years, security researchers are asking said users to avoid enabling the new feature. At least for now, as the option is still lacking the additional protection layer that end-to-end encryption can provide.












































Let's personalize your content