Cisco issues firewall, SD-WAN security warnings
Network World
JANUARY 22, 2020
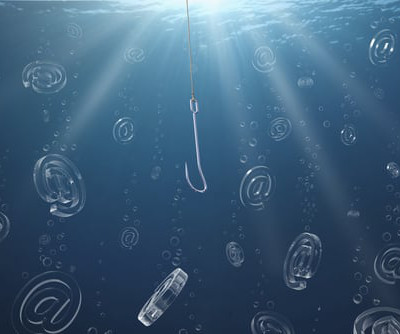
Amongst Cisco’s dump of 27 security advisories today only one was rated as critical – a vulnerability in its Firepower firewall system that could let an attacker bypass authentication and execute arbitrary actions with administrative privileges on a particular device. To read this article in full, please click here
















































Let's personalize your content