New DarkGate Malware Campaign Hits Companies Via Microsoft Teams
Tech Republic
SEPTEMBER 14, 2023
Get technical details about how this new attack campaign is delivered via Microsoft Teams and how to protect your company from this loader malware.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
JULY 6, 2023
Learn how the Meduza Stealer malware works, what it targets and how to protect your company from this cybersecurity threat. The post New Malware Targets 97 Browser Variants, 76 Crypto Wallets & 19 Password Managers appeared first on TechRepublic.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
MAY 9, 2022
The cybersecurity company says this is the first time they have seen this type of malware hiding method. The post Kaspersky uncovers fileless malware inside Windows event logs appeared first on TechRepublic.
IT Toolbox
SEPTEMBER 9, 2022
North Korean Lazarus group is targeting critical infrastructure through existing Log4j vulnerabilities and newly developed MagicRAT malware. Energy Companies appeared first on Spiceworks. The post Lazarus Hackers Exploiting Log4j Vulnerabilities to Target U.S.

Gizmodo
JANUARY 8, 2022
Using friendly-looking USB sticks as a vector for malware distribution is a trick as old as the internet itself and, apparently, it’s still quite popular with the criminals. Read more.

TechSpot
MARCH 27, 2023
Google recently suspended e-commerce giant Pinduoduo's official Play store app and warned users that several of the company's other apps contain malware. Pinduoduo's main Google Play store app (and the Apple App Store's, for that matter) is likely harmless, but Google said versions from other distribution channels are dangerous.

TechSpot
OCTOBER 1, 2021
The network security company said that in Q2 2021, 91.5% of malware arrived over an encrypted connection. It added that any company not examining encrypted HTTPS traffic at the perimeter will miss out on 9/10 of all malware. The data is derived from the firm’s own active WatchGuard Fireboxes.

Gizmodo
JANUARY 11, 2022
The world’s largest companies are grappling with increasingly widespread and sophisticated malware attacks, but an interesting new malware detection technique could help companies thwart these threats without needing any software. Read more.

CTOvision
JULY 29, 2014
Three Questions on Automated Malware Removal with Bob Gourley, Cognitio Corp and CTOVision. While there’s still an emphasis – and related spending – on malware detection, most incident response teams are actually overwhelmed by vast number of security alerts they receive. Then why haven’t more companies already embraced automation?

CTOvision
APRIL 23, 2019
HP on Tuesday announced a bevy of PC updates and new features, as well as the formal release of HP Sure Sense, the company’s new software that uses AI to prevent and block malware in near-real-time, including ransomware and previously unknown malware.
TechSpot
MARCH 14, 2023
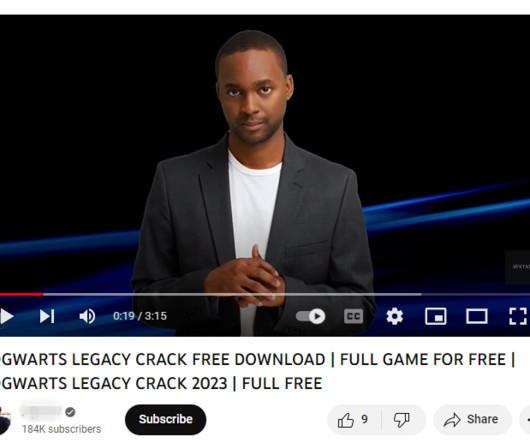
CloudSEK, a contextual AI company that predicts cyberthreats, writes that since November 2022, there has been a 200-300% month-on-month increase in YouTube videos containing links to stealer malware, including Vidar, RedLine, and Raccoon. Read Entire Article

TechSpot
SEPTEMBER 30, 2022
Chaos is a novel malware written in the Go programming language with pretty unique capabilities. Discovered and analyzed by Black Lotus Labs, the research arm of security company Lumen, the new threat can infect a plethora of computing platforms both on the software and hardware front. There are more than.

SecureWorld News
MAY 26, 2023
Security researchers at Mandiant have recently made a significant discovery in the realm of industrial control system (ICS) malware. Named "CosmicEnergy," this specialized operational technology (OT) malware poses a potential threat to critical infrastructure systems and electric grids.

CTOvision
JANUARY 23, 2019
Trojan malware attacks against business targets have rocketed in the last year, as cybercriminals alter their tactics away from short-term gain and in-your-face ransomware attacks towards more subtle, long-term campaigns with the aim of stealing information including banking information, personal data, and even intellectual property.

CTOvision
FEBRUARY 24, 2014
Signature based solutions are being bypassed by malware every day. The pervasiveness and sophistication of modern malware is damaging computers to a point where expert int. Company Security Companies' Face it, the bad guys are winning. To read more please log in. Not a member yet? We would love to have you onboard.
The Verge
AUGUST 31, 2020
Apple accidentally approved common malware disguised as an update for Adobe Flash Player to run on macOS, according to a new report. According to security researcher Patrick Wardle, Apple approved an app that contained code used by a well-known malware called Shlayer. Illustration by Alex Castro / The Verge.

SecureWorld News
JUNE 23, 2023
Army's Criminal Investigation Division (CID) is urging military personnel to be on the lookout for unsolicited, suspicious smartwatches in the mail, warning that the devices could be rigged with malware. You're compromising your personal and/or professional data with malware." Worst case? These products may also be used for Brushing.

SecureWorld News
FEBRUARY 20, 2023
Web hosting provider GoDaddy has revealed it suffered a security breach that lasted for several years, resulting in the installation of malware on its servers and the theft of source code related to some of its services. The company has attributed the campaign to a "sophisticated and organized group targeting hosting services."

Galido
MARCH 2, 2020
Information Technology Blog - - List of Latest Malware Attacks in the World - Information Technology Blog. Malware in different forms has caused serious data loss to users around the world in the last few decades. Here, we have listed the latest malware attacks in the world that you should be aware of. Ryuk Ransomware.

CTOvision
DECEMBER 30, 2019
A critical flaw has been discovered in two Citrix products, placing 80,000 companies in 158 countries at risk. The easily exploitable vulnerability could allow attackers to obtain direct access to a company’s local network and to access a company’s credentials.

SecureWorld News
NOVEMBER 4, 2022
An undisclosed media organization serving Boston, New York, Chicago, Miami, and other major cities has been hit by cybercriminals who are deploying malware on more than 250 newspaper websites, Proofpoint Threat Research reported on Twitter. This media company serves content via #Javascript to its partners.

SecureWorld News
MAY 1, 2023
Google has obtained a temporary court order to disrupt the distribution of CryptBot, a Windows-based information-stealing malware that has infected more than 670,000 computers in 2022. The harvested data is then sold to other attackers for use in data breach campaigns.

Gizmodo
JANUARY 19, 2021
On Monday, researchers announced the discovery of yet another malware strain used by foreign hackers to infiltrate a wide milieu of American government agencies and companies. SolarWinds: it’s the hack that keeps on growing. Read more.

Gizmodo
DECEMBER 1, 2021
Unpatched, years-old vulnerabilities in networking devices have allowed a noxious malware to infect thousands of AT&T customers in the U.S., a new report from a Chinese cybersecurity company claims. The malware basically functions as a backdoor, one that could allow an attacker to penetrate networks, steal data, and… Read more.

TechSpot
MARCH 22, 2022
Researchers at French mobile security company Pradeo revealed that the app, Craftsart Cartoon Photo Tools, contained a version of an Android trojan malware called Facestealer.

SecureWorld News
OCTOBER 20, 2022
Google Play has removed 16 apps from its app store after the McAfee Mobile Research Team alerted the company to Clicker malware associated with the apps, affecting 20 million people who installed the apps. Like so many mobile malware schemes, the apps profess to be helpful to users, providing a handy tool or time-saving utility.

The Verge
JULY 12, 2021
Microsoft says it’s gone door-to-door replacing routers compromised with the Trickbot malware in Brazil and Latin America, hoping to squash an international hacking group. The Daily Beast reported the detail in an article about the group, which is an ongoing target for US Cyber Command as well as information security companies like Microsoft.

CTOvision
FEBRUARY 24, 2014
Lastline Enterprise and Analyst deliver protection against targeted attacks, advanced persistent threats (APTs), zero-day exploits, and other advanced malware that bypass traditional signature-based controls and sandbox-based analysis systems. Company Security Companies' Please sign up today at CTOvision Pro.

TechSpot
MARCH 26, 2024
The company boasts that the feature allows users to ask complex and more descriptive questions, with the generative AI providing text summaries of sites and recommendations related to a user's search. Google started rolling out its Search Generative Experience (SGE) earlier this month. Read Entire Article

CTOvision
DECEMBER 30, 2020
Two months ago, researchers at US security company AdvIntel discovered that one of the Internet’s most troublesome malware platforms, Trickbot, had started testing something rather ominous: probing UEFI firmware chips […].

Network World
JULY 12, 2016
Security researchers have discovered a new malware threat that goes to great lengths to remain undetected while targeting energy companies. The goal of droppers is to prepare the field for the installation of other malware components that can perform specialized tasks. These are all tasks that Furtim’s Parent does well.

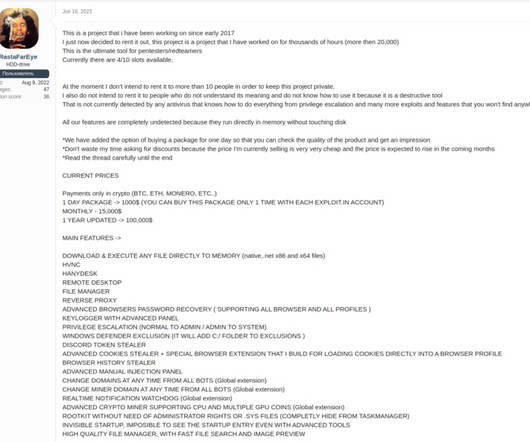
Tech Republic Security
APRIL 14, 2023
A new report from cyberthreat intelligence company Cybersixgill sees threat actors swarming to digital bazaars to collaborate, buy and sell malware and credentials. The post For cybercriminal mischief, it’s dark web vs deep web appeared first on TechRepublic.

Tech Republic Security
APRIL 22, 2024
Threats from malware, cryptographic infections and compromised networks have never been greater. Companies can’t protect their technological infrastructure, though, without a solid grasp of the actual equipment in play.

Tech Republic Security
MARCH 14, 2024
Every company’s network is made up of devices that transmit and store information. This can include internal and external systems, either company-owned or leased/rented/subscribed to. This must be done.

SecureWorld News
OCTOBER 20, 2020
But the GRU members being charged in this case started with other strains of malware and a narrow target: Ukraine's power grid. In what is commonly referred to as the most destructive and costly cyber attack ever, the conspirators unleashed the 'NotPetya' malware. The GRU's Olympic Destroyer malware. and a large U.S.

Galido
MARCH 4, 2019
Information Technology Blog - - Why Malware Prevention Should Be A Priority This Year - Information Technology Blog. What is Malware? Malware or malicious software is designed to damage or disable computers and can often cause serious damage before they are even detected. Malware prevention VS. Malware detection.

Tech Republic Security
JANUARY 24, 2023
A new study by Gartner predicts that by 2026 just 10% of companies will have zero-trust protocols in place against cybersecurity exploits. The post Companies slow to “mask up” with zero trust cybersecurity protocols appeared first on TechRepublic.

CTOvision
APRIL 22, 2020
We are tracking OPSWAT in our Guide to Technology as a Cybersecurity Company. Their goal: Eliminate malware and zero-day attacks. OPSWAT is trusted by over 1,000 organizations worldwide to protect infrastructure and reduce risk from cyber attack.

Tech Republic Security
SEPTEMBER 22, 2021
The most common targets of ransomware in the second quarter of 2021 were governmental, medical and industrial companies along with scientific and educational institutions, says Positive Technologies.

CTOvision
FEBRUARY 25, 2014
By Bob Gourley Red Owl Analytics has been named the Most Innovative Company by an august panel of highly respected judges at the RSA conference this year. The following is from the RSA conference press release : Congratulations to Red Owl Analytics for being named the Most Innovative Company at RSA Conference 2014!

Tech Republic Security
OCTOBER 7, 2022
The post 2022 State of the Threat: Ransomware is still hitting companies hard appeared first on TechRepublic. SecureWorks found that business email compromise still generates huge revenues for cybercriminals, while cyberespionage activities tend not to change so much.

The Verge
FEBRUARY 9, 2021
It’s not quite clear what’s going on here, but the prevailing theory is that the 100 million-download strong app is getting mistaken for another one with the same exact name — one that might have been a clone of ZXing’s app and one that did add malware in a recent update, according to digital security firm MalwareBytes.

Tech Republic Security
AUGUST 8, 2017
Security firm Kaspersky Lab's threat report for Q2 2017 noted that malware disguised as ransomware will likely be a big problem this year, along with attacks targeting energy companies.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content