Unleashing the Power of Cloud-Network Convergence with Smart Operation System
TM Forum
SEPTEMBER 12, 2022
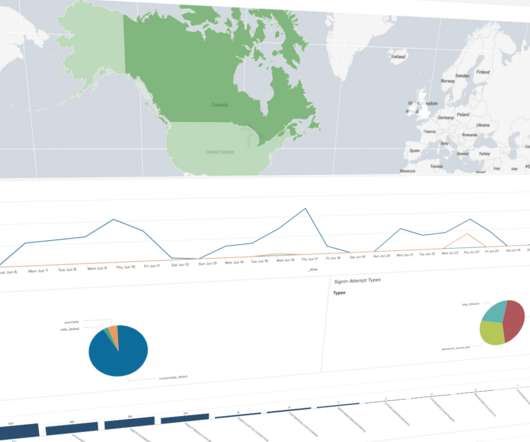
The cloud-network operation system is an important part of the cloud-network convergence architecture, and it is also the key to unlocking the value of cloud-network convergence. China Telecom pays great attention to the technical research, and continuously optimizes cloud-network intelligent and agile operation capabilities.



















































Let's personalize your content