Let’s Learn About 8 Common Cyber Security Threats. Cyber Security is a relevant topic in the technological era and one of the concerns of end users. It faces different threats that can severely affect users’ lives.
Cybersecurity is an important part of individual life, and a lack of security in the Cyber field may affect people’s personal and professional lives. Technology is growing every day; everything is digitalized. Users spend more time in their professional fields and save confidential data on devices.
The IT sector faces many cyber threats and malicious attacks. A cyber security threat is any potential danger or risk that could compromise the confidentiality, integrity, or availability of data or IT systems.
Malicious attackers try to exploit vulnerabilities to gain unauthorized access, steal sensitive information, disrupt operations, or harm individuals, organizations, or even entire nations. This blog post explains 8 Common Cyber Security Threats.
- 2024 Cybersecurity Certifications for IT Professionals
- 40% of All Incoming emails Pose a Potential Cybersecurity Threat

Learn About 8 Common Cyber Security Threats
There are different types of Cyber Security Threats that malicious actors use to steal confidential data, and users want to compromise security. The various forms of threads disrupt operations and target different aspects of digital systems and data.
| 8 Common Cyber Security Threats |
|---|
| Phishing |
| Malware |
| Denial of Service (DoS) and Distributed Denial of Service (DDoS) |
| SQL Injection |
| Cross-Site Scripting (XSS) |
| Social Engineering |
| Zero-Day (0day) Exploits |
| Credential Attacks |
1. Phishing
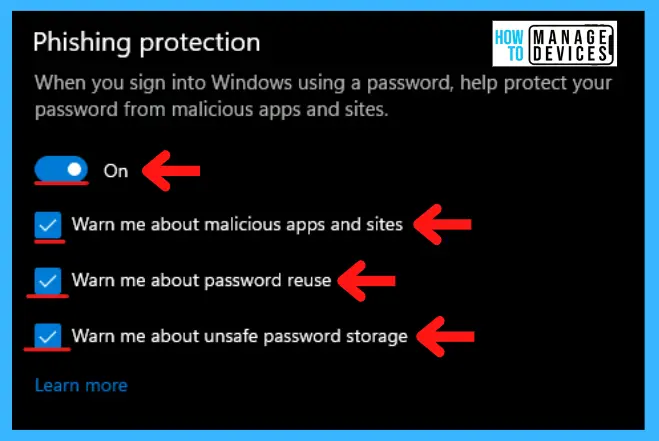
Phishing is a critical cyber security threat commonly used by malicious actors. This attack involves sending deceptive emails or messages that appear to be from an authorized source. This fraudulent practice steals sensitive information such as passwords, credit card numbers, or personal information.
Phishing can also lead victims to malicious websites or malware downloads. Some features of Phishing include Too Good To Be True, a Sense of Urgency, Hyperlink Attachments, and an Unusual Sender.
2. Malware
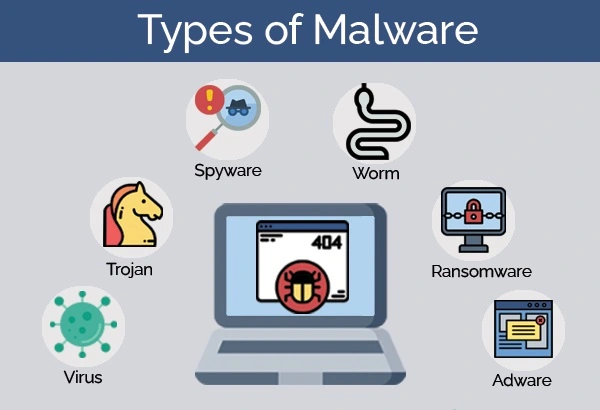
Malware (Malicious Software) is intentionally designed to cause disruptions. It can affect a computer, server, client, or computer network, leak private information, or gain unauthorized access to information or systems.
- Ransomware – It encrypts files and demands a ransom for decryption
- Trojans – Disguised as legitimate software, they give attackers unauthorized access
- Worms – It is a self-replicating programs that attach to files and spread
3. Denial of Service (DoS) and Distributed Denial of Service (DDoS)
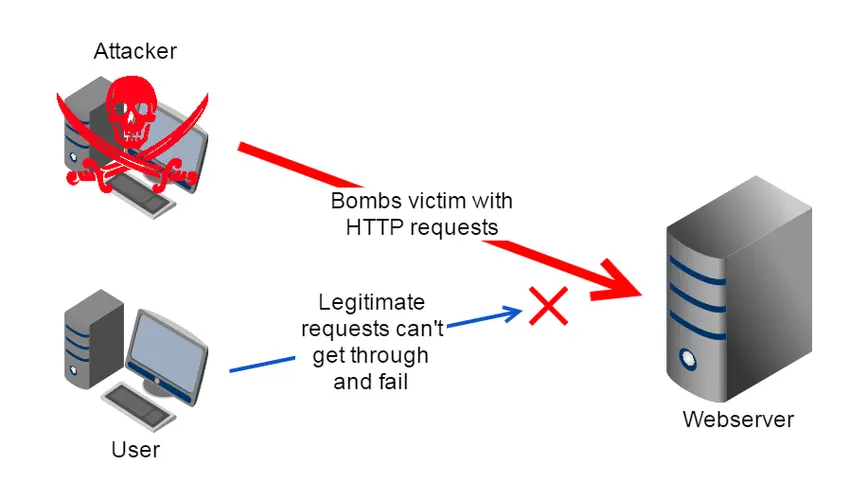
Denial-Of-Service attack floods a server with traffic, making a website or resource unavailable. In Distibuted-Denial-of-Service, use Multiple computers to attack targeted devices. There are different types of Dos Attacks, and they include Buffer Overflow, Ping of Death, SYN Flood, Teardrop, etc.
4. SQL Injection
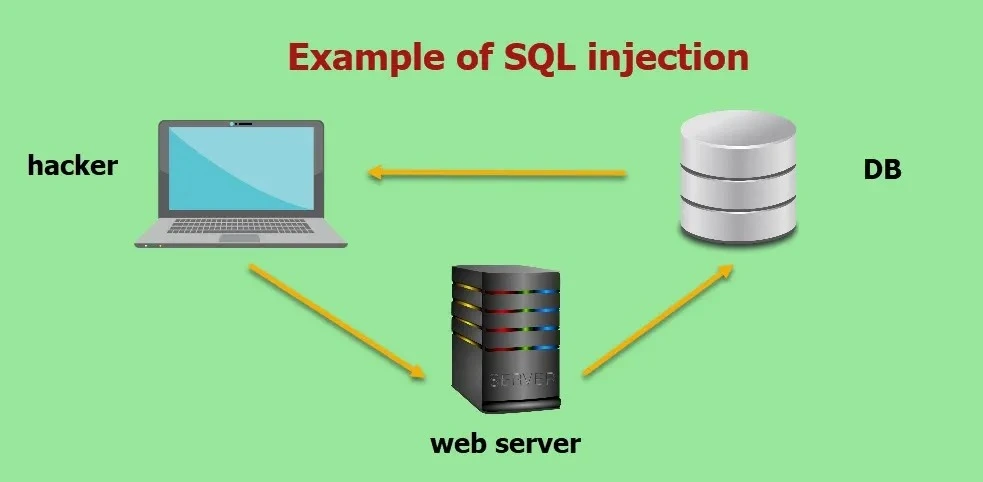
SQL Injection is a type of Cyber Security thread. It is a code injection technique used to attack data-driven applications. Attackers manipulate a web application’s input field to inject malicious SQL queries, potentially gaining unauthorized access to databases and sensitive data.
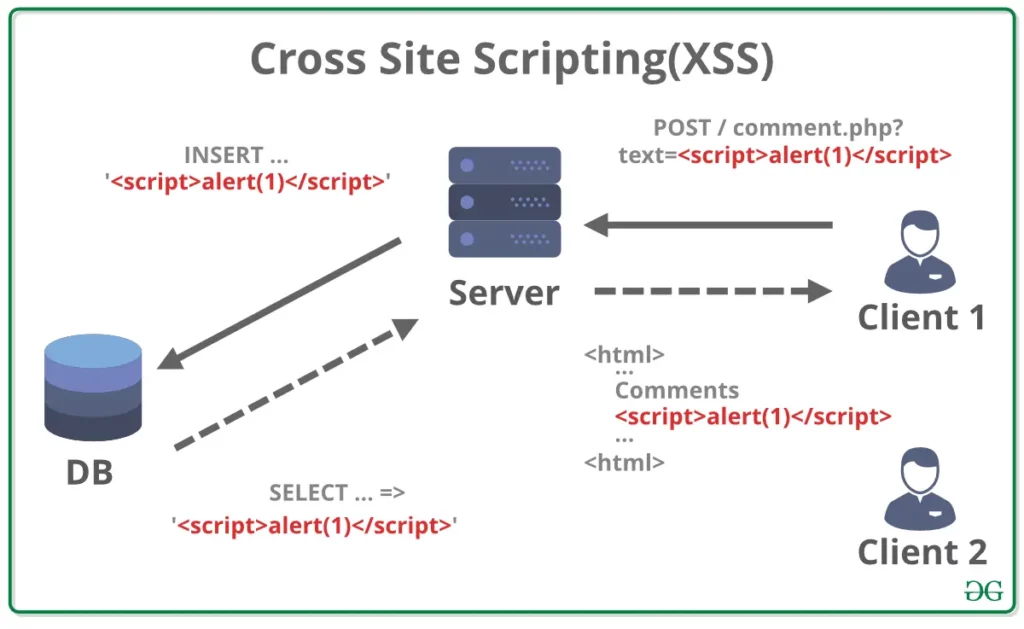
5. Cross-Site Scripting (XSS)
In Cross-site Scripting(XSS), attackers inject malicious executable scripts into the code of a trusted application or website, leading to the theft of user data. Cross-site scripting includes Capturing a user’s keystrokes, Redirecting a user to a malicious website, and Running web browser–based exploits.
6. Social Engineering
Social engineering is the psychological manipulation of individuals into divulging confidential information or performing actions that compromise security.
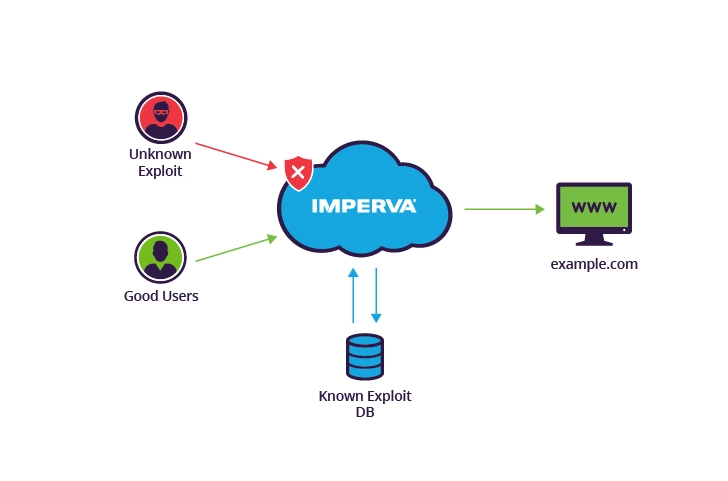
7. Zero-Day (0day) Exploits
Zero-day (0-day) Exploits target software or hardware vulnerabilities unknown to the vendor or public. Attackers focus on these vulnerabilities and take advantage of them before patches are developed. Security researchers work quickly to make a patch when a zero-day is discovered. Hence, zero days are generally short-lived.
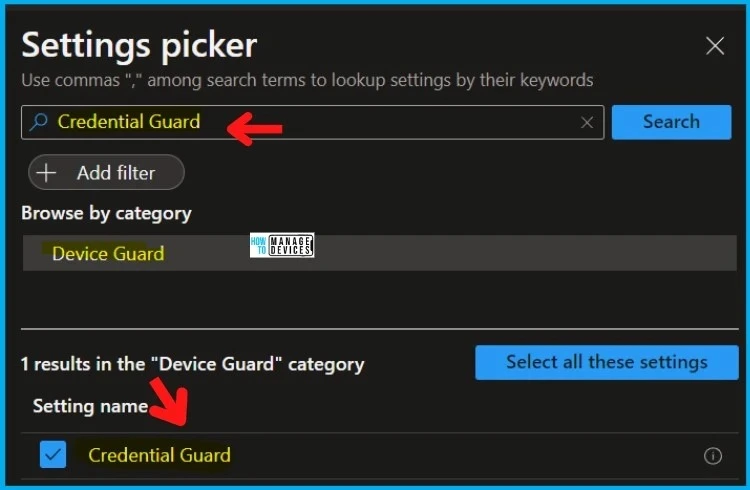
8. Credential Attacks
It is a brute force attack, where repeatedly guessed passwords and credential stuffing attacks, where stolen credentials from one site are used to attempt access on other sites.
We are on WhatsApp. To get the latest step-by-step guides and news updates, Join our Channel. Click here –HTMD WhatsApp.
Author
Gopika S Nair is a computer enthusiast. She loves writing on Windows 11 and related technologies. She is here to share quick tips and tricks with Windows 11 or Windows 10 users. She is Post Graduate Diploma Holder in Computer Science.

