Ransomware attackers are now using triple extortion tactics
Tech Republic Security
MAY 12, 2021
Attackers are not only demanding ransom from organizations, but also threatening their customers, users and other third parties.
Tech Republic Security
MAY 12, 2021
Attackers are not only demanding ransom from organizations, but also threatening their customers, users and other third parties.

Information Week
MAY 13, 2021
Not everyone has been trained to think like a data scientist or a data analyst, but they can learn to think more like one.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Forrester IT
MAY 10, 2021
I spent the early days of my career in the early 90’s studying manufacturing engineering at University then working in a ship repair yard. I was taught to weld by a gruff Geordie who handed me a visor, a live arc-welder and told me “don’t look into the light. You’ll go blind”. I didn’t. That […].

Association of Information Technology Professional
MAY 12, 2021
Ready to grow your cloud computing career or get it off to a great start? If so, check out the best cloud computing certifications today.

Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.
Anoop
MAY 13, 2021
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Read More. The post How to Improve SCCM Task Sequence Progress Bar End User Experience | ConfigMgr appeared first on HTMD Blog by Jitesh Kumar.

Information Week
MAY 10, 2021
The cloud is set to help businesses lead by outmaneuvering uncertainty. It's now imperative that they lean into the cloud and catch up with leaders before the gap becomes too large.
Information Technology Zone brings together the best content for IT professionals from the widest variety of industry thought leaders.

Tech Republic Data Center
MAY 11, 2021
A recent report on DC power revealed some interesting trends related to data center operations and power. Learn what data center conditions look like today and going forward.

Anoop
MAY 12, 2021
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Read More. The post Easy Steps to Run SCCM Task Sequence with High Performance Power Plan | ConfigMgr appeared first on HTMD Blog by Jitesh Kumar.

Tech Republic Security
MAY 11, 2021
Cybersecurity expert discusses the many ways attackers could have gotten access to the Colonial Pipeline company and reminds us why the threat always looms.

Forrester IT
MAY 13, 2021
This may be a bit of a long blog due to the extensive nature of the Executive Order On Improving The Nation’s Cybersecurity and its impact on cybersecurity and the Zero Trust approach. The Biden administration also published a “FACT SHEET: President Signs Executive Order Charting New Course to Improve the Nation’s Cybersecurity and Protect […].

Advertiser: GEP
The technological landscape is dynamic and changes quickly. And for procurement and supply chain leaders looking to harness the power of technology to navigate complex challenges and an uncertain business environment, keeping up with the latest trends can be its own obstacle. So, what’s on the technological horizon for procurement and supply chain for the year ahead?

Information Week
MAY 14, 2021
Though challenges arise when implementing a strategy to capitalize on data currency, the rewards are worth the effort. Here are six ways to unlock the value of your data.
Anoop
MAY 11, 2021
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Read More. The post Deploy Windows 10 Feature Update Using SCCM Task Sequence | ConfigMgr appeared first on HTMD Blog by Jitesh Kumar.

Tech Republic Security
MAY 12, 2021
Government and business both need to step up to combat ransomware attacks against critical systems before they spiral further out of control.
Forrester IT
MAY 10, 2021
Many companies get emotion wrong… Rather than designing experiences built on a broad spectrum of emotions, they equate emotion with delight. But real joy and real happiness can only exist in relation to all the emotions, they are a “boxed set.” We cannot just pick and choose our emotions. Anger isn’t joy, just as joy […].

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.

Tech Republic Cloud
MAY 10, 2021
The growth of hybrid cloud deployments are driving the need to bring the security and flexibility of cloud tools to data centers.
Anoop
MAY 10, 2021
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Read More. The post What’s New In SCCM Windows 10 Servicing Dashboard | ConfigMgr appeared first on HTMD Blog by Jitesh Kumar.
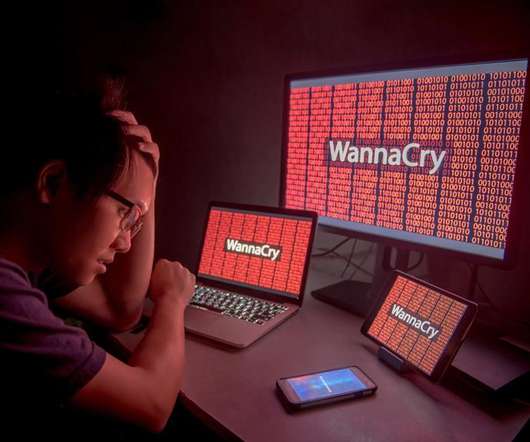
Tech Republic Security
MAY 11, 2021
Though it likes to promote itself as being "philanthropic," the DarkSide gang represents a dangerous threat to organizations around the world.

Forrester IT
MAY 12, 2021
Our society is coping with unprecedented challenges. Your customers, employees, and partners are all facing growing uncertainties and concerns, such as: income inequality and job insecurity, social unrest, and misinformation and disinformation. Meanwhile, systemic risks like climate change, pandemics, and global recessions have wrought significant health, safety, and financial impacts.

Advertisement
You’ve read the PMBOK® Guide several times, taken the certification exam for project managers, passed, and you are now a PMP®. So why do you keep making rookie mistakes? This whitepaper shows 20 of the most common mistakes that young or inexperienced project managers make, issues that can cost significant time and money. It's a good starting point for understanding how and why many PMs get themsleves into trouble, and provides guidance on the types of issues that PMs need to understand.
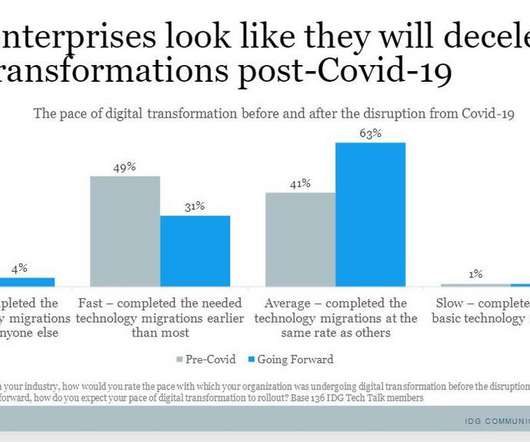
Tech Republic Cloud
MAY 11, 2021
Many enterprises will likely decelerate digital transformations post-pandemic, a new study by SAP and IDG finds.
Anoop
MAY 14, 2021
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Read More. The post What’s New Improvement with SCCM Task Sequence Check Readiness Step | ConfigMgr appeared first on HTMD Blog by Jitesh Kumar.

Tech Republic Security
MAY 10, 2021
A recent survey found an unusual reason cybersecurity is failing. Experts share what it is and how to correct it.

Forrester IT
MAY 10, 2021
While automated malware analysis and network intrusion detection systems remained in our Divest category, three more technologies joined them this year: data loss prevention, managed security service providers, and security user behavior analytics. Why is this? Because these stand-alone technologies simply don’t cut it anymore. This isn’t to say these solutions are dead, mind you.

Advertisement
“Reimagined: Building Products with Generative AI” is an extensive guide for integrating generative AI into product strategy and careers featuring over 150 real-world examples, 30 case studies, and 20+ frameworks, and endorsed by over 20 leading AI and product executives, inventors, entrepreneurs, and researchers.

Information Week
MAY 10, 2021
Accelerated moves to the cloud made sense at the height of the pandemic -- organizations may face different concerns in the future.

The Verge
MAY 13, 2021
One of the more impressive aspects of Grand Theft Auto V is how closely the game’s San Andreas approximates real-life Los Angeles and Southern California, but a new machine learning project from Intel Labs called “Enhancing Photorealism Enhancement” might take that realism in a unsettlingly photorealistic direction ( via Gizmodo ). Putting the game through the processes researchers Stephan R.
Tech Republic Security
MAY 12, 2021
A new HP Wolf Security study focuses on shifting cybersecurity threats in the age of remote working as employees use work devices for personal entertainment.

Forrester IT
MAY 10, 2021
New data from the UK Office Of National Statistics (ONS) shows that one in five adults in Britain experienced depressive symptoms in early 2021, more than double the proportion before the pandemic. Young adults are coping with a significant increase of mental health issues. Financial concerns, managing children in the household, and disabilities are some […].

Advertisement
Are you trying to decide which entity resolution capabilities you need? It can be confusing to determine which features are most important for your project. And sometimes key features are overlooked. Get the Entity Resolution Evaluation Checklist to make sure you’ve thought of everything to make your project a success! The list was created by Senzing’s team of leading entity resolution experts, based on their real-world experience.

Information Week
MAY 12, 2021
The C-suite has expanded, but will the trend continue? Likely yes, but how depends on what your company values most.

GeekWire
MAY 11, 2021
Sage Khanuja, left, and Nikolas Ioannou, the founders of Seattle-based Spira. (Spira Photo). The news: Seattle entrepreneurs Sage Khanuja , 17, and Nikolas Ioannou , 18, have sold their telemedicine startup Spira to Galileo , a New York-based healthcare company. “To be honest, I didn’t really think much or ask about their age,” Galileo CEO Tom Lee said of the teens. “I generally evaluate technology and teams based on their capabilities and potential.

Tech Republic Security
MAY 14, 2021
Old technology and fear of sharing proprietary information are keeping companies from helping each other thwart attacks.

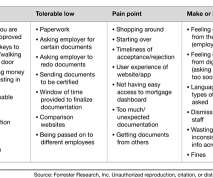
Forrester IT
MAY 12, 2021
Improving reps' productivity is one of the top objectives of our sales leader clients. The first step to achieving this is to truly understand the key productivity obstacles today’s sales teams face.

Speaker: Nicholas Zeisler, CX Strategist & Fractional CXO
The first step in a successful Customer Experience endeavor (or for that matter, any business proposition) is to find out what’s wrong. If you can’t identify it, you can’t fix it! 💡 That’s where the Voice of the Customer (VoC) comes in. Today, far too many brands do VoC simply because that’s what they think they’re supposed to do; that’s what all their competitors do.
Let's personalize your content