Scaling Cloud Security with Policy as Code
IT Toolbox
DECEMBER 5, 2022
How can enterprise scale cloud security with policy as code? The post Scaling Cloud Security with Policy as Code appeared first on.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

IT Toolbox
DECEMBER 5, 2022
How can enterprise scale cloud security with policy as code? The post Scaling Cloud Security with Policy as Code appeared first on.

Tech Republic Security
APRIL 23, 2023
PURPOSE Every enterprise needs to establish a plan of action to assess and then recover from unauthorized access to its network. This policy from TechRepublic Premium provides a foundation from which to start building your specific procedures. The post Incident response policy appeared first on TechRepublic.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
AUGUST 15, 2023
It doesn’t matter whether you are a large business enterprise, SMB, government or nonprofit, the collection, management, protection and analysis of data is a determining factor in your overall success. This policy from TechRepublic Premium establishes an enterprise-wide framework for categorizing and classifying.

Tech Republic Security
DECEMBER 12, 2022
All modern enterprises must accept the fact that at some point their systems or networks will very likely experience an unauthorized intrusion of some kind. This is the state of the world’s current security environment and for the most part enterprises, especially well-managed ones, have come to terms with this fate while also doing their.
Advertisement
Data fuels the modern enterprise — today more than ever, businesses compete on their ability to turn big data into essential business insights. Increasingly, enterprises are leveraging cloud data lakes as the platform used to store data for analytics, combined with various compute engines for processing that data.

Tech Republic Security
FEBRUARY 2, 2023
This policy outlines the appropriate auditing and logging procedures for computer systems, networks and devices that store or transport critical data. From the policy: Many computer systems, network devices and other technological hardware used in the enterprise can audit and log various.

TechSpot
MARCH 12, 2024
As per Microsoft policy, Windows 10 will soon reach an important milestone in its release history. Version 21H2 of Windows 10 Enterprise and Education reaches the end of life (EoL) on June 11, 2024. Organizations must upgrade to the latest version to keep receiving security updates through the Windows Update service.

CIO Business Intelligence
DECEMBER 18, 2023
Over the summer, I wrote a column about how CIOs are worried about the informal rise of generative AI in the enterprise. Since then, many CIOs I’ve spoken with have grappled with enterprise data security and privacy issues around AI usage in their companies. That column may have been the understatement of the year.
CIO Business Intelligence
OCTOBER 25, 2023
From IT, to finance, marketing, engineering, and more, AI advances are causing enterprises to re-evaluate their traditional approaches to unlock the transformative potential of AI. What can enterprises learn from these trends, and what future enterprise developments can we expect around generative AI?

Tech Republic Security
MARCH 1, 2024
The US National Institute of Standards and Technology's framework defines federal policy, but it can be used by private enterprises, too. Here's what you need to know.

Network World
AUGUST 24, 2023
Cisco and Kyndryl have expanded their partnership to offer new services that are aimed at helping enterprise customers better detect and respond to cyber threats. It features a unified dashboard, support for flexible trust policies, and open APIs to encourage third-party integrators.

Anoop
MARCH 28, 2018
There are many discussions happening whether CSP can replace Group policy (GP). The post Windows 10 MDM CSP Policies Override Group Policy Settings appeared first on SCCM Intune Real World Enterprise Experience Blog by Vimal Das. By default, GP have higher precedence over CSP when there is a setting conflict.

CTOvision
OCTOBER 27, 2020
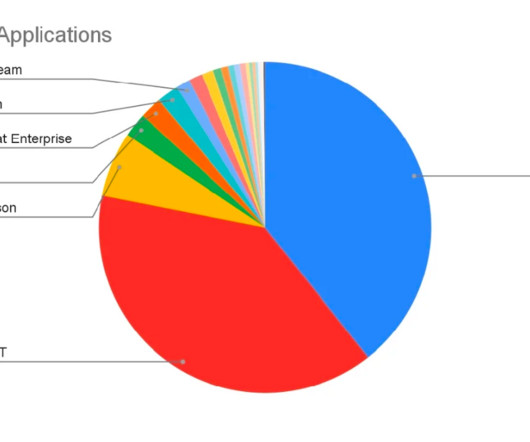
Today, enterprises are increasingly turning to Next-Generation Firewall (NGFW) features with the goal of moving toward a more proactive user and application-aware approach to enterprise security. A long-term Palo Alto […].

Tech Republic Security
JANUARY 16, 2024
Data in transit means data is at risk if the proper precautions aren’t followed. Data stored inside a securely monitored environment is much less likely to fall into the wrong hands than data exchanged between people and systems. With this in mind, it is essential for company personnel to adhere to firm and clear guidelines.
CIO Business Intelligence
OCTOBER 10, 2023
So, what are its implications for the enterprise and cybersecurity? It is a scientific and engineering game-changer for the enterprise. But the shock of how fast Generative AI applications such as ChatGPT , Bard , and GitHub Pilot emerged seemingly overnight has understandably taken enterprise IT leaders by surprise.

Tech Republic Security
FEBRUARY 23, 2023
The post Transmission of sensitive data policy appeared first on TechRepublic. Data stored inside a securely monitored environment is much less likely to fall into the wrong hands than data exchanged between people and systems. With this in mind, it is essential for company personnel to adhere to firm and clear guidelines.

Computerworld Vertical IT
AUGUST 31, 2022
There's yet more news from the ever-effervescent Apple-in-the-enterprise space , as Apple device management company Addigy has introduced a new tool called Flex Policies. Making policies remote, automated, and easier.

TM Forum
OCTOBER 14, 2021
This Catalyst explores how communication service providers (CSPs) can offer enterprises guaranteed and differentiated 5G connectivity services – with the security, data sovereignty and control that enterprises need to move more mission critical workloads onto the CSP’s 5G network.

CIO Business Intelligence
APRIL 14, 2023
Here are ways to get a better grasp of what these systems are capable of, and utilize them to construct an effective corporate use policy for your organization. With this in mind, here are six best practices to develop a corporate use policy for generative AI. For example, will this cover all forms of AI or just generative AI?

Venture Beast
DECEMBER 21, 2021
PlainID has raised $75 million to expand its access policy management platform that providers simplified identity security for enterprises. Read More.

TechSpot
JULY 23, 2022
David Weston, Microsoft's VP of Security and Enterprise, announced the news via Twitter earlier this week. According to Weston, the lockout policy is designed to mitigate Remote Desktop Protocol (RDP) and other brute force attack vectors. The new feature is available on Windows 11 Insider Preview builds 22528.1000 and newer.

Anoop
APRIL 30, 2018
In my previous post (Group policy Vs Intune Policy), we discussed Intune policy wins over GP when there is a policy conflict. The post Group Policy Vs Intune Policy after Intune unenrollement appeared first on SCCM Intune Real World Enterprise Experience Blog by Vimal Das.
TM Forum
OCTOBER 15, 2021
This Catalyst explores how communication service providers (CSPs) can offer enterprises guaranteed and differentiated 5G connectivity services – with the security, data sovereignty and control that enterprises need to move more mission critical workloads onto the CSP’s 5G network.

Tech Republic Security
AUGUST 8, 2023
The EU General Data Protection Regulation is a comprehensive set of rules designed to keep the personal data of all EU citizens collected by any organization, enterprise or business safe from unauthorized access or use. The GDPR went into effect on May 25, 2018, and the provisions in the law greatly affected the manner in.

CIO Business Intelligence
MARCH 18, 2024
Workload IAM transforms enterprise security by securing workload-to-workload access through policy-driven, identity-based, and secretless access controls, moving away from the legacy unmanaged, secrets-based approach. See more here. The CrowdStrike Falcon platform is rapidly becoming the center of cybersecurity’s ecosystem.

CIO Business Intelligence
AUGUST 30, 2023
Now, generative AI use has infiltrated the enterprise with tools and platforms like OpenAI’s ChatGPT / DALL-E, Anthropic’s Claude.ai, Stable Diffusion, and others in ways both expected and unexpected. In my next article, I’ll share some processes to manage and remediate the use of generative AI in enterprise organizations. Stay tuned!

Tech Republic
OCTOBER 11, 2023
The purpose of this policy from TechRepublic Premium is to provide guidelines for the appropriate application of.

CIO Business Intelligence
OCTOBER 4, 2023
The enterprise edge has become a growing area of innovation as organizations increasingly understand that not every workload — particularly new edge workloads — can move to the cloud. Generating business value from this data will require significant growth in edge computing deployments.
CIO Business Intelligence
JULY 5, 2023
Considering how many organizations now follow a hybrid work model, it’s time for the enterprise browser to offer that same experience, allowing individuals to easily navigate their tasks whether they’re on their laptop at the office or checking email on their mobile device at home.

Computerworld Vertical IT
AUGUST 3, 2021
Microsoft last week said the most important Windows policies enterprises can set to speed up Windows servicing are those configuring deadlines. Setting Compliance Deadlines is the most important policy that every enterprise who cares about achieving reliable update velocity should set," the Redmond, Wash.

CIO Business Intelligence
NOVEMBER 14, 2023
The Internet of Things (IoT) is a permanent fixture for consumers and enterprises as the world becomes more and more interconnected. In this article, we’ll explore the risks associated with IoT and OT connectivity and the measures that organizations need to take to safeguard enterprise networks. billion devices reported in 2023.

CIO Business Intelligence
JULY 5, 2023
Generative AI is potentially the most transformative new technology since the introduction of the public internet, and it already has many exciting applications within enterprise service management (ESM). Each company, for example, has its own policy for employee password renewal, making it difficult to nail down a universal standard.

CIO Business Intelligence
NOVEMBER 23, 2022
Enterprise architecture definition Enterprise architecture (EA) is the practice of analyzing, designing, planning, and implementing enterprise analysis to successfully execute on business strategies. Another main priority with EA is agility and ensuring that your EA strategy has a strong focus on agility and agile adoption.

Forrester IT
JANUARY 29, 2021
The recent uproar about WhatsApp’s changes to its privacy policy is a good reminder of that fact. While the changes had implications for consumers who use WhatsApp, the concerns also made their way into the enterprise.

CIO Business Intelligence
MARCH 8, 2023
Firstly, digital businesses embrace a digital-first enterprise strategy led by the CEO and other C-suite executives. More and more businesses today have taken root in a digital business model to serve as their stepping stone towards becoming Future Enterprises. But what does it mean to be a digital business? Maria Beatriz A.

CIO Business Intelligence
NOVEMBER 22, 2022
Every enterprise needs a data strategy that clearly defines the technologies, processes, people, and rules needed to safely and securely manage its information assets and practices. Guan believes that having the ability to harness data is non-negotiable in today’s business environment.

Information Week
OCTOBER 12, 2021
In a world awash with data, it's important to keep important enterprise records safe, secure, and organized

SecureWorld News
JANUARY 31, 2024
All stakeholders, including insurers, need to understand whose cyber insurance policy responds to an incident. Even worse, boilerplate contractual liability exclusions within most cyber insurance policies will exclude coverage for special purpose vehicles or other interested parties.

CIO Business Intelligence
AUGUST 5, 2022
A vast majority of enterprises globally are overspending in the cloud, according to a new HashiCorp-Forrester report. The report showed that a majority of enterprises surveyed were already using multicloud infrastructures. Multicloud infrastructure works for most enterprises.

Venture Beast
MAY 18, 2021
Styra, a company developing a platform for container policy management, has raised $40 million in venture funding. Read More.

Computer Weekly
SEPTEMBER 8, 2016
With IoT devices set to outnumber notebooks, smartphones and tablets by more than three times, businesses will need to adjust their network access policies to keep things running smoothly, says Gartner

SecureWorld News
MAY 1, 2022
These are the threats workers may face and what enterprises can do to protect them. Scams, device theft, interception of itineraries from enterprise travel security platforms, and physical safety threats are all potential risks. They may also provide a hacker with confidential information or access to the enterprise network.

Venture Beast
AUGUST 23, 2021
Small and medium-sized enterprises (SMEs) are continuing to adjust their policies as new COVID-19 cases surge due to the Delta variant. Read More.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content