CISOs Tackle Compliance With Cyber Guidelines
Information Week
MARCH 6, 2024
The more information chief information security officers can uncover about their security and tech stack, the better off they will be.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Information Week
MARCH 6, 2024
The more information chief information security officers can uncover about their security and tech stack, the better off they will be.

Tech Republic Security
JANUARY 23, 2024
This policy from TechRepublic Premium provides guidelines for the reporting of information security incidents by company employees. From the policy: STEPS TO TAKE IF YOU SUSPECT AN INFORMATION SECURITY.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
MARCH 23, 2023
PURPOSE These guidelines from TechRepublic Premium will help you define the necessary ingredients of a security policy and assist in its proper construction. Using this information, your business can establish new policies or elaborate on those. Using this information, your business can establish new policies or elaborate on those.

SecureWorld News
NOVEMBER 27, 2023
In a significant step forward to safeguard the digital landscape, the United States Cybersecurity and Infrastructure Security Agency (CISA) and the United Kingdom National Cyber Security Centre (NCSC) have jointly released the Guidelines for Secure AI System Development.

Tech Republic Security
APRIL 26, 2023
PURPOSE This policy from TechRepublic Premium provides guidelines for the reporting of information security incidents by company employees. From the policy: POLICY DETAILS An information security incident is defined. From the policy: POLICY DETAILS An information security incident is defined.

ForAllSecure
JANUARY 31, 2023
Cyber Security Guidelines The updated FFIEC Cybersecurity Guidelines are voluntary programs and actionable initiatives that are designed to help financial institutions and their service providers protect the security, confidentiality, and integrity of customer information in an increasingly interconnected digital world.

SecureWorld News
NOVEMBER 1, 2022
government agencies have come together to provide some guidelines in protecting against these attacks. The advisory also includes detailed information on what your organization should do if you believe you are experiencing a DDoS attack, as well what to do after an attack. Which is why some U.S.

CIO Business Intelligence
OCTOBER 11, 2022
For example, academic institutions must comply with strict guidelines for the retention of research data for anywhere from ten to thirty years. With decades or even centuries of information to steward, how can academic institutions preserve this content for future generations? Information may be degrading because of how it is stored.

Information Week
JULY 15, 2022
Fundamentals of operationalizing artificial intelligence help companies chart a course for early wins.
The Verge
JUNE 7, 2021
Providing verifiable information to Apple and customers is critical to customer trust. The information you provide must be truthful, relevant, and up-to-date so that Apple and customers understand who they are engaging with and can contact you regarding any issues. Illustration by William Joel / The Verge. Developer Identity.

Information Week
JANUARY 18, 2024
By following these guidelines, manufacturers can uplevel their security stance, protect their investments and take meaningful steps toward establishing a robust cybersecurity strategy.

Venture Beast
MAY 8, 2022
DAOs can be informative in guiding how to govern AI-driven systems based on community decisions rather than centralized authorities. Read More.

Tech Republic Security
AUGUST 7, 2023
It can provide peace of mind that communications will not be intercepted and that sensitive information stored on devices can’t be exfiltrated in the event of loss or theft. This policy from TechRepublic Premium provides guidelines for adopting encryption technologies for organizational.

Information Week
DECEMBER 1, 2023
18 nations have signed on to the new non-binding 'Guidelines for Secure AI System Development,' but, without enforcement, will it make an impact?
Tech Republic Security
MARCH 15, 2023
PURPOSE The purpose of this policy is to provide guidelines for the appropriate disposal of information and the destruction of electronic media, which is defined as any storage device used to hold company information including, but not limited to, hard disks, magnetic tapes, compact discs, audio or videotapes, and removable storage devices such as (..)

Tech Republic Security
JANUARY 31, 2023
However, that access entails risk, including exposure of confidential information and interruption in essential business services. This policy from TechRepublic Premium offers guidelines for governing access to critical systems and confidential data. From the policy: SUMMARY IT.

Galido
MARCH 11, 2017
Before discussing the guidelines to find the best offshore software development company, let’s discuss briefly the reasons to outsource. To simplify the process, here we explain some easy-to-follow guidelines which can help in selecting the right outsourcing partner. Outsourcing to can reduce overall IT project cost to almost 30-40%.

Future of CIO
OCTOBER 16, 2019
A good information strategy guides the company forward by determining the strategic objective of information management, identifying and assessing risks and adjusting the business speed, to maximize business benefit. With overwhelming growth of data, information and its life cycle become much more complex.

Information Week
AUGUST 7, 2019
You don't need to come up with an AI ethics framework out of thin air. Here are five of the best resources to get technology and ethics leaders started.

CTOvision
NOVEMBER 13, 2013
The following exciting information is from: [link]. Defense Information Systems Agency Mobility Management for U.S. “It gives us the ability to move information wherever we need it and put the information in the hands of the warfighter wherever he or she might be. Department of Defense. n June 2013, the U.S.

Tech Republic Security
MARCH 16, 2023
This policy from TechRepublic Premium provides guidelines for the appropriate use of electronic communications.

Information Week
APRIL 18, 2023
In a world already flooded with misinformation, businesses eye ethical use guidelines to implement generative artificial intelligence technologies more responsibly.

TechSpot
MARCH 24, 2021
Apple recently updated its security guidelines for its manufacturing partners to cut down on the number of leaks. Ironically, the news comes from an internal document leaked to The Information.

Information Week
JANUARY 24, 2022
Guidelines are great -- but they need to be enforced. An ethics board is one way to ensure these principles are woven into product development and uses of internal data.

SecureWorld News
APRIL 4, 2024
Clear guidelines on how company's information and IP assets can and cannot be utilized with AI systems are essential. Reinforcing access controls can prevent unauthorized use of IP, a crucial measure given the ease with which GenAI can disseminate information.

Information Week
MARCH 14, 2023
Private sector, voluntary guidelines on the ethical use of generative AI are emerging, yet no US government body regulates the technology currently.

SecureWorld News
FEBRUARY 17, 2024
Cybercriminals often attack medical devices and networks to access highly sensitive information, including personal and protected health data. They often exploit this information by demanding ransom or selling it on the Dark Web. Vulnerabilities in medical devices present significant risks, expanding the potential for breaches.

Tech Republic Cloud
NOVEMBER 22, 2022
This policy provides guidelines for secure and effective cloud computing operations to ensure the integrity and privacy of company-owned information. Gains in business continuity are an especially noteworthy.

Computer Weekly
OCTOBER 25, 2017
UK’s intelligence services lack adequate oversight and written guidelines when sharing databases of sensitive information, Privacy International argues in secret court

Information Week
JANUARY 20, 2021
IT leaders must step in with guidelines about when to develop applications using low code and no code, and when it's necessary to develop in a full-code mode.

Kitaboo
SEPTEMBER 19, 2022
Web Content Accessibility Guidelines (WCAG), first published on 9 May 1999 by the Worldwide Consortium (W3C), are part of a series of Web Accessibility Initiatives (WAI). A total of 9 new guidelines have been introduced, categorized under the existing three levels. Four New Guidelines under Level AA. 3.2.6 – Consistent Help.

SecureWorld News
JULY 19, 2023
By implementing voluntary guidelines and labeling certified products, the U.S. By applying the program's shield logo to certified devices, consumers will be able to identify and choose products that meet the program's cybersecurity guidelines.

Kitaboo
DECEMBER 28, 2023
Publication ethics are the rules of conduct, ethical standards, policies, and guidelines typically agreed upon between various stakeholders when publishing results of research or other scholarly work in general. Having said that, there are several considerations that you need to take into account to maintain ethical publication guidelines.

Kitaboo
MARCH 17, 2023
Today, it can apply to almost anything including product design, activities, information exchanges and so on. You could have learners, who you have no prior information about, sitting at the other end of the globe. They face many barriers, including decreased access to information and a lack of job opportunities.

Information Week
DECEMBER 1, 2021
Here are some guidelines that I recommend. I’ve spent most of my career applying machine learning and natural language processing to solve problems for users and businesses.

CIO Business Intelligence
AUGUST 5, 2022
The regulations streamline how entities who handle customer banking information will secure their systems and share details within protected application program interfaces. The Operational Guidelines for Open Banking in Nigeria published by the CBN stress that customer data security is critical for the safety of the open banking model.
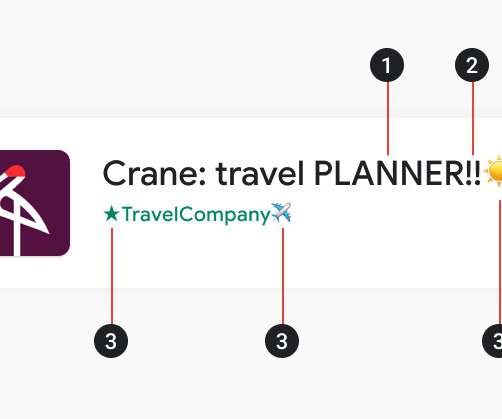
The Verge
APRIL 30, 2021
Google has announced new Play Store policies and guidelines designed to make app listings more succinct, accurate, and less of an eyesore. Separately, the new guidelines about app preview assets will come into effect in the second half of the year. An example of the kind of listing that will be prohibited under the new policy.

SecureWorld News
AUGUST 30, 2023
The proposed bill would require the Office of Management and Budget (OMB) to update the Federal Acquisition Regulation (FAR) to require federal contractors to implement VDPs that are consistent with the guidelines of the National Institute of Standards and Technology (NIST). Mittal will be presenting on "How Deep Are We in These Fakes?

Anoop
JUNE 27, 2018
I will provide more information about “SCCM Educational post series” in upcoming posts. In case you are a newbie to SCCM then this is the important guidelines for you. This is my first post on SCCM Educational post series. The details of SCCM Console nodes or buttons will give you an overall idea UI capabilities. […].

Kitaboo
DECEMBER 22, 2023
For instance, if a series of articles uses the same headings, font styles, and paragraph spacing, readers can quickly navigate and digest the information. Consistent guidelines on style, tone, and format reduce the time spent on revisions and ensure uniform quality. This approach is supported by a commitment to high-quality editing.
SecureWorld News
MARCH 28, 2024
As the attack surface has shifted to vulnerabilities in IoT, OT, and industrial control systems, CIRCIA acts as an accelerant to cross-industry information sharing." While some argued for shorter timelines, CISA aims to balance rapid reporting with allowing victims sufficient time for initial response and accurate information gathering.

Tech Republic Big Data
MAY 30, 2023
The purpose of this policy from TechRepublic Premium is to provide guidelines for the appropriate retention and disposal of physical and electronic documents.

GeekWire
JULY 27, 2021
This comes in addition to the previously announced safety guidelines, which include a reduced capacity for the show and mandatory face masks inside the building for all attendees. Attendees of the upcoming gaming convention, scheduled to be held as an in-person event on Sept. ” Those have apparently been surmounted.

IT Toolbox
OCTOBER 9, 2017
Information technology is rapidly changing the production guidelines mapped out by decades of mass production. With the emergence of ERP, resource management and all assignments related to project management invariably fall under the purview of IT departments.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content