Webroot vs. Symantec: Endpoint security software comparison
Tech Republic Security
MARCH 15, 2022
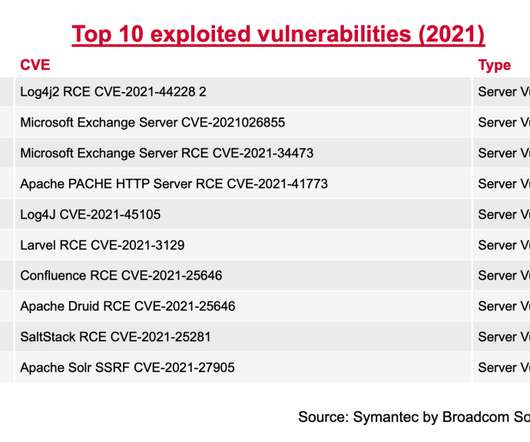
Symantec Endpoint Protection and Webroot Internet Security Plus 2022 are compelling security products intended to protect business systems. Learn the pros and cons of each security solution to make the best possible choice.






































Let's personalize your content