Androxgh0st Malware Botnet Steals AWS, Microsoft Credentials and More
Tech Republic Security
JANUARY 18, 2024
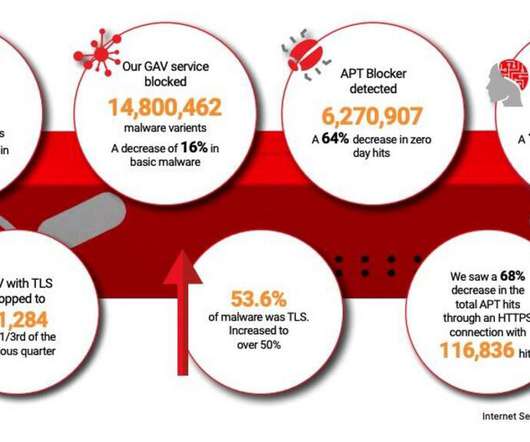
The Androxgh0st malware botnet is used for victim identification and exploitation in targeted networks, as well as credentials collection. Read the FBI/CISA's tips for protecting against this malware threat.
















































Let's personalize your content