Where’s The Value In Open Source?
Forrester IT
OCTOBER 9, 2019
In a brand-new stream of research, VP and principal analyst James Staten and I will be taking a close look at open source software (OSS) as a strategy for modern businesses.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Forrester IT
OCTOBER 9, 2019
In a brand-new stream of research, VP and principal analyst James Staten and I will be taking a close look at open source software (OSS) as a strategy for modern businesses.

CIO Business Intelligence
NOVEMBER 13, 2023
Open source has seen a great deal of momentum among mainframers, making collaboration easier and providing greater transparency. But for all of its benefits, open source is not without risks. By its very nature, open-source code is accessible to whoever wants to see it—including potential attackers.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CTOvision
JUNE 10, 2020
The number of open source software (OSS) vulnerabilities more than doubled in 2019 compared with 2018, a new RiskSense report has shown. Total common vulnerabilities and exposures vulnerabilities (CVEs) reached […].

Tech Republic
MARCH 3, 2023
Many software companies rely on open-source code but lack consistency in how they measure and handle risks and vulnerabilities associated with open-source software, according to a new report. The post Top 10 open-source security and operational risks of 2023 appeared first on TechRepublic.
Dataconomy
MARCH 26, 2024
Runa Capital’s ROSS Index highlights the growing market for AI and open-source technologies, tracking the rapid expansion of this sector. These efforts showcase the diverse, evolving nature of AI and open-source ventures. This convergence of trends is a key focus of the report.
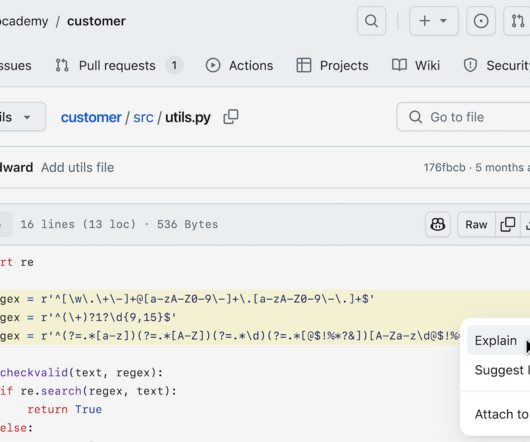
Tech Republic Security
NOVEMBER 10, 2023
GitHub Advanced Security gains some AI features, and GitHub Copilot now includes a chatbot option. Github Copilot Enterprise is expected in February 2024.

Venture Beast
APRIL 12, 2022
Results point to a clear desire for license cost savings, code portability and strong community backing offered by open source technologies. Read More.

Venture Beast
SEPTEMBER 6, 2021
A new report commissioned by the EC sheds light on the potential impact of open source software and hardware on Europe's economy. Read More.
Venture Beast
MARCH 2, 2021
Enterprises continued to embrace open source software through the pandemic, according to a new Red Hat report. Read More.

Venture Beast
MARCH 4, 2022
More companies will continue to bring more products to market based on open source tools because of the broad and strategic benefits. Read More.

The Verge
JANUARY 9, 2022
A developer appears to have purposefully corrupted a pair of open-source libraries on GitHub and software registry npm — “ faker.js ” and “ colors.js ” — that thousands of users depend on, rendering any project that contains these libraries useless, as reported by Bleeping Computer. Illustration by Alex Castro / The Verge.

Venture Beast
JUNE 19, 2021
91% of software developers expect open source to be a part of their organizations in years to come, accourding to a recent Aiven survey. Read More.

SecureWorld News
DECEMBER 15, 2022
Security researchers at Checkmarx and Illustria recently discovered a campaign in which a threat actor(s) managed to post over 144,000 phishing packages to popular open source platforms, including NPM, PyPi, and NuGet. For more information, see the full report, How 140K Nuget, NPM, and PyPi Packages Were Used to Spread Phishing Links.

Tech Republic Security
MAY 20, 2020
Problems are everywhere, but most fixes are easy to find and implement, according to a Veracode report that analyzed.
Venture Beast
APRIL 13, 2021
Vulnerabilities in open source codebases increased by nine percentage points in 2020, according to a new report from Synopsys and Black Duck. Read More.
SecureWorld News
FEBRUARY 10, 2021
Google recently launched the 'OSV' (Open Source Vulnerabilities) database, as a " first step towards improving vulnerability triage for developers and consumers of open source software.". This will help consumers of open source software determine if they were impacted and make the appropriate security changes.

Venture Beast
SEPTEMBER 29, 2021
This change is likely due to the prevalence of open source components in new software and rising attacks using open projects as vectors. Read More.

Tech Republic Security
MARCH 2, 2021
A new Red Hat report also finds that app development and digital transformation are important to users and that security perceptions have improved.

IT Toolbox
MARCH 24, 2023
A malicious, open-source ChatGPT extension for Chrome has been reported to steal key details of approximately 9,000 Facebook accounts. The post Malicious ChatGPT Extension Hijacks Facebook Accounts appeared first on Spiceworks.

The Verge
MARCH 8, 2022
Google’s Jigsaw unit is releasing the code for an open source anti-harassment tool called Harassment Manager. It’s debuting as source code for developers to build on, then being launched as a functional application for Thomson Reuters Foundation journalists in June. Illustration by Alex Castro / The Verge.

Tech Republic Security
APRIL 24, 2024
A new report by cyber security firm Radware identifies the four main impacts of AI on the threat landscape emerging this year.

Network World
FEBRUARY 8, 2017
Open source software is the norm these days rather than the exception. Discover how to secure your systems with InfoWorld's Security Report newsletter. ]. Discover how to secure your systems with InfoWorld's Security Report newsletter. ]. InfoWorld: Why is Red Hat getting on the soapbox about open source security?

CTOvision
MAY 9, 2014
Now for more on their assessment: Recorded Future reported that: Since 2007, Al-Qaeda’s use of encryption technology has been based on the Mujahideen Secrets platform which has developed to include support for mobile, instant messaging, and Macs.

CTOvision
JANUARY 25, 2016
invited to participate in its January 2016 report entitled "The Forrester Wave TM : Big Data Hadoop Distributions, Q1 2016." It was noted in the Forrester Report that, "Hortonworks doubles-down on inclusive, broad community innovation. Hortonworks is a rock when it comes to its promise to offer a 100% open source distribution.

CIO Business Intelligence
APRIL 12, 2024
According to a report from Indeed , a large part of this shift has come as organizations focus more on adopting AI in the workplace. Even as the IT job market experiences shifting dynamics, employment website Indeed reports a range of roles have maintained resiliency and even grown in demand.

Forrester IT
MAY 4, 2020
In my new report, “The State Of Application Security, 2020,” some of the trends are. Applications remain the most popular attack vector, open source continues to infect everything, and too many industries are not investing in the application security controls they need. kind of discouraging.

Network World
MARCH 3, 2017
HackerOne, the company behind one of the most popular vulnerability coordination and bug bounty platforms, has decided to make its professional service available to open-source projects for free. Here at HackerOne, open source runs through our veins," the company's representatives said in a blog post.
ForAllSecure
JANUARY 28, 2020
In recent articles, ForAllSecure has discussed how we were able to use our next-generation fuzzing solution, Mayhem, to discover previously unknown vulnerabilities in several open source projects, including Netflix DIAL reference , Das U-Boot , and more. allows an attacker to cause a denial of service via a crafted PSD file.

Network World
MAY 19, 2022
Nmap, short for Network Mapper, is a free and open source tool used for vulnerability checking, port scanning and, of course, network mapping. Despite being created back in 1997, Nmap remains the gold standard against which all other similar tools , either commercial or open source, are judged.

Venture Beast
APRIL 26, 2022
Based on recent adoption trends, it's clear the original open sourcing of Java has set the language on a path to a more user-friendly future. Read More.

Venture Beast
APRIL 29, 2022
Log4shell, a humble piece of open-source software, quickly became the worry of IT teams as they scrambled to protect critical data. Read More.

Network World
AUGUST 31, 2016
The Department of Defense needs to move past open source myths that have been debunked and jump on the open source bandwagon or the DoD and U.S. military will not be able to maintain tech superiority, warns a Center for a New American Security (CNAS) report.

SecureWorld News
JULY 14, 2022
The Department of Homeland Security's (DHS) Cyber Safety Review Board (CSRB) has released its first report , providing detailed information on the Log4j vulnerability. Organizations should continue to report (and escalate) observations of Log4j exploitation. Increase investments in open source software security.
ForAllSecure
JANUARY 28, 2020
In recent articles, ForAllSecure has discussed how we were able to use our next-generation fuzzing solution, Mayhem, to discover previously unknown vulnerabilities in several open source projects, including Netflix DIAL reference , Das U-Boot , and more. allows an attacker to cause a denial of service via a crafted PSD file.
ForAllSecure
JANUARY 28, 2020
In recent articles, ForAllSecure has discussed how we were able to use our next-generation fuzzing solution, Mayhem, to discover previously unknown vulnerabilities in several open source projects, including Netflix DIAL reference , Das U-Boot , and more. allows an attacker to cause a denial of service via a crafted PSD file.

Computer Weekly
NOVEMBER 6, 2017
Reports by 451 Research and the OpenStack Foundation suggest enterprise use of the open cloud platform is on the rise, as issues around installation and upgrades are addressed by the developer community
CIO Business Intelligence
APRIL 24, 2024
Thus, it’s important to assess whether your organization is set up to handle the continuous expansion of the open-source ecosystem and an ever-growing array of tools to incorporate into your supply chain. Here, you’ll find a high-level synopsis of the report’s key findings and recommendations. Read the full report.

The Verge
MAY 29, 2021
US soldiers stationed in Europe may have accidentally exposed information about the United States’ nuclear weapons stockpile when they used flashcard apps to help them remember details about the information, according to a report from open-source intelligence outlet Bellingcat.
The Verge
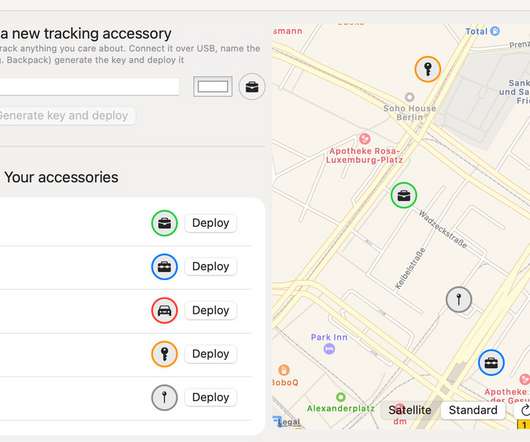
MARCH 4, 2021
OpenHaystack is a new open-source tool developed by security researchers at the Secure Mobile Networking Lab , who have essentially reverse-engineered the way Apple devices register themselves to the Find My mesh network. That doesn’t mean you should just go ahead and start using OpenHaystack, however.

Forrester IT
APRIL 18, 2017
The ever-dependable Barb Darrow at Fortune reported late last week that the OpenStack Innovation Center (OSIC) is to shut down. But this may not be quite so bad as it appears, because the OpenStack Innovation Center isn't nearly so critical to the open source cloud computing project as its name might imply. cloud computing.

Tech Republic Security
OCTOBER 19, 2020
The groups have been using off-the-shelf tooling and open source penetration testing tools at unprecedented scale, according to Accenture's 2020 Cyber Threatscape Report.

TechSpot
DECEMBER 14, 2021
Techspot reported on Log4J over the weekend after it was discovered last week. Since Friday, the open-source software's use has become a pandemic in its own right. Security firm Check Point has been monitoring the situation and, at one point, were seeing more than 100 Log4J attacks per minute.

SecureWorld News
DECEMBER 13, 2023
Log4j is a widely-used open source Java logging library, and the vulnerability allowed threat actors to execute remote code on servers, potentially leading to unauthorized access and data breaches. Lazarus' exploitation of the Log4j vulnerability in Operation Blacksmith emphasizes the risk associated with open source vulnerabilities.

TechSpot
OCTOBER 1, 2021
One area focused on within the report is the current state of Android malware. "It It is an open source system with many vendors having their own Android versions (with their own vulnerabilities and patching problems)," Eset security awareness specialist Ondrej Kubovi? told The Register.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content