The Anywhere Operating System
Forrester IT
FEBRUARY 22, 2022
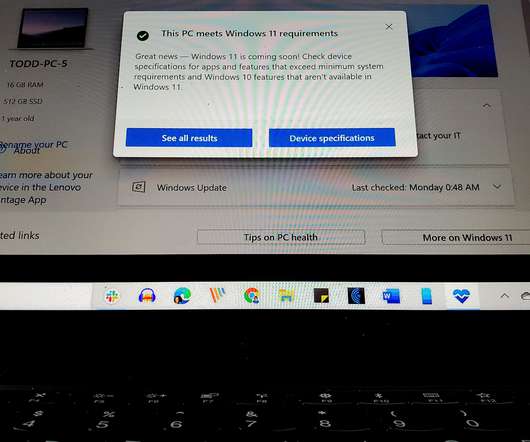
“Do Operating Systems Matter Anymore?” Today, we know that OS proliferation is happening — a majority of technology decision-makers in 2021 indicate that they have four or more operating systems in their organization — and it’s only going […].














































Let's personalize your content