Report: Attackers Move Lightning Fast to Capitalize on Vulnerabilities
SecureWorld News
DECEMBER 18, 2023
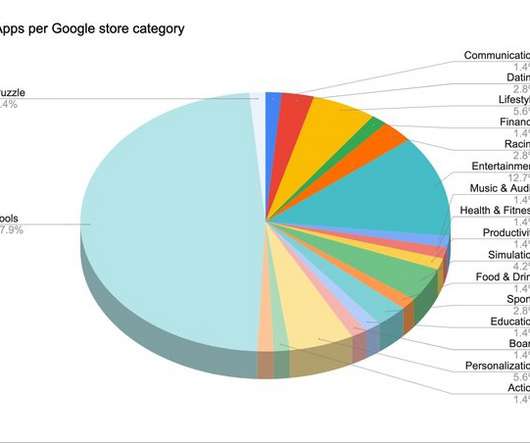
This morning, the Qualys Threat Research Unit released its 2023 Threat Landscape Year in Review report. One-third of high-risk vulnerabilities impacted network devices and web applications. 15 exploited by malware and botnets. 15 exploited by malware and botnets. 115 exploited by named threat actors.

















































Let's personalize your content