What is NAC and why is it important for network security?
Network World
MARCH 23, 2022
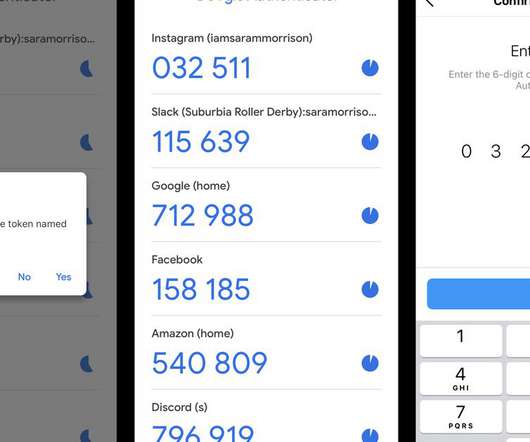
Network Access Control (NAC) is a cybersecurity technique that prevents unauthorized users and devices from entering private networks and accessing sensitive resources. NAC tools detect all devices on the network and provide visibility into those devices. How NAC works. To read this article in full, please click here














































Let's personalize your content