Hyperautomation: A Cybersecurity Solution for Burnt Out Teams
IT Toolbox
SEPTEMBER 13, 2023
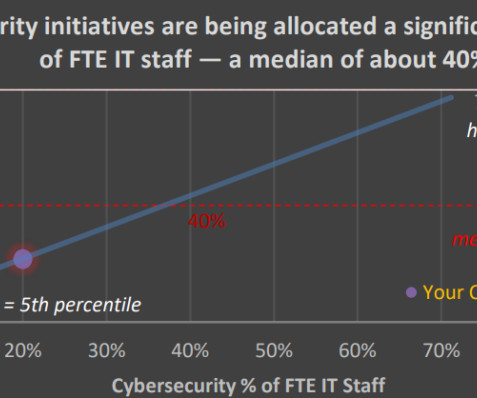
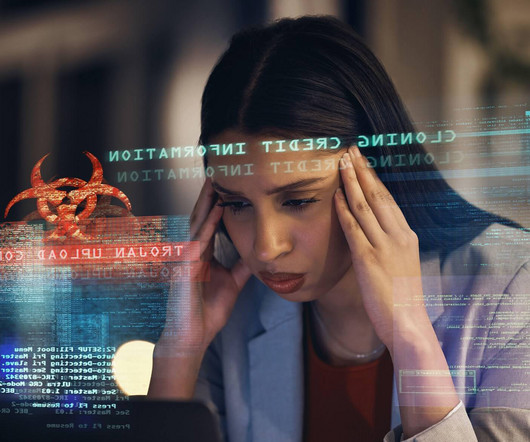
How can hyperautomation tackle the issue of burnout in the cybersecurity industry? The post Hyperautomation: A Cybersecurity Solution for Burnt Out Teams appeared first on Spiceworks.






































Let's personalize your content