Take control of your Oracle unlimited licensing agreement
CIO Business Intelligence
OCTOBER 6, 2023
Frequently, organizations are looking not just to trim costs, but for value-added services that few software vendors may be willing to provide.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

CIO Business Intelligence
OCTOBER 6, 2023
Frequently, organizations are looking not just to trim costs, but for value-added services that few software vendors may be willing to provide.

Tech Republic Security
JULY 24, 2022
It enables next-generation applications and can boost user productivity. As such, the LAN not only greatly impacts user experience, but is also the beginning or end of many security events. The post Not-So-Hidden Costs Are Lurking in the LAN: Insist on Operational and Licensing Simplicity appeared first on TechRepublic.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Generative AI Deep Dive: Advancing from Proof of Concept to Production
Reimagining Cybersecurity Training: Driving Real Impact on Security Culture

Kitaboo
MARCH 30, 2024
Leading digital textbook platforms like KITABOO, which incorporate DRM systems, play a pivotal role in data security. Data security has become the need of the hour, considering the growth in piracy, illicit distribution of content, and misuse of intellectual property. Licenses defining the terms and duration of content usage.

CTOvision
FEBRUARY 27, 2014
HP Enterprise Security Solutions to help 33 U.S. Department of Homeland Security (DHS) has awarded the company a cybersecurity contract worth up to $32.4 Department of Homeland Security (DHS) has awarded the company a cybersecurity contract worth up to $32.4 By Bob Gourley. PALO ALTO, Calif. — HP today announced the U.S.

CIO Business Intelligence
MAY 25, 2023
Having the right licenses for the applications the business needs are critical. Licensing can sometimes be complex to understand, however, which is why SMBs should make sure they’re sourcing their licenses from the right places. Microsoft 365 is the productivity engine at the heart of many SMB businesses across Australia.

CIO Business Intelligence
FEBRUARY 20, 2024
Concurrently, the threat posed by data breaches increases, risking patient privacy and regulatory breaches such as with security measures incorporated in the Health Insurance Portability and Accountability Act (HIPAA) and the General Data Protection Regulation (GDPR). The good news is that AI can be used to improve security.

Tech Republic Security
MAY 8, 2022
Bridgecrew by Prisma Cloud is the codified cloud security platform built to bridge the gap between DevOps and security teams. With Bridgecrew’s platform, teams can streamline cloud security, enforce. With Bridgecrew’s platform, teams can streamline cloud security, enforce.

CIO Business Intelligence
APRIL 13, 2023
Gartner projects that spending on information security and risk management products and services will grow 11.3% To better focus security spend, some chief information security officers (CISOs) are shifting their risk assessments from IT systems to the data, applications, and processes that keep the business going.

CIO Business Intelligence
JUNE 16, 2022
Against a backdrop of disruptive global events and fast-moving technology change, a cloud-first approach to enterprise applications is increasingly critical. What could be worse than to plan for an event that requires the scaling of an application’s infrastructure only to have it all fall flat on its face when the time comes?”.

Kitaboo
MARCH 30, 2024
Collaborating with digital textbook platforms like KITABOO empowers content creators to explore eBook security and ePUB DRM Solutions. Digital Rights Management (DRM) serves as a security system and a protective barrier that protects intellectual property from unauthorized downloading and ensures only the right user has authorized access.
Kitaboo
MARCH 26, 2024
eBook DRM: Revolutionizing eBook Distribution and Use Protection of IP Rights Secure Distribution Channels Expanded Outreach Flexibility in Business Models More Monetization Opportunities Better Control Through Analytics III. It includes methods like user authentication, verification, licensing of eBooks, encryption, etc.
GeekWire
MARCH 19, 2024
Blue Origin said the DarkSky-1 system is expected to be launched as a payload on a future national-security space launch manifested by the U.S. Mission duration would be no more than 12 hours, Blue Origin says in the application. Space Force. million for the development of multi-orbit logistics vehicles.

Kitaboo
APRIL 22, 2024
Just like you secure your home with a sturdy lock, eBook DRM shields your literary masterpieces from illicit copying and sharing. Customizing Accessibility Authorization and Licensing Encryption: The Shield of Protection Detecting Unauthorized Distribution Unique Codes DRM Variations IV. Table of Contents: I. What is an eBook DRM?

mrc's Cup of Joe Blog
DECEMBER 19, 2019
So, where is enterprise application development headed in the coming year? photo credit: lakexyde via pixabay cc It’s an exciting time in the world of enterprise application development. These days, enterprise web application development is: Rapidly evolving : Web application development is going through major changes.
Kitaboo
APRIL 24, 2024
Encryption Key Usage Control License Acquisition Expiation III. DRM for eBook Security and User Experience Device Compatibility Safe Transactions Personalized Recommendations IV. Some DRM platforms allow the sharing and transfer of licenses between 2-3 devices. Table of Contents I. What is DRM? How Does DRM Work?

Kitaboo
FEBRUARY 16, 2024
Key Features and Benefits of DRM Protection Encryption Access Control License Management Watermarks Cross-Platform Compatibility III. Key Features and Benefits of DRM Protection DRM protection offers a range of features and benefits designed to enhance the security of digital content. Table of Contents: I.

CIO Business Intelligence
DECEMBER 4, 2023
By: Scott Sellers , Co-Founder and CEO, Azul After almost 30 years, Java remains the programming language of choice for large-scale enterprise applications in the cloud, on-prem, or hybrid. Its versatility, reliability, stability, and open-source and third-party libraries and frameworks make developing and running applications very efficient.

Kitaboo
MAY 23, 2023
In this comprehensive guide, we will delve into the fascinating world of Digital Rights Management (DRM) and explore how it is implemented in software applications. With the advancements in encryption algorithms, secure key management, and robust licensing systems, software-based DRM has become the go-to choice for protecting digital content.

CIO Business Intelligence
DECEMBER 21, 2023
By analyzing large volumes of clean data from various sources, such as network traffic logs and user behavior patterns, AI can correctly identify anomalies and potential security breaches that may go unnoticed by traditional security measures. Real-time processing is key to keeping systems secure and ensuring swift incident handling.

CIO Business Intelligence
NOVEMBER 5, 2023
Taking the programmer out of software development, low-code provides tools that enable people with minimal training and coding skills to create and adapt applications themselves using prebuilt templates and program modules. Applicability & Customisability. Empowering Citizen Developers. Reporting and analytics.

GeekWire
JANUARY 19, 2023
(GeekWire File Photo / Taylor Soper) T-Mobile disclosed in a regulatory filing Thursday that a hacker obtained data from about 37 million customer accounts using an API, or application programming interface. The Bellevue, Wash.-based The hack started on or around Nov. 25, and T-Mobile identified the bad actor Jan.

CTOvision
AUGUST 15, 2016
Here is how Microsoft describes themselves: Microsoft Corporation is engaged in developing, licensing and supporting a range of software products and services. The Company operates in five segments: Devices and Consumer (D&C) Licensing, D&C Hardware, D&C Other, Commercial Licensing, and Commercial Other.

SecureWorld News
JUNE 19, 2023
The breach, which exploited a Zero-Day vulnerability, has raised concerns about the patching practices and security measures employed by organizations worldwide. million Oregonians who possess an ID or driver license. Despite their efforts, unauthorized actors had already accessed multiple files before the security alert was received.

Phil Windley
AUGUST 28, 2023
Zero Trust is a security framework that is better attuned to the modern era of sophisticated threats and interconnected systems. If we assume breach, then the only strategy that can protect the corporate network, infrastructure, applications, and people is to authorize every access. password, fingerprint, OTP) before granting access.

The Verge
AUGUST 20, 2021
While someone in possession of the leaked data said they had obtained information for as many as 100 million customers , including driver’s license info, IMEI numbers, and more, T-Mobile’s first statement put the figure at 47 million or so and did not mention the IMEI / IMSI data. Now, T-Mobile has confirmed that for the 7.8 Additionally, 5.3

CTOvision
NOVEMBER 26, 2014
The National Security Agency announced today the public release of its new technology that automates data flows among multiple computer networks, even when data formats and protocols differ. “NSA’s innovators work on some of the most challenging national security problems imaginable,” said Linda L. economic growth.”
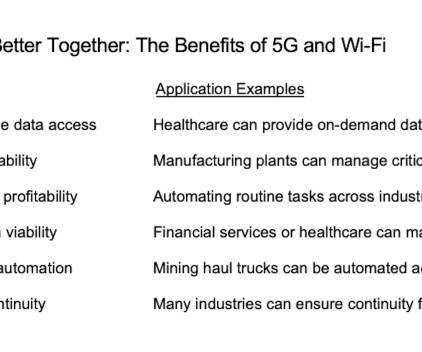
CIO Business Intelligence
SEPTEMBER 12, 2023
That’s because the 5G technology powering your phone remains intact, giving you a reassuring sense of security and an open line of communication with weather updates, friends and family during the storm. Improve capacity and latency Enterprise network traffic is growing, and new data-hungry applications require faster and faster data speeds.

CIO Business Intelligence
NOVEMBER 29, 2023
Once enterprises commit to running business-critical applications in the cloud, they rarely move to another provider. But if you do your planning exercise properly, you shouldn’t have to move your applications around,” he says. But doing this requires planning ahead early on, before moving an application to the cloud the first time.
CIO Business Intelligence
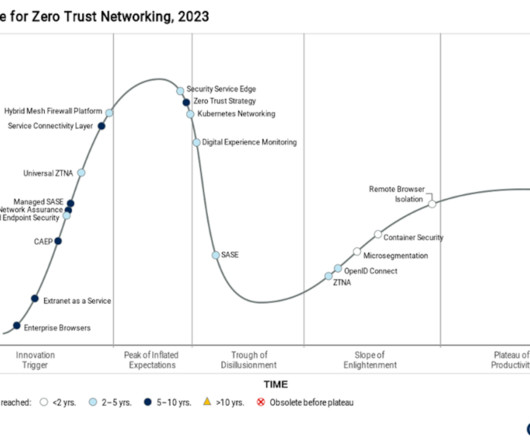
NOVEMBER 2, 2023
In the recent Gartner® Hype Cycle TM for Zero Trust Networking, 2023 report , which evaluates the current status of 19 of “the most relevant and hyped” zero-trust technologies, the cybersecurity industry analysts made a somewhat startling pronouncement about secure access service edge (SASE). 3 Why the trough of disillusionment?

CIO Business Intelligence
DECEMBER 5, 2023
While it’s critical to control costs continuously, it becomes even more imperative during times of economic pressure,” says Jon Pratt, CIO at security managed services provider 11:11 Systems. Following are some actions IT leaders can take now to secure those funds for the future.

CIO Business Intelligence
MAY 3, 2024
Besides, the expanded offering also includes IBM’s flagship database Db2 Cloud Pak for Data as well as a portfolio of automation software including Apptio, Turbonomic, and Instana, and the IBM Security and Sustainability software portfolios — all built on Red Hat OpenShift Service on AWS.

CTOvision
MAY 1, 2015
The Cloud Security Alliance (CSA) is the world’s leading organization dedicated to defining and raising awareness of best practices to help ensure a secure and highly functional cloud computing environment. Presenting: Jim Reavis, CEO, Cloud Security Alliance. Cognitio has tracked and supported the CSA since the beginning.

Network World
NOVEMBER 27, 2018
That seems to be the mantra for Cisco in 2019 as the company pushes software-defined WANs, cloud partnerships, improved application programs and its over-arching drive to sell more subscription-based software licenses. Check out What is hybrid cloud computing and learn what you need to know about multi-cloud. | billion.

CIO Business Intelligence
MARCH 19, 2024
Rather than selling software to customers, HP said, Autonomy had been selling them hardware at a loss, then booking the sales as software licensing revenue. December 2012: HP says it is cooperating with the Department of Justice, the Securities and Exchange Commission and the UK’s Serious Fraud Office in an investigation relating to Autonomy.

CIO Business Intelligence
JANUARY 17, 2023
So when it comes to securing funding and resources from the board, is the CIO put in the box seat if technology is at the center of investment strategy? Review software licenses and subscriptions Many organizations are over-licensed and oversubscribed on software, pushing costs higher than they need to be. Not necessarily.

CIO Business Intelligence
APRIL 29, 2024
This ransomware-based crime involved hackers demanding cash payments from the companies after hacking into databases that included members’ driver’s license information and Social Security numbers. Artificial Intelligence, Security No AI-based deepfake technology was used in these attacks.

CIO Business Intelligence
MARCH 19, 2024
And we’ve completed the software business-model transition that began to accelerate in 2019, from selling perpetual software to subscription licensing only – the industry standard. We’ve changed how and through whom we will sell our software. VMware Cloud Foundation , or VCF, is our platform for innovation going forward.

CIO Business Intelligence
MAY 24, 2023
Where the widespread adoption of SaaS previously distributed IT and lines-of-business selected and implemented their own applications, the pendulum is now shifting back with CIOs pursuing large-scale transformations to drive value and re-centralize operations. Plus, the IT organization itself can be fertile ground for automation.

CIO Business Intelligence
SEPTEMBER 14, 2023
Nasdaq is currently using gen AI for a range of applications, including supporting digital investigators’ efforts to identify financial crime risk and empowering corporate boards to consume presentations and disclosures more efficiently. The company, which reported net revenues of $3.6

CIO Business Intelligence
JANUARY 10, 2024
Migrating infrastructure and applications to the cloud is never straightforward, and managing ongoing costs can be equally complicated. Refactoring applications to take advantage of cloud-native services is vital to maximizing cloud ROI. Overspending is easy to do,” says Chris McMasters, CIO at the City of Corona, California.

CIO Business Intelligence
JANUARY 5, 2023
Low-code/no-code visual programming tools promise to radically simplify and speed up application development by allowing business users to create new applications using drag and drop interfaces, reducing the workload on hard-to-find professional developers. So there’s a lot in the plus column, but there are reasons to be cautious, too.

TM Forum
OCTOBER 12, 2022
“The decision to deploy a new, cloud-native OSS was made based on our strategy to leverage the benefits offered by the cloud in terms of scalability, security and automation. A hodgepodge of applications stranded on aging and out-of-date infrastructure becomes unmanageable. Today the applications are deployed in the MTC cloud.

Dataconomy
MAY 21, 2024
Also known as identity verification software, ID scanning software automates data extraction from identification documents like driver’s licenses, passports, and ID cards. Errors or missing information may result in delays in processing applications, customers, or compliance breaches.

CIO Business Intelligence
JULY 26, 2023
Over the past three or four years, the industry has been abuzz with the concept of delivering converged security and networking features via the cloud. Because SASE touches so many elements of security and networking, most enterprises use multiple vendors and point products to build a solution.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content