The Internet Has A New Problem: Repeating Random Numbers!
CTOvision
FEBRUARY 18, 2019
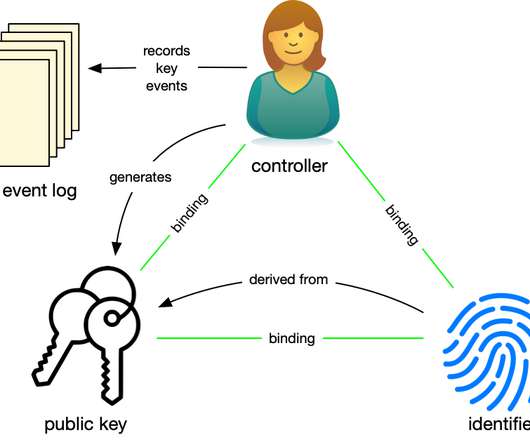
Digital Certificates are a foundational building block of the Internet. They are used to verify the identity of e-commerce sites, the authenticity of software and encrypt data. Not surprisingly, cyberattackers try to create fake Certificates or get the Private Keys for real ones to steal data or intercept communications.














































Let's personalize your content