Palo Alto Networks debuts cloud-native firewall service for AWS
Venture Beast
MARCH 30, 2022
Palo Alto Networks has unveiled a new cloud-native firewall service for Amazon Web Services (AWS), aiming to simplify cloud network security. Read More.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 category
category 
Venture Beast
MARCH 30, 2022
Palo Alto Networks has unveiled a new cloud-native firewall service for Amazon Web Services (AWS), aiming to simplify cloud network security. Read More.

CIO Business Intelligence
MARCH 7, 2024
Enterprise AI traffic monitoring: Vigilantly monitor AI activities within the enterprise to identify anomalies or potential security threats and allow for prompt intervention. Firewall capability for AI security: Enhance security measures by providing firewall capabilities to safeguard against potential AI-related vulnerabilities.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Venture Beast
AUGUST 28, 2021
Even if placed behind a firewall, inadequately secured robots may not be safe. We’ve already seen malware that breaches isolated networks. Read More.

Venture Beast
FEBRUARY 15, 2022
F5 launched its Distributed Cloud Services platform with application security features such as API protection and web application firewall. Read More.
Venture Beast
FEBRUARY 15, 2022
Netacea is an upcoming provider in the application security solutions market, which Forester anticipates will grow from $4.7 billion by 2025, as bot management solutions gradually overtake traditional web application firewall (WAF) solutions. billion in 2019 to $12.9 Read More.

Network World
APRIL 26, 2017
Nothing beats hearing from your peers about which IT security products have been successful in the enterprise. IT Central Station selected the product leaders in each security category. To read this article in full or to leave a comment, please click here (Insider Story)

ForAllSecure
FEBRUARY 23, 2023
All of these APIs have one thing in common: they need to be secure. Unfortunately, many devs and ops engineers don't view API security as a priority - and that's a mistake. In this blog post, we'll explore why API security is so important, and how you can make sure you're doing it right. Or something else entirely.

CTOvision
NOVEMBER 10, 2016
Threats outside the firewall are vast and dynamic. RiskIQ provides organizations access to the widest range of security intelligence and applications necessary to understand exposures and take action - all without leaving the platform. We are pleased to have Georgian Partners as part of our strong investment and advisory team. "Our

CTOvision
AUGUST 20, 2016
With this post we are initiating coverage of Bayshore Networks in our IoT Companies category. Bayshore Networks was founded to safely and securely protect Industrial IoT networks, applications, machines and workers from the threats of the Internet. Research Team.

Venture Beast
MARCH 25, 2022
Threatblockr's announcement comes as traditional IT security measures like firewalls struggle to keep up with a variety of vulnerabilities. Read More.

Linux Academy
JUNE 26, 2019
In today’s interconnected world, data security has never been more important. By training your IT staff to keep your systems secure, you can prevent harmful or costly data breaches. If your organization handles either of these sensitive data types, you must follow guidelines to keep your systems secure. Security policies.
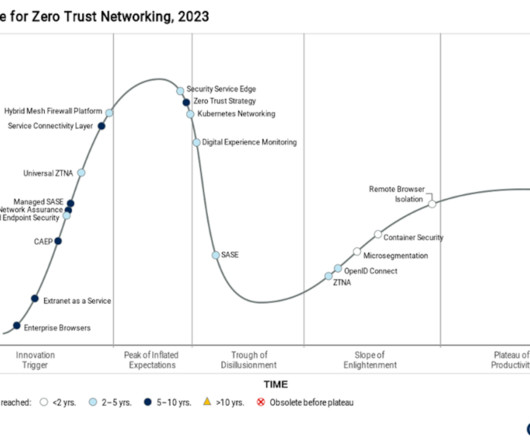
CIO Business Intelligence
NOVEMBER 2, 2023
In the recent Gartner® Hype Cycle TM for Zero Trust Networking, 2023 report , which evaluates the current status of 19 of “the most relevant and hyped” zero-trust technologies, the cybersecurity industry analysts made a somewhat startling pronouncement about secure access service edge (SASE). What is SASE? 5 I agree.

CTOvision
MARCH 12, 2015
CyberEdge Group surveyed more than 800 security decision makers and practitioners seeking a 360 degree view of threats, defenses and planned investments. Their bottom line up front: IT security spending is increasing, but confidence is falling. Security spending continues to rise. Security analytics in top demand.

SecureWorld News
SEPTEMBER 12, 2022
China's National Computer Virus Emergency Response Center (CVERC) recently made a statement accusing the United States National Security Agency (NSA) of repeatedly hacking the Northwestern Polytechnical University, a key public military research university located in Xi'an, China. stealing over 140GB of high-value data.

CTOvision
MAY 28, 2014
Additionally, it includes a Project Development Kit (PDK) and a solution guide. ” Only the Software AG IoT Solution Accelerator helps companies build an integrated, comprehensive platform for the entire IoT infrastructure with robust, end-to-end security.

GeekWire
DECEMBER 3, 2022
.” Many companies treat the battle against bots as a “DIY project,” hiring their own engineers to address the problem, or leaving it to their internal security teams to deal with it, which Locoh-Donou described as a mistake. To be sure, F5 has a vested interest in that viewpoint. billion in 2025, Aite-Novarica estimates.

Galido
FEBRUARY 7, 2019
Ever wonder what secures 4G and 5G mobile networks from attacks? Positive Technologies has performed audits of SS7 website signaling networks since 2014 and continues to secure next-generation 4G and 5G networks with their PT Telecom Security Assessment. Maximized efficiency of other security measures.

SecureWorld News
JANUARY 13, 2022
For IT professionals and facility administrators, it is a term that governs the common features, technology, consumables, and security present in an office environment. Organizations must adapt their security controls to home networks and even public WiFi. All communication is secured (internal or external).

Network World
JULY 22, 2016
Yes, some industries have different regulations, use cases or business processes that demand specific security controls, but overall every company needs things like firewalls, IDS/IPS, threat management gateways and antivirus software regardless. CISO progression.

CIO Business Intelligence
AUGUST 15, 2022
Instead, Koch’s engineering team set about virtualizing the physical transports to build the SD-LAN and firewall within the cloud rather than in the data center. Leased lines and direct connects would remain in the data center as part of this strategy, but Hoag did not want to route users through the data center to access data on the cloud.

Venture Beast
DECEMBER 7, 2021
SASE solutions close network cybersecurity gaps so enterprises can secure and simplify access to resources from any location. Read More.

CIO Business Intelligence
JUNE 21, 2023
Today, CIO and CISO teams are tasked with multiple business-critical initiatives like securing and connecting work-from-anywhere employees, moving applications to the edge or the cloud, and securing operational technology (OT) and IT environments. security effectiveness rating.
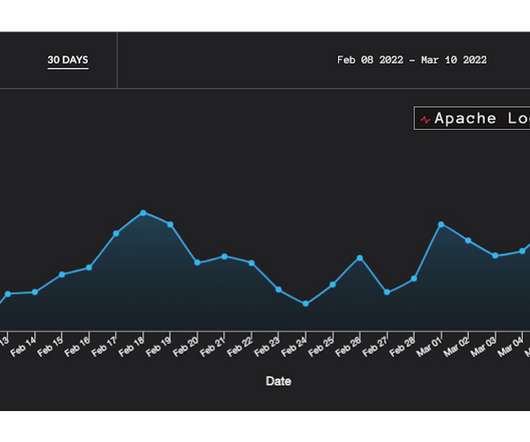
Venture Beast
MARCH 14, 2022
GreyNoise launched a free security tool to guard against critical vulnerabilities that are being widely exploited, such as the flaw in Log4j. Read More.

CIO Business Intelligence
JULY 11, 2022
This digital transformation requires businesses to bring together data, applications, and users in a secure way—across digital and hybrid environments that are distributed, complex, and expanding. Enter the need for integrated networking and security. SASE is SD-WAN-as-a-service and security-as-a-service.

CTOvision
JUNE 3, 2014
According to the federal model, there are 15 functional areas comprising a comprehensive continuous monitoring solution, as shown in the graphic below: These functional areas are grouped into the following categories: Manage Assets. Security Lifecycle Management. Each category addresses a general area of vulnerability in an enterprise.

A Screw's Loose
DECEMBER 20, 2012
We started off with a tweet about how all people really want is Windows on their iOS device and quickly moved down the rat hole of VDI and from there to Risk, Security and Users and all about Mobile. print Tagged as: Enterprise Strategy , Security , strategy. They may not even unplug themselves from the main network. CloudOfCaroline.

CIO Business Intelligence
JANUARY 24, 2024
Securing IoMT IoMT devices represent a huge opportunity for practitioners to improve the quality of care and for patients to reap the benefits of important advances in treatment. While new regulations in Europe and elsewhere govern their use, manufacturers are lagging behind with security. This all helps the regulatory environment.

CIO Business Intelligence
APRIL 12, 2022
For today’s enterprise, there is a very legitimate argument that cloud security architecture is the single most important part of a CISO’s operation. The cloud providers take application and infrastructure security responsibility, yet the responsibility of access and data security resides with enterprise security teams.

Victus pro Scientia Opus -- Food for the Knowledge
JANUARY 9, 2007
Enterprise 2.0 Web/Tech Weblogs Add me to your TypePad People list Subscribe to this blogs feed See how were connected « Geek Reading, Dec. 2006 | Main | Office 2007 -- In Production Use » January 09, 2007 The Poor Mans Groove?

Data Center Knowledge
JULY 17, 2013
The need for application management tools is particularly critical when applications go beyond typical single server Web sites into the more complex category of multi-tier enterprise applications. In contrast to Cloud Management, the emerging category of “Cloud Application Management” addresses the next level above the Infrastructure cloud.

Scott Lowe
SEPTEMBER 1, 2015
Obviously, mobile is a category that is growing very rapidly, and Poonen talks about VMware’s movement in this space via the AirWatch acquisition. Poonen shows a video with a few customer testimonials, and then introduces Jim Alkove, Corporate VP in charge of enterprise management and security for Windows at Microsoft.

A Screw's Loose
MARCH 20, 2013
One tweeter mentioned that IT was not only the security police but the productivity police as well. Depending on the tool it can be done by category or sometimes has to be done by app name. Is the best way to handle that to cut off the streams at the firewall? Categories. Select Category. You can blacklist apps.

ForAllSecure
MARCH 10, 2021
Within infosec, where so many challenges that are intangible -- like configuring network or firewalls. And if you can find a way around it, find a way to do it without the proper token again even someone who's not a security practitioner instantly rocks the realization of what that kind of impact is. The lock is just verifying that.

ForAllSecure
MARCH 9, 2021
Within infosec, where so many challenges that are intangible -- like configuring network or firewalls. And if you can find a way around it, find a way to do it without the proper token again even someone who's not a security practitioner instantly rocks the realization of what that kind of impact is. The lock is just verifying that.

A Screw's Loose
DECEMBER 10, 2012
Then you have the personal firewall that is centrally managed by IT and let’s not forget that you are hooked up to a proxy server if you try to access the internet. IT didn’t necessarily spend a lot of time training the end user on what to watch out for and how to stay secure. understand the policy and security that follows the data.

ForAllSecure
MAY 2, 2023
So he invites me to go to a book that, you know, one of those first black hats and Doug Song was set doing his thing on checkpoint firewall bypass, and I'm sitting there, and a guy named Jeff Nathan. And so, myself and another individual named Rob Farrell, we were brought in to start a security team. Come sit next to me.

TM Forum
OCTOBER 21, 2021
Norway’s 5G-VINNI facility site, hosted by Telenor Research in Oslo, leverages network equipment from Ericsson, Huawei and Nokia, testing equipment from Keysight and EANTC, security solutions by Palo Alto networks and a Cisco IoT fabric. in the Beyond Connectivity category. ExcellenceAwards2021logo.jpg. image_alt_text.

The Verge
AUGUST 10, 2020
On August 6th, Trump declared TikTok and WeChat a “national emergency” because of real — but also politically convenient — privacy and security concerns. Existing app users wouldn’t necessarily be forced off the network, however, the way they’d be with China’s site-blocking Great Firewall. TikTok is now a national emergency.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content