Ermetic raises $70M for ‘identity-first’ cloud security
Venture Beast
DECEMBER 15, 2021
Ermetic, which offers a platform for cloud and container security focused on securing identities, announced a $70 million series B round. Read More.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 page b
page b  Security Related Topics
Security Related Topics 
Venture Beast
DECEMBER 15, 2021
Ermetic, which offers a platform for cloud and container security focused on securing identities, announced a $70 million series B round. Read More.

TechEmpower - Information Technology
JULY 24, 2023
Do you have specific landing pages? Is there a need for A/B testing? SEO Support Will URLs and page content need to be properly formed for SEO? Will you need to add arbitrary new pages? Security What are the business / application’s specific security risks? Do you rely on affiliates?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Venture Beast
JANUARY 5, 2022
Xage, which offers zero trust identity security for operational technology customers, raised a $30 million series B to scale its deployments. Read More.
Venture Beast
DECEMBER 7, 2021
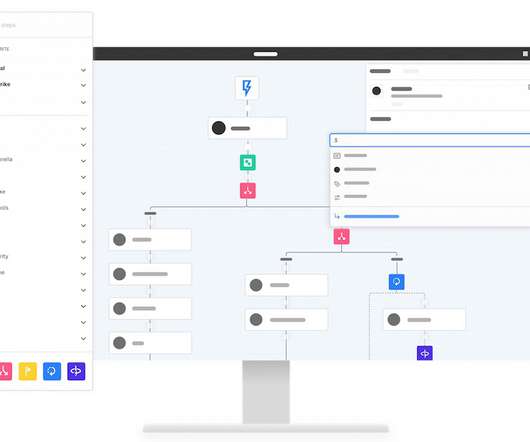
Torq says it's found "incredible" customer demand this year for its platform, which offers no-code automation for security teams. Read More.
Venture Beast
DECEMBER 7, 2021
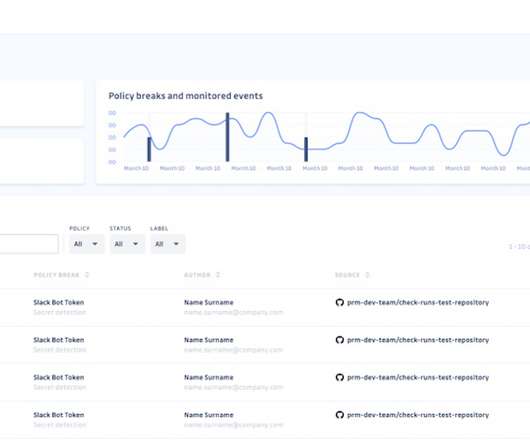
GitGuardian, which offers a secrets detector for GitHub, aims to expand into a broader provider of code security and enabler of DevSecOps. Read More.

SecureWorld News
NOVEMBER 23, 2022
The 37-page document was finalized Oct. This 'never trust, always verify' mindset requires us to take responsibility for the security of our devices, applications, assets, and services; users are granted access to only the data they need and when needed," John B. 21 and released for public consumption on Nov.

Linux Academy
MAY 13, 2019
Good, since we’re all on the same page, why is this such a bad situation? We have incident response plans so we can quickly address security incidents and eliminate the threat as quickly as possible. Incident Response Practice and Improving Security. It’s bad because when an incident occurs, time is of the essence.

Linux Academy
APRIL 22, 2019
Happy Monday, and welcome back to Roadmap to Securing Your Infrastructure. That’s right — over 6 1/2 billion (with a B) accounts. HIBP is kind enough to offer a special signup page to search by entire domains at no cost. Previous tips for securing your infrastructure: Check for vulnerabilities in your infrastructure.

CTOvision
MAY 22, 2017
The megatrends we track can be remembered with the mnemonic acronym CAMBRIC, which stands for C loud Computing , A rtificial Intelligence , M obility , B ig Data , R obotics , I nternet of Things , C yberSecurity. You can confirm that on our Newsletter Subscriptions page.

Kitaboo
JANUARY 30, 2024
Visit KITABOO to get quick file conversions and securely distribute your content across all devices. Managing Complex PDF Layouts during Conversion To handle complex layouts, the easiest way is to adjust the conversion options such as scaling, page margins, and font settings. To know more, please write to us at kitaboo@hurix.com.

CTOvision
JANUARY 9, 2017
The megatrends we track can be remembered with the helpful mnemonic acronym CAMBRIC, which stands for C loud Computing , A rtificial Intelligence , M obility , B ig Data , R obotics , I nternet of Things , C yberSecurity. You can confirm that on our Newsletter Subscriptions page.
The Verge
DECEMBER 29, 2020
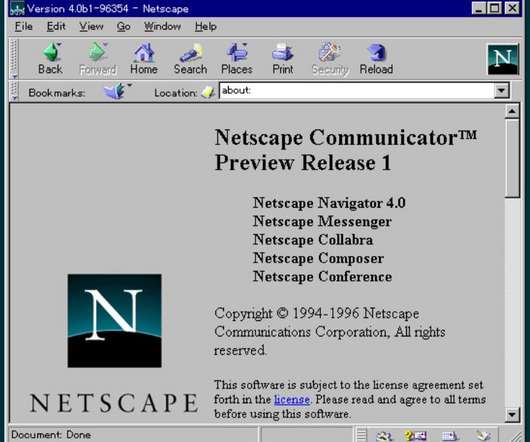
But some security researchers have noted some puzzling aspects of the deal, including mentions of the defunct, 23-year old Netscape Communicator email software and recommendations of outdated encryption standards. pic.twitter.com/573xNdN3ZH — Prof B Buchanan OBE (@billatnapier) December 26, 2020. looked like. 509 standard.

Dataconomy
FEBRUARY 27, 2024
Improved security Companies can use data analytics to improve their security significantly. Split testing, or A/B testing, involves creating different versions of a site to assess which version functions better. Based upon the results of user behavior analysis, analysts can adjust layouts, page features, internal links, etc.

Kitaboo
MARCH 23, 2021
The camera is placed in a way that allows the person or machine to easily turn the pages. However, the method is time-consuming since the book is first cut and then the loose pages are fed into the machine. The scanning technology can capture the page and create a digital image with little or no damage to the text or graphics.
Kitaboo
NOVEMBER 4, 2022
The fixed-layout format in eBooks is mostly used for projects with more complex page layouts and where there is a need to have absolutely placed content. Reflowable vs. Fixed-page-Which eBook Format Is Right For You? Fixed-layout Formats. KF8, and Kindle Textbook Creator for Kindle Devices by Amazon. Limitations. Limitations .

CTOvision
FEBRUARY 7, 2017
You can remember them all with the helpful mnemonic acronym CAMBRIC, which stands for C loud Computing , A rtificial Intelligence , M obility , B ig Data , R obotics , I nternet of Things , C yberSecurity. A great way to track the emerging developments in this domain is our page on Robotic Companies.

ForAllSecure
OCTOBER 11, 2022
< int fuzzme(char *buf) { if(buf[0] == 'b') if(buf[1] == 'u') if(buf[2] == 'g') { return 0; // Fixed: No more defect. Within the create new run flow, click the Show Mayhemfile link at the bottom of the page to confirm that your Mayhemfile looks similar to the following: image: index.docker.io/forallsecure/tutorial:latest

ForAllSecure
SEPTEMBER 28, 2022
> int fuzzme(char *buf) { if(buf[0] == 'b') if(buf[1] == 'u') if(buf[2] == 'g') { abort(); // Defect: Sends a SIGABRT signal } return 0; } int main(int argc, char *argv[]) { FILE *f; char buf[12]; if(argc != Development Speed or Code Security. For this exercise we will be executing a Mayhem run on the previously discussed testme.

Kitaboo
MARCH 12, 2019
But some software tools provide additional features like text search, page jump, font and size change, hyperlinks, day and night reading mode, table of content creation, read aloud etc. B) What the eBook Conversion Service Company Offers: 1. Data Security: Ensure that the company offers data security and copyright protection.

Kitaboo
JANUARY 21, 2021
Below are some of the key features of the KITABOO reader – Offers DRM protection and encryption for content security. Features a supportive online community, the platform also offers a detailed inspiration hub with a tips and tutorials page, creative writing exercises and other publishing resources in one place.

CIO Business Intelligence
JULY 10, 2023
“The changes required for effective digital transformation are essential to create a new, advanced organization,” says Pankaj Setia, chairman of the center for digital transformation at India’s top B school, IIM Ahmedabad. For instance, we had to junk our homegrown HR solution to migrate to the global HR solution.

ForAllSecure
OCTOBER 4, 2022
> int fuzzme(char *buf) { if(buf[0] == 'b') if(buf[1] == 'u') if(buf[2] == 'g') { return 0; // Fixed: No more defect. Within the create new run flow, click the Show Mayhemfile link at the bottom of the page to confirm that your Mayhemfile looks similar to the following: image: index.docker.io/forallsecure/tutorial:latest

Cloud Musings
MAY 16, 2016
This leads to an increased need to categorize those assets and apply appropriate security controls with respect to business/mission functions, data user role, location of access, legal/regulatory guidelines and user devices. For more content like this, visit Point B and Beyond. Grab this Headline Animator ( Thank you.

GeekWire
FEBRUARY 16, 2022
He eventually built a website using Github pages. He worked with teams at two different hospitals to secure Evusheld for his wife. She received a shot last week that should give her protection for six months, which would get her close to 12 months past her last chemotherapy treatment, an important benchmark for growing healthy B-cells.

Kitaboo
JUNE 13, 2023
B) Time and Cost Efficiency Ready-to-Use Platform By opting for a white-label eBook platform, businesses can leverage a pre-built solution that is ready to use. Businesses can design and distribute personalized marketing collateral, such as landing pages, banners, and social media graphics, to promote their eBooks.

Cloud Musings
NOVEMBER 15, 2012
15, 2012 — NJVC , an information technology solutions provider headquartered in Northern Virginia, announces it will spotlight its Cloudcuity ™ framework for delivering secure and unified cloud management solutions at the Gartner Data Center Conference , December 3 – 6, at The Venetian Resort Hotel and Casino ® in Las Vegas.

Kitaboo
APRIL 16, 2023
B&N accepts formats like doc, Docx, txt, HTML, and EPUB. It supports formats like EPUB and multi-touch books created in Apple Pages. The platform also allows you to publish your book on other platforms simultaneously. The authors are entitled to a royalty of 70% on each sale. It is the second-largest online retailer of eBooks.

SecureWorld News
APRIL 15, 2021
And I don't always agree with that definition b ecause the more I studied the psychology behind how we make decisions as people, the more I realized that there's a positive and a negative, like a yin and a yang to social engineering. Y ou have to take the security risk out of the person's hands. And that handles security.

Cloud Musings
DECEMBER 27, 2011
One in particular is their recommendation for a National Office for Cyberspace (NOC) and a new National Security Council Cybersecurity Directorate (NSCCD). Use FedRAMP when conducting risk assessments, security authorizations, and granting ATOs for all Executive department or agency use of cloud services; ii. B) ELEMENTS.—The

SecureWorld News
DECEMBER 14, 2021
And they are posting about it on the Kronos user group page. efujioka2 posted: "I am disappointed that UKG being the size they are and all they promote there was no Plan b, c, d etc. Barani wrote: "Knowing this is a ransomware attack, do we have a word on data security? Why did I renew my support when I am not receiving any?".

Cloud Musings
SEPTEMBER 5, 2016
million by 2019; Hybrid warfare, a new type of global conflict where conventional and cyber warfare are combined and in which the aggressor avoids attribution or retribution, is now front page news. For more content like this, visit Point B and Beyond. ). Don’t sit cowering in a corner. TAKE ACTION TODAY!

Cloud Musings
OCTOBER 17, 2011
Location: Room 103, Henry B. Panelists: Don Cotter, CTO, Department of Homeland Security. A prolific blogger and first-time book author on cloud computing, he was recently named one of the “Most Powerful Voices in Security” by SYS-CON MEDIA. Cloudcuity Secure, Unified Cloud Management and Control Services.

ForAllSecure
APRIL 3, 2019
Software security is a global challenge that is slated to grow worse. The application attack surface is growing by 111 billion new lines of software code every year, with newly reported zero-day exploits rising from one-per-week in 2015 to one-per-day by 2021, according to the Application Security Report from Cybersecurity Ventures.

Crafty CTO
JULY 21, 2023
Meta AI Releases Llama 2 Meta’s Llama 2 release is a seminal event, given that (a) Meta’s initial LLaMA 1 release spawned AI March Madness , (b) Llama 2 is substantially more capable than the first LLaMA, and (c) This time Meta is allowing as opposed to blocking commercial use. I’ll concentrate in two areas.

A Screw's Loose
OCTOBER 8, 2012
I was having an interesting conversation tonight on Twitter with Rafal Los about OSes and security. We spend a lot of time in the enterprise developing solutions and working hard to make sure that our solutions are secure. You can no longer b t your end users. print Tagged as: Security , strategy. A Screw's Loose.

ForAllSecure
APRIL 3, 2019
Software security is a global challenge that is slated to grow worse. The application attack surface is growing by 111 billion new lines of software code every year, with newly reported zero-day exploits rising from one-per-week in 2015 to one-per-day by 2021, according to the Application Security Report from Cybersecurity Ventures.

ForAllSecure
APRIL 3, 2019
Software security is a global challenge that is slated to grow worse. The application attack surface is growing by 111 billion new lines of software code every year, with newly reported zero-day exploits rising from one-per-week in 2015 to one-per-day by 2021, according to the Application Security Report from Cybersecurity Ventures.

Social, Agile and Transformation
JANUARY 26, 2009
The problem is that the SaaS vendor has to solve two fundamental technology problems: (a) writing and supporting really good software and (b) hosting many customers at competitive service levels and required security. saas security mobile security cloud security data safety data integrity Reply Delete Add comment Load more.

ForAllSecure
MARCH 14, 2022
In fact, I remember starting a new job by flying to Auburn Hills, Michigan for the very first meeting of the Featherstone Group, a collection of automotive OEM executive and security professionals. Steve Grobman, CTO with Intel’s security group had this to say: CNBC: Yeah, so I think that nothing is ever impossible.

Galido
MAY 24, 2016
Here are some free software that conform to this security standard, i.e. triple data overwriting for the destruction of remains of sensitive data. Once a file is ‘Securely Deleted’ no one can undelete it. Securely Wipe Free Disk Space: This will securely wipe all free space on the disk. a, b, or m.

A Screw's Loose
MAY 30, 2012
There have to be certain parameters around security and usability that need to be met, but that does not preclude the two major mobile device OS’s currently on the market. link] Mark Page. Pingback: Is ‘bollocks’ the B in BYOD? Let’s be clear that not every device qualifies as usable yet. Nonprofit HR. Uncategorized.

Sean Daniel
JUNE 17, 2011
The server will automatically redirect [link] requests to the secured by SSL https:// URLs When you have finished the router configuration portion of remote access, you should choose to Set up your domain name. Click Next on the Getting started page of the wizard When manually configuring a domain name, the server assumes you already own it.

Venture Beast
NOVEMBER 17, 2021
The Stellar Cyber platform ingests data from multiple systems to establish a full view of users, networks, applications, and resources. Read More.

Galido
OCTOBER 9, 2018
Anyone trying to access any of this information is immediately redirected to a landing page that displays text about restricted access. Security From Online Hackers & Information/Identity Theft. For example, the car needs to get from Point A to Point B. This car is on the wanted list of the police in Point B.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content