How SAST and Mayhem Work Together for Comprehensive Application Security Testing
ForAllSecure
DECEMBER 20, 2022
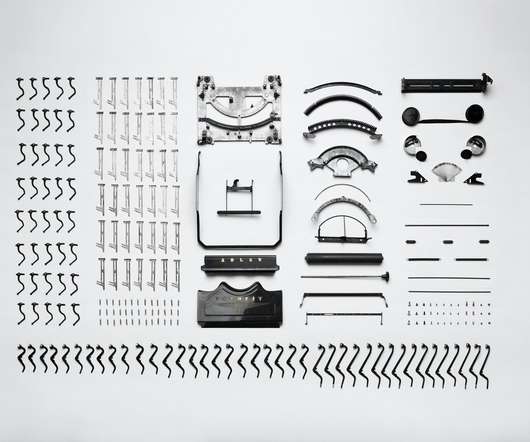
Software application vulnerabilities fall into three different risk categories : Known Known : Known Knowns are identifiable risks that are known to lead to compromise. For the purpose of this blog post, we will focus on how SAST and Mayhem work together to identify both known-unknown and unknown-unknown risks.















Let's personalize your content