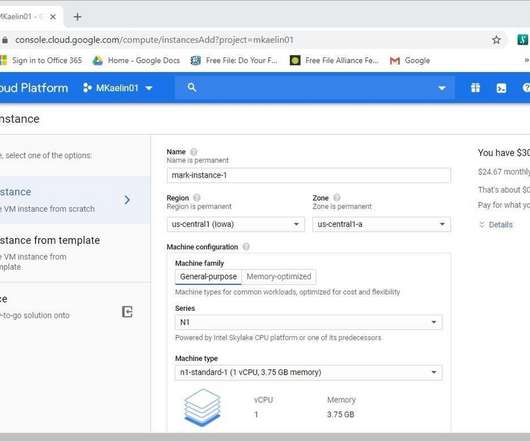
How to create a virtual machine in Google Cloud Platform
Tech Republic Data Center
NOVEMBER 8, 2022
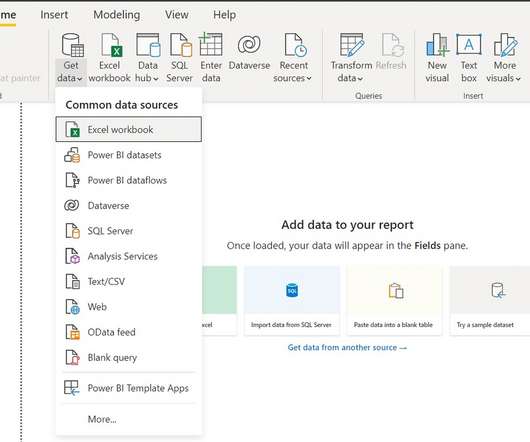
The key component of cloud-based computing is the virtual machine. Creating a VM using Google Cloud Platform is simple, but there are some decisions to make. The post How to create a virtual machine in Google Cloud Platform appeared first on TechRepublic.







































Let's personalize your content