macOS Devices Targeted by Infostealer Malware
IT Toolbox
APRIL 1, 2024
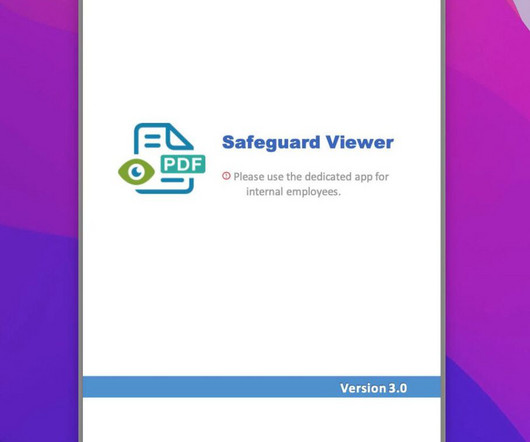
The post macOS Devices Targeted by Infostealer Malware appeared first on Spiceworks. Learn more about the implications of the attacks and the strategies used by threat actors to steal the credentials of their victims.











































Let's personalize your content