Your AST Guide for the Disenchanted: Part 4
ForAllSecure
OCTOBER 6, 2020
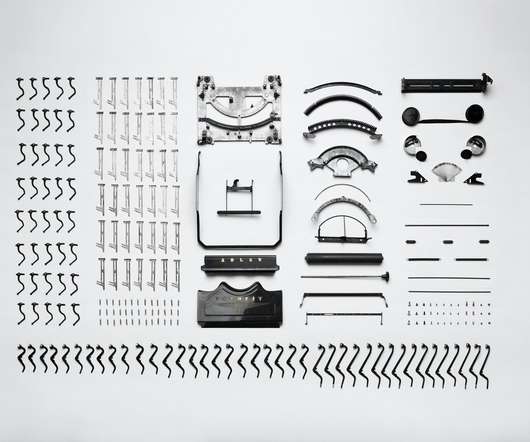
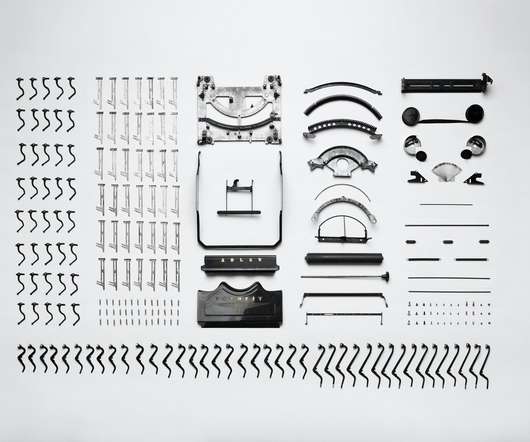
In today’s post, we’ll focus on how software composition analysis can help you address those known vulnerabilities. Developing applications works the same way. Organizations leverage an intricate supply chain to source chunks of code or whole applications as the building blocks of their larger applications.

















Let's personalize your content