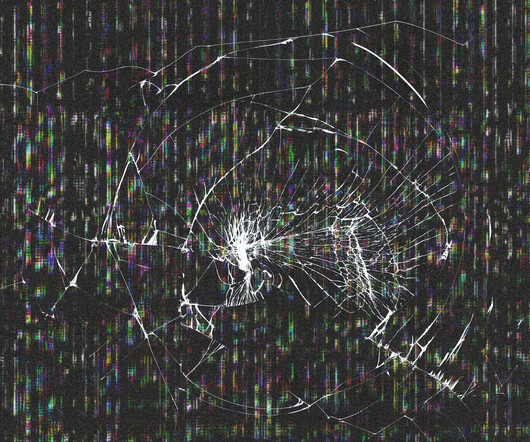
How can such a small file do so much damage?
Dataconomy
NOVEMBER 7, 2023
For example, an attacker might send a zip bomb to a company in an attempt to disable its antivirus software. Once the antivirus software is disabled, the attacker can then send other malware to the company’s computers. A zip bombing like this can take a very long time to fix manually if backups are not taken in short periods.










Let's personalize your content