There’s a better way to protect yourself from hackers and identity thieves
Vox
MAY 6, 2021
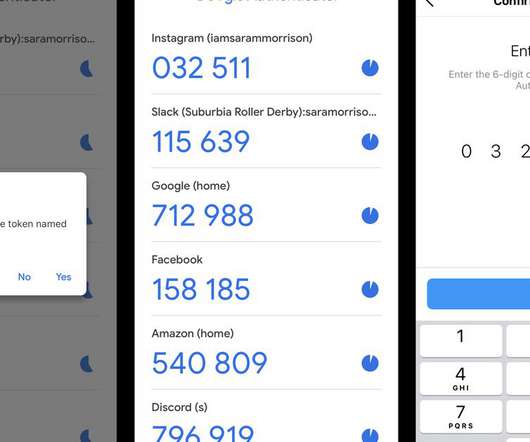
Authenticator apps like Google Authenticator might seem intimidating, but they’re easy to use and safer than texts. If you’re using texts for two-factor authentication, it’s time to change to an app. And you always use two-factor authentication, or 2FA. How to choose and use an authenticator app. No, “Passw0rd!”




















Let's personalize your content