Can AI Improve Your Loyalty Program?
Forrester IT
MARCH 26, 2024
Learn about the potential of predictive AI — and, now, generative AI — in enhancing loyalty programs and strategies.
 Programming Related Topics
Programming Related Topics 
Forrester IT
MARCH 26, 2024
Learn about the potential of predictive AI — and, now, generative AI — in enhancing loyalty programs and strategies.

Forrester IT
APRIL 10, 2024
Most marketing leaders run top-level brand and reputation programs as a primary way of building awareness. These are the advertising or thought leadership initiatives intended to provide a compelling yet broad brand story — but they often aren’t well connected to buyer needs and demand programs.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Forrester IT
OCTOBER 25, 2022
Today, brands leverage loyalty programs to acquire and retain customers, particularly those they lost during the height of the pandemic. But loyalty programs are a symbiotic relationship: Consumers look to programs for better experiences and cost savings, especially in light of the current economic crisis.
IT Toolbox
SEPTEMBER 13, 2023
Here are 12 articles to help you better your programming knowledge on Programmer’s Day 2023. The post 12 Articles To Boost Your Programming Career appeared first on Spiceworks.
Advertiser: ZoomInfo
In a recent survey with Demand Gen Report, we found 59% of experienced practitioners (those with ABM programs more than a year old) indicated their ABM programs are meeting or greatly exceeding their expectations, while only 45% of novices (those with ABM programs less than one year old) could say the same.

Forrester IT
APRIL 4, 2024
Get ready to be inspired by these best-practice program implementations across B2B marketing, sales, and product. We reveal which eight companies will be honored at B2B Summit North America in May.

IT Toolbox
APRIL 23, 2024
The European Commission has raised concerns about TikTok Lite’s rewards program in the region and threatened suspension over addiction risks. Find out more about the program and the problems associated with it. The post TikTok Lite Faces Scrutiny in the EU Over Potentially Addictive Rewards Program appeared first on Spiceworks Inc.
Advertisement
Need to go remote or move your training programs online? Download this guide to identify and overcome the biggest eLearning challenges so you can pick the perfect LMS without wasting time, money, and effort, even if you are just starting your eLearning journey.
Advertiser: ZoomInfo
But none of this is possible without the most important element of a successful ABM program: good data. Running an ABM program on data you don’t trust means wasted time, resources, and lost revenue. The benefits of account-based marketing are clear: internal alignment, shorter sales cycles, higher conversion rates.
Advertiser: ZoomInfo
Research shows that nearly three-quarters of marketers (74%) already have the resources needed to build successful ABM programs. According to several business analysts and practitioners, ABM is a necessity for creating more predictable revenue.
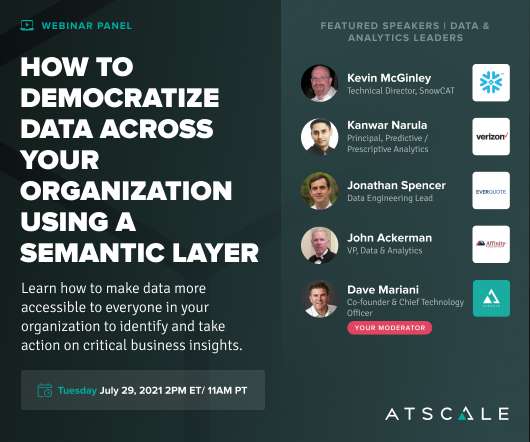
Speaker: speakers from Verizon, Snowflake, Affinity Federal Credit Union, EverQuote, and AtScale
The impact that data literacy programs and using a semantic layer can deliver. In this webinar you will learn about: Making data accessible to everyone in your organization with their favorite tools. Driving a self-service analytics culture with a semantic layer. Using predictive/prescriptive analytics, given the available data.

Advertiser: ZoomInfo
talking points, we thought it would be more helpful to examine an ABM program that ZoomInfo executed. So, what does ABM look like in 2022? Instead of wading through a series of vague “how-to kick-start your ABM strategy!” In just 90 days, we were able to increase our pipeline by 114% and the customer base for this particular product by 30%.

Advertiser: ZoomInfo
While B2B research suggests organizations are thriving through successful ABM programs, getting just one campaign off the ground is more difficult than it seems. Download ZoomInfo’s latest eBook to learn about the three most common mistakes organizations make while executing an ABM program, including: Poor account selection process.

Speaker: Andrew Ysasi, Vice President of Advocacy for Vital Records Control, President of IG GURU®, MS, FIP, FIIM, CIPM, CIGO, CISM, PMP, CRM, IGP, CIP, CSAP
Countless data breaches, hacks, and the never-ending changes being made to privacy regulations illustrate why it is critical for data-driven organizations to develop information privacy strategies that fill the gaps of their existing data management programs. Information privacy is a critical part of an IG program. Set up a program.

Speaker: Megan Brown, Director, Data Literacy at Starbucks; Mariska Veenhof-Bulten, Business Intelligence Lead at bol.com; and Jennifer Wheeler, Director, IT Data and Analytics at Cardinal Health
Our featured speakers will share practical guidance and examples from effective programs that help with data skill-building, improving decision-making, and fostering a data literate culture – so everyone at your organization can confidently read, write, analyze and communicate with data.
Let's personalize your content