Insider Threat: A perspective on how to address the increasing risk
CTOvision
OCTOBER 28, 2015
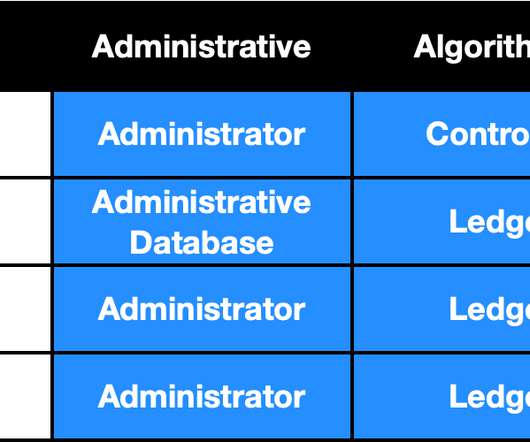
Cyber security is one of the highest priority topics for organizations today. However, in June of 2013, a systems administrator at the National Security Agency (NSA) reminded us of the threat that already exists within an organization, behind the protection of its sophisticated, complex perimeter security.
















Let's personalize your content