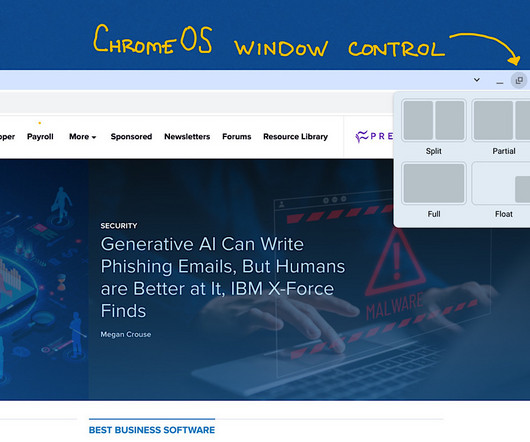
How to Use Hidden Browser Window Controls in ChromeOS
Tech Republic
NOVEMBER 14, 2023
Learn how to use the hidden browser window controls in ChromeOS for an enhanced browsing experience with this step-by-step guide.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Tech Republic
NOVEMBER 14, 2023
Learn how to use the hidden browser window controls in ChromeOS for an enhanced browsing experience with this step-by-step guide.

The Verge
NOVEMBER 6, 2020
percent of computer users still are on Windows 7 — even though Microsoft no longer supports it for free. If you have an older system but are worried that it won’t support Windows 10 — or if you simply don’t want to deal with Windows anymore — I have a suggestion: Switch to desktop Linux. Which Linux?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CTOvision
APRIL 20, 2014
R runs on a wide variety of systems, including Mac, Windows, Linux and Unix. You will immediately see links to Linux, Mac and Windows versions of R. Download and install the one for your system. See how easy that was. Now you have R running on your system. Open it, and look around. That’s it.

CIO Business Intelligence
DECEMBER 4, 2023
Its versatility, reliability, stability, and open-source and third-party libraries and frameworks make developing and running applications very efficient. What operating systems and architectures do you support? In January 2023, Oracle changed its licensing and/or pricing for Java for the fourth time in four years.

Scott Lowe
MARCH 15, 2024
Networking Lee Briggs (formerly of Pulumi, now with Tailscale) shows how to use the Tailscale Operator to create “free” Kubernetes load balancers (“free” as in no additional charge above and beyond what it would normally cost to operate a Kubernetes cluster). Thanks for reading! This is a handy trick.

Dataconomy
DECEMBER 25, 2023
Soon, custom firmware emerged, expanding the attack canvas to Android and Windows, spamming users with unwanted advertisements, and potentially compromising device security. Pen-testing tool Flipper Zero was eventually used for Bluetooth spam attacks on the iOS operating system ( Image credit ) What is Wall of Flippers?

Kitaboo
MARCH 26, 2024
How to Choose the Right Software for eBook Publishing and Conversion? How to Choose the Right Software for eBook Publishing and Conversion? Consider Your Operating System Verify that your shortlisted software works with your operating system. Table of Contents I.

GeekWire
DECEMBER 30, 2023
” The need for strong open-source models: “The consolidation of power in AI is a huge risk. The countervailing forces are, number one, open source models. A great analogy here is what we’ve seen in operating systems. We had Windows, which billions and billions and dollars went into.

CTOvision
JANUARY 28, 2015
On the next page, you will be given a choice to download for Linux, Windows or Mac. . I will continue this with an example of how to download on a Mac. The first choice you must make is to determine what operating system your computer is running. CTO Carnegie Mellon University R'

Kitaboo
APRIL 23, 2024
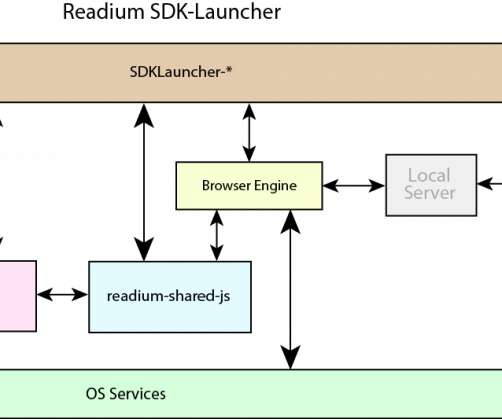
The SDK ensures seamless delivery across various devices and operating systems to provide readers with flexibility in how they consume your content. KITABOO also integrates with your existing Learning Management Systems (LMSs), making it a valuable tool for educational institutions.

Galido
JANUARY 12, 2017
It is recommended that users install these antivirus softwares on the Linux operating system that can be downloaded via Internet. Linux operating systems work on a completely different principle compared to Windows systems and, therefore, viruses made for Windows can not be activated and spread to computers installed with Linux.
Kitaboo
MAY 19, 2020
The Open Source Foundation aims to develop technology for expediting the adoption of ePUB3 and the Open Web Platform by the Digital Publishing Industry. It strives to deliver leading-edge functionality that is fully specified, free, open, and interoperable. How-To Guide: How to Automate PDF to ePub3 Conversion.

Kitaboo
JULY 2, 2020
When it comes to MOBI eBook format, it is specialized for Kindle devices, and since Kindle is not an open-source format, the eReaders which support MOBI are not many. Guide: How to Automate PDF to ePub3 Conversion. Works well with different operating systems including Windows, macOS, and Linux.

Galido
OCTOBER 18, 2018
“Everyone should learn how to program a computer, because it teaches you how to think”…Steve Jobs. When programming applications for the operating system of Apple, iOS, and therefore to create apps for iPhone and iPad, you must use the Objective-C language. Kotlin is an open source language.

Scott Lowe
APRIL 19, 2019
This article discusses four open source secrets management tools. Many organizations prefer to use two-factor authentication (2FA) to help protect their systems. ” Operating Systems/Applications. John Harris explains how to use dynamic configuration discovery in Grafana. Very handy!

ForAllSecure
JUNE 16, 2020
The Google Chrome web browser, for example, is used on billions of devices and is completely open source, allowing any attacker to review exactly how the software works. So how does Google check and protect Chrome’s millions of lines of code? How to get started? Is fuzzing right for you?

ForAllSecure
JUNE 16, 2020
The Google Chrome web browser, for example, is used on billions of devices and is completely open source, allowing any attacker to review exactly how the software works. So how does Google check and protect Chrome’s millions of lines of code? How to get started? Is fuzzing right for you?

ForAllSecure
JUNE 16, 2020
The Google Chrome web browser, for example, is used on billions of devices and is completely open source, allowing any attacker to review exactly how the software works. So how does Google check and protect Chrome’s millions of lines of code? How to get started? Is fuzzing right for you?

Linux Academy
APRIL 30, 2019
That viruses and malware are Windows problems is a misnomer that is often propagated through the Linux community and it’s an easy one to believe until you start noticing strange behavior on your system. Introduction to Python Development — This course is designed to teach you how to program using Python.

Galido
MARCH 19, 2019
These areas of IT include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Here you can find latest news and insights from Google on security and how to be safe on the Internet. CIO Dashboard. Dark Reading.

Scott Lowe
APRIL 15, 2022
Although Linux is often considered to be superior to Windows and macOS with regard to security, it is not without its own security flaws. Diego Sucaria shows how to use an SSH SOCKS proxy to access private Kubernetes clusters. Operating Systems/Applications. Cloud Computing/Cloud Management. Career/Soft Skills.

Scott Lowe
NOVEMBER 25, 2020
Open source has become so critical to so many aspects of our computing infrastructure. Teammate Eric Shanks shows folks how to use ytt to customize a TKG deployment. I recently stumbled across Ricardo Sueiras’ “AWS open source news and updates” posts. Operating Systems/Applications.

Scott Lowe
JANUARY 17, 2020
dll , a core Windows cryptographic component) that was rumored to be fixed the next day (January 14) on the first “Patch Tuesday” of 2020. How about a bash “wrapper” for working with AWS resources from the command line? Operating Systems/Applications. This is kind of cool.

SPF13
MARCH 20, 2015
In the last few years open source has transformed the software industry. From Android to Wikipedia, open source is everywhere, but how does one succeed in it? What Every Successful Open Source Project Needs. spf13 Chief Operator @ Docker? Open Source is taking over the world.

Scott Lowe
DECEMBER 29, 2016
Operating Systems/Applications. could make RDP connections to modern Windows systems. could make RDP connections to modern Windows systems. Jase McCarty talks about how to backup or recover storage policy-based management (SPBM) profiles. Way to go, Daniel! Virtualization. Neat trick!

Galido
MAY 1, 2019
These areas of tech include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Here you can find latest news and insights from Google on security and how to be safe on the Internet. CIO Dashboard.

Galido
MARCH 22, 2019
These areas of tech include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Here you can find latest news and insights from Google on security and how to be safe on the Internet. CIO Dashboard.

Scott Lowe
MARCH 23, 2017
As opposed to just encrypting data at the transport level (although Acra does that between components of its architecture) or just encrypting data at the storage level (using an encrypted file system or similar), Acra targets encrypting data at the table/row/column level within a database. Acra is open source and available via GitHub.

Scott Lowe
JANUARY 19, 2018
Via Maish Saidel-Keesing, I saw this post about 10 open source Kubernetes tools for highly effective SRE and Ops teams. Operating Systems/Applications. Ariya Hidayat shows how to run Debian under WSL (Windows Subsystem for Linux). Klaus Aschenbrenner shares how he designed his VMware vSAN-based home lab.

Scott Lowe
APRIL 27, 2018
Cilium, the open source project working to bring eBPF-powered networking and security to Kubernetes environments, has hit the 1.0 Gergely Nemeth shares how to leverage skaffold so you can use Kubernetes for local development. Operating Systems/Applications. Here’s YAKI (Yet Another Kubernetes Introduction).

Scott Lowe
JANUARY 28, 2016
And while we are on the topic of Linux and open source in the networking industry…read this entertaining and informative article on the importance of (truly) open source libraries in networking. The project itself is open source and hosted on GitHub. Operating Systems/Applications.

Scott Lowe
JANUARY 28, 2016
And while we are on the topic of Linux and open source in the networking industry…read this entertaining and informative article on the importance of (truly) open source libraries in networking. The project itself is open source and hosted on GitHub. Operating Systems/Applications.

Galido
MARCH 19, 2019
These areas of IT include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Here you can find latest news and insights from Google on security and how to be safe on the Internet. CIO Dashboard. Dark Reading.

Dataconomy
APRIL 24, 2024
Ollama, a free, open-source tool, enables the operation of various large language models, such as Llama 3, on personal computers, even those with limited capabilities. It utilizes llama.cpp, an open-source library that optimizes the performance of LLMs on local machines with minimal hardware demands.

Linux Academy
APRIL 29, 2019
That viruses and malware are Windows problems is a misnomer that is often propagated through the Linux community and it’s an easy one to believe until you start noticing strange behavior on your system. Introduction to Python Development — This course is designed to teach you how to program using Python.

Galido
SEPTEMBER 25, 2019
These areas of tech include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Here you can find latest news and insights from Google on security and how to be safe on the Internet. CIO Dashboard.

Scott Lowe
APRIL 24, 2020
Josh VanDeraa shows how to use Netmiko, NTC-Templates, Telegraf, Prometheus, and Grafana for monitoring VPN infrastructure (a more critical piece of infrastructure these days given all the remote work going on). I recently stumbled across this regular list of AWS open source news and updates by Ricardo Sueiras.

Scott Lowe
FEBRUARY 9, 2018
and how to use the Python SDK for NSX-T. Operating Systems/Applications. The Windows Server team managed to shrink the size of the Windows Server Core container image by about 60%; get more details here. I’ve been a Dash user for a while and I can attest to how handy it can be.

Scott Lowe
SEPTEMBER 23, 2015
No problem, Ravello Systems has a blog (and a blueprint) to help you set all this up. Darren O’Connor has an article describing how he used bird to pull global BGP route counts. Bird , by the way, is an open source routing daemon for Linux, *BSD, and other UNIX-like operating systems.). Servers/Hardware.

Scott Lowe
MARCH 2, 2017
Skydive is (in the project’s own words) an “open source real-time network topology and protocols analyzer.” Operating Systems/Applications. Here’s a list of some open source Docker-related tools that developers may find useful. Alan Renouf shows you how to retrieve NVMe storage device details using PowerCLI.

Scott Lowe
DECEMBER 8, 2016
Will Robinson talks about how to structure your Ansible playbooks in the context of using Ansible to control your network gear. This is an interesting project to watch, I think—it’s porting OVN (Open Virtual Network) from a “traditional” OvS back-end to an IOVisor-based back-end (IOVisor implements the data plane in eBPF). Networking.

ForAllSecure
DECEMBER 2, 2021
You’ll want someone with years of pen testing experience, some one who knows the operating system like no other. So in general, an operating system that eventually allows you to gain more information about the context within which attack was made. Maybe your first concern is to make sure the company is functional.

Scott Lowe
SEPTEMBER 3, 2014
To help resolve this issue, Cumulus Networks (and possibly Metacloud, I’m not sure of their involvement yet) has release an open source project called vxfld. SDN Central has a nice write-up on the need for open efforts in the policy space, which includes the Congress project. Operating Systems/Applications.

ForAllSecure
AUGUST 12, 2019
Open Source Security Podcast helps listeners better understand security topics of the day. Hosted by Kurt Seifried and Josh Bressers, the pair covers a wide range of topics including IoT, application security, operational security, cloud, devops, and security news of the day. The full transcript is also available below.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content