Atomic Stealer Distributes Malware to Macs Through False Browser Downloads
Tech Republic Security
NOVEMBER 22, 2023
Atomic Stealer malware advertises itself through ClearFake browser updates disguised as Google's Chrome and Apple’s Safari.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
NOVEMBER 22, 2023
Atomic Stealer malware advertises itself through ClearFake browser updates disguised as Google's Chrome and Apple’s Safari.

SecureWorld News
JULY 11, 2023
Apple has issued a new round of Rapid Security Response (RSR) updates to address a Zero-Day bug exploited in attacks and impacting fully-patched iPhones, Macs, and iPads. By default, your device automatically applies Rapid Security Responses. Mac: Choose Apple menu > System Settings.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
OCTOBER 13, 2022
The post New Alchimist attack framework hits Windows, Linux and Mac appeared first on TechRepublic. The attack framework of probable Chinese origin used by cybercriminals has been discovered.

The Verge
APRIL 26, 2021
Apple has just released macOS 11.3, It’s probably worth updating your Mac to it as soon as you can — not only because it comes with some new features, including improvements for running iPhone and iPad apps on M1 Macs and updates to Apple Music and Podcasts, but it also fixes a major security flaw. alongside iOS 14.5.

The Verge
JUNE 29, 2021
Microsoft’s big security push is complicated Microsoft has had six years to prepare for the launch of Windows 11, but the company is still struggling to explain its new hardware requirements. It’s an unusual surprise if you purchased a new PC for Windows 10, or perhaps you have a perfectly capable machine that’s even older.

SecureWorld News
JUNE 1, 2023
This discovery raises concerns about system integrity, the installation of undeletable malware, and the potential compromise of private user data. Microsoft promptly reported the issue to Apple, resulting in the release of security updates to address the vulnerability. Occasionally, even those built-in protections are breached.

The Verge
MAY 27, 2021
Apple proceedings kicked off, and the news has been relentless. 1] Apple keeps iMessage closed in order to sell more iPhones. 3] Apple pulled out all the stops to keep Netflix selling subscriptions on the iPhone. But for a while, Apple was willing to do just about anything to keep Netflix from giving in to the obvious economics.

Tech Republic Security
NOVEMBER 28, 2016
The new report details increased risks to Android and Apple products and the top 10 Windows malware programs of 2016. Here's what your business needs to know to stay safe.
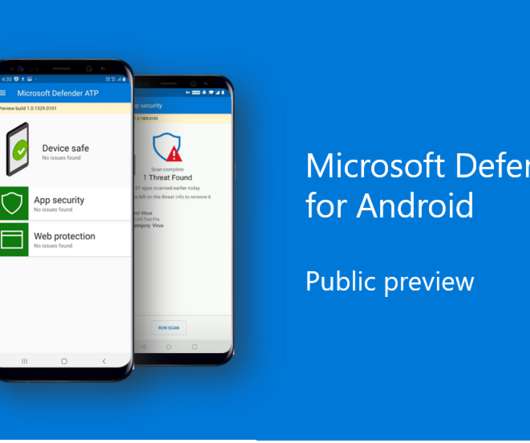
The Verge
JUNE 23, 2020
The software giant revealed that Windows Defender was making its way to both iOS and Android earlier this year , but didn’t fully detail what to expect. The public preview for Android will include protection against phishing and go a step further than Google’s built-in malware protection to offer signature-based malware detection.

Galido
DECEMBER 28, 2018
Information Technology Blog - - Data Security and its Importance on the Internet - Information Technology Blog. Users are partly responsible for their own safety, and often the lack of security updates and knowledge of security protocol has made them vulnerable to malicious attacks. Why Should You Care?

Network World
FEBRUARY 1, 2017
Macs are really no more secure than a PC, but for many years there just weren’t as many out there because of the expense of the hardware and other issues. The PC attack surface is much wider; therefore, criminals develop malware that works on PCs because the payout is much higher.

Scott Lowe
AUGUST 27, 2021
Teri Radichel uses some basketball analogies to explain why defensive (proactive) security strategies are more desirable than reactive security strategies. Sentinel Labs outlines a major malware push that is bypassing Apple’s malware protections. (And since Kevin didn’t define TDP—shame, shame!—see

Galido
MARCH 19, 2019
Information technology is the use of any tech devices, infrastructure, software and processes to create and process, store, secure and exchange all forms of digital data. Our articles are typically focused on software recommendations, business, security, interesting topics and search engine optimization and marketing. Search Security.

Galido
MAY 1, 2019
These areas of tech include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Security Tech Blogs. Techworld Security Blog. They offer useful relevant topics on security and tech security news.

Scott Lowe
AUGUST 27, 2021
Teri Radichel uses some basketball analogies to explain why defensive (proactive) security strategies are more desirable than reactive security strategies. Sentinel Labs outlines a major malware push that is bypassing Apple’s malware protections. (And since Kevin didn’t define TDP—shame, shame!—see

Galido
MARCH 22, 2019
These areas of tech include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Security Tech Blogs. Techworld Security Blog. They offer useful relevant topics on security and tech security news.

Galido
SEPTEMBER 25, 2019
These areas of tech include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Security Tech Blogs. Techworld Security Blog. They offer useful relevant topics on security and tech security news.

Galido
MARCH 19, 2019
Information technology is the use of any tech devices, infrastructure, software and processes to create and process, store, secure and exchange all forms of digital data. Our articles are typically focused on software recommendations, business, security, interesting topics and search engine optimization and marketing. Search Security.

A Screw's Loose
APRIL 11, 2013
As my first three blog posts this week have been related to security I felt it was only fair that I continue this week with another one in the same vein. I participated in a tweet chat yesterday that was premised on the fact that mobile malware exists and what can you do to prevent it on your devices in the enterprise.

A Screw's Loose
OCTOBER 26, 2011
Windows Phone 7 and why it doesn’t suck! They have since released Windows Phone 7.5 I am looking forward to seeing where Microsoft decides to take Windows Phone in its next iteration known as Apollo and am optimistic that it will make better in roads in its second year as a mobile OS. Windows Phone. Standard Disclaimer.

A Screw's Loose
MARCH 26, 2013
People have been struggling for years sitting in their cubicles and offices, chained to their mammoth desktop running some sort of Windows (most likely Windows XP). Didn’t you use Apple Maps? Windows Phone. The majority of workers though, are looking for a way out. What do you mean you can’t get data in the building?

ForAllSecure
NOVEMBER 24, 2020
In this episode I talk about how Heartbleed (CVE 2014-0160) was found and also interview Rauli Kaksonen, someone who was at Codenomicon at the time of its discovery and is now a senior security specialist at the University of Oulu in Finland, about how new security tools are still needed to find the next big zero day. Apple Podcasts.

ForAllSecure
NOVEMBER 24, 2020
In this episode I talk about how Heartbleed (CVE 2014-0160) was found and also interview Rauli Kaksonen, someone who was at Codenomicon at the time of its discovery and is now a senior security specialist at the University of Oulu in Finland, about how new security tools are still needed to find the next big zero day. Apple Podcasts.

A Screw's Loose
SEPTEMBER 26, 2012
It didn’t help that security realized that the new devices were around and they weren’t locked down blackberries. You have a new OS from Apple once a year, new devices from them at least twice a year, then you have Android which may have 57 different models and all at a different OS level. Windows Phone. Uncategorized.

ForAllSecure
NOVEMBER 24, 2020
In this episode I talk about how Heartbleed (CVE 2014-0160) was found and also interview Rauli Kaksonen, someone who was at Codenomicon at the time of its discovery and is now a senior security specialist at the University of Oulu in Finland, about how new security tools are still needed to find the next big zero day. Apple Podcasts.

A Screw's Loose
SEPTEMBER 24, 2012
Apple released iOS 6 on Wednesday and then released the iPhone 5 on Friday. As Apple is a consumer tech company, they have always allowed users to make the decision on whether they updated or not. One of my customers was talking about securing his datacenters starting from the fact that everything outside is unsecure by nature.

A Screw's Loose
JULY 2, 2013
We spend hours talking about the differences between Android and Apple, or whether we should allow Microsoft to play in our sandbox. We see this as a way to protect our intellectual property and keep our corporate data secure. Windows Phone. We have this tendency to get stuck on the trivial things. Uncategorized. Crapplications.

A Screw's Loose
NOVEMBER 2, 2011
The question they were asking in the Podcast was really “Did Nokia do enough with Windows Phone 7?” The big piece of news from Nokia was not that they were releasing 2 Windows Mobile Phones but that they were releasing the Asha line and renewing their focus on emerging markets. Don’t get me wrong, as far as a Windows Phone 7.5

Chief Seattle Greek Blog
OCTOBER 30, 2010
Yup, we give you a standard HP model with Windows XP, Office 2007 and Anti-Virus loaded on it. Yup, here’s your BlackBerry connected to Outlook and locked down from installing any dangerous applications which present a security threat. Cyberterrorists and Malware. You need a computer? You need a smart phone to do your job?

A Screw's Loose
JUNE 26, 2013
I, of course, have Waze in case I rent a car and use either Google Maps or Apple Maps if I am on an iDevice for mapping walking directions. Walking around in Amsterdam on Sunday, I camped out right outside an Apple Store for about 10 minutes to make a free Facetime call with my wife. Windows Phone. Uncategorized. Crapplications.

A Screw's Loose
OCTOBER 16, 2012
As much as we like to think that people switch from Apple to Android or vice-versa, most of the time you end up locked in to whichever platform you’re on due to the apps that you have. They don’t think about security or the data, they just want to be able to do their work when and where they need to. Windows Phone. Innovation.

A Screw's Loose
MAY 14, 2012
Their second objective was just as important, as they were erecting a paywall, they didn’t want to have to pay Apple a 30% cut of their revenues. Another reason to go all native might be you are only developing for one platform, apple, android etc, and have no plans to go anywhere else, might make sense to go all native.

A Screw's Loose
JUNE 11, 2013
This isn’t limited to Apple devices either, one could use Skype or Ustream to do the same thing. Windows Phone. I watched the whole game including my daughter scoring the tying goal from my computer in the comfort of the house. To be fair, it wasn’t ESPN quality but it came out pretty good. Uncategorized. Tags Applications.

ForAllSecure
JANUARY 15, 2021
Apple Podcasts. I suppose such things happen, but what I remember was her telling her surprise when the system booted up and the Windows 95 splash screen came up … wait, what? Microsoft, for example, stopped patching Windows XP for security vulnerabilities in 2014. Especially in the world of security standards.

ForAllSecure
JANUARY 15, 2021
Apple Podcasts. I suppose such things happen, but what I remember was her telling her surprise when the system booted up and the Windows 95 splash screen came up … wait, what? Microsoft, for example, stopped patching Windows XP for security vulnerabilities in 2014. Especially in the world of security standards.

A Screw's Loose
FEBRUARY 15, 2012
They brought up security concerns and slowed things down for about a year. When Apple introduced the App store, the gates swung open, as there were just too many requests to use these devices. ” via cloud enabled services, securely and cheaper then ever. Windows Phone. Uncategorized. Tags Applications. Innovation.

A Screw's Loose
JUNE 24, 2013
We hear complaints about going through security all the time, bad flights, bad hotel rooms and the list goes on and on. One of the benefits of all these are that they use the same apple lightning adapter on their charge/sync cable. Traveling through TSA security checkpoints is always fun. Windows Phone. Uncategorized.

The Verge
APRIL 8, 2021
New filings show both sides’ legal strategies at work On May 3rd, Fortnite publisher Epic Games will finally have its day in court, forcing Apple to defend kicking Fortnite off the iOS App Store last year. The heart of the case is the so-called App Store tax — a 30 percent surcharge Apple collects on purchases made through the App Store.

A Screw's Loose
JUNE 4, 2012
This means that they will be moving data into apps that work for them but that may not be as secure or reliable as what you want them to use. Good post, should be pointed out that the majority of tabletsphones supported by enterprise have MS, CE & Apple clients for multi media experience (codecsdrives, etc.) Windows Phone.

The Verge
DECEMBER 14, 2021
How Amazon, Google, Apple, and Samsung will work with Matter, and which products you should buy. From platform owners like Apple, Google, and Amazon to major manufacturers such as Samsung and LG and smaller, accessory-focused players like Nanoleaf, Eve, and Wyze, there’s an unprecedented industry coalition behind Matter. Image: Apple.

A Screw's Loose
MAY 7, 2012
I, for example, am writing this post on my iPad using Apple’s Pages. Windows Phone. The point I had made then and many other times is that Microsoft Word, in its desktop incarnation has way to many features that aren’t really necessary on a mobile device. Do I need to be doing mathematical formulas in this post? Innovation.

The Verge
JUNE 18, 2020
30 percent is unconscionable,” says Congressman David Cicilline Apple is acting like a monopolist and a bully, according to the chairman of the House antitrust subcommittee. There’s been rumbling discontent from developers about how Apple runs the iPhone App Store for years now, but the Hey situation has brought it to startling light.

A Screw's Loose
MARCH 13, 2012
I spent the whole presentation on Securing the Mobile Enterprise building up to the the fact that most businesses were approaching mobile strategy using legacy thinking and now was the time to get out of the habit. We look to secure every device and every endpoint. Security makes sure we encrypt our laptops. We manage devices.

ForAllSecure
OCTOBER 29, 2020
While digital voting systems are more secure today, what about the larger ecosystem, starting from the moment you register until your vote is counted? Who’s keeping those systems secure? Apple Podcasts. One of the premiere security researchers that Bowen invited to California was J. Google Podcasts. Amazon Music.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content