Zero Trust
Phil Windley
AUGUST 28, 2023
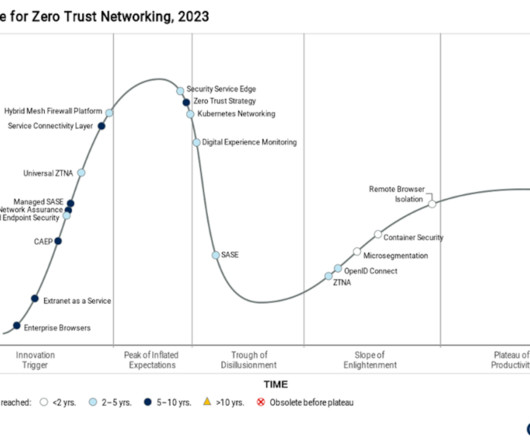
My new book Learning Digital Identity from O'Reilly Media covers many of the topics in this post such as multi-factor authentication, authorization and access control, and identity policy development in depth. Zero Trust is a security framework that is better attuned to the modern era of sophisticated threats and interconnected systems.




























Let's personalize your content