Zero Trust
Phil Windley
AUGUST 28, 2023
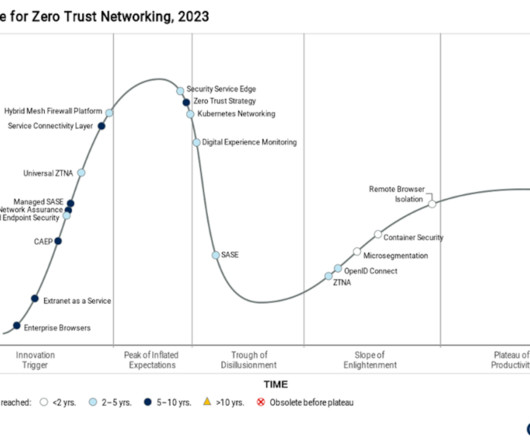
Zero Trust is a security framework that is better attuned to the modern era of sophisticated threats and interconnected systems. As more and more work has gone remote and personal devices like phones, tablets, and even laptops are being used for work, a firewall—virtual or physical—offers less and less protection.
































Let's personalize your content