Deploying Open Source Software in an Age of Global Security Mandates
IT Toolbox
MARCH 22, 2024
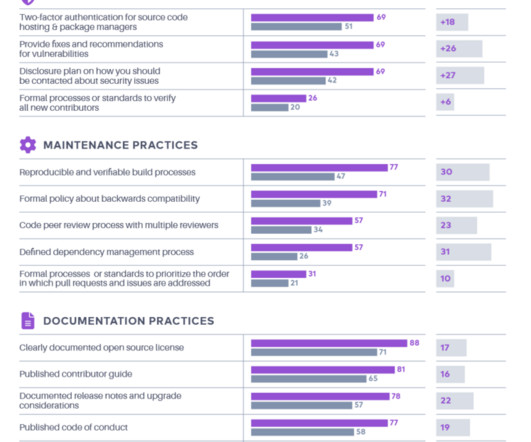
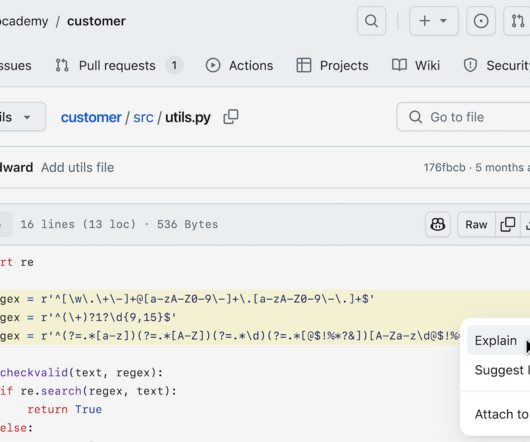
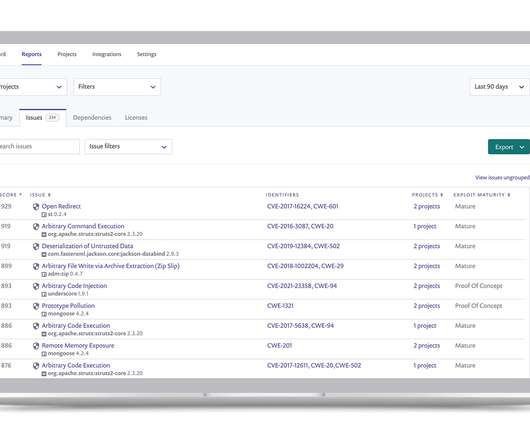
Discover tightened global software security, key regulations, and open-source impacts on compliance and societal resilience. The post Deploying Open Source Software in an Age of Global Security Mandates appeared first on Spiceworks.











































Let's personalize your content