KubeCon + CloudNativeCon Highlights Security for Open Source
Information Week
OCTOBER 15, 2021
Vulnerabilities in the life cycle of open-source software development can start from tiny crumbs but grow into substantial issues.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Information Week
OCTOBER 15, 2021
Vulnerabilities in the life cycle of open-source software development can start from tiny crumbs but grow into substantial issues.

CTOvision
AUGUST 20, 2020
explain how you can stay secure on GitHub on Dark Reading : Open source software is a fact of life for enterprise software developers, and GitHub […]. Read Curtis Franklin Jr.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
DECEMBER 21, 2022
Microsoft has open sourced its framework for managing open source in software development. The post What is Microsoft’s Secure Supply Chain Consumption Framework, and why should I use it? appeared first on TechRepublic.
Venture Beast
MAY 4, 2022
Appwrite has launched a dedicated fund to support open source project maintainers, following shortly after its recent $27 million fundraise. Read More.
Venture Beast
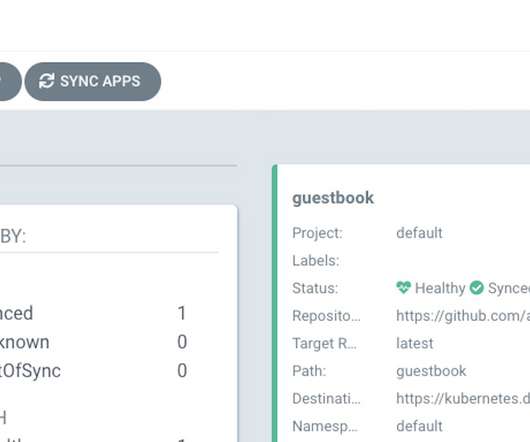
FEBRUARY 3, 2022
A zero day vulnerability with a "high" severity rating affects Argo CD, an open source developer tool for Kubernetes, Apiiro researchers said. Read More.

Venture Beast
OCTOBER 20, 2021
ControlFlag, an AI-powered tool developed by Intel to spot potential issues in software code, has been released in open source. Read More.
CIO Business Intelligence
APRIL 24, 2024
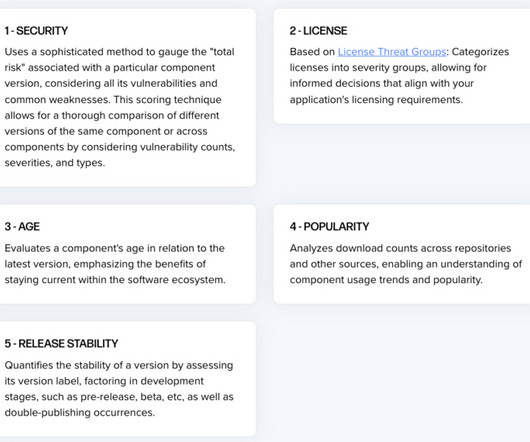
The complexity of the software supply chain (SSC) has the potential to expose your organization to greater risk than ever before. In today’s fast-paced software development landscape, managing and securing the software supply chain is crucial for delivering reliable and trusted software releases.

TechSpot
APRIL 5, 2024
"In addition to improved IT security, cost-effectiveness, and data protection, the use of open-source software also enables seamless collaboration between different systems," officials said. Alongside open-source software development, the goal is to release future development results of the country under free licenses."

Venture Beast
JANUARY 24, 2021
Russia's SolarWinds hack gave it access to data from federal agencies because we haven't secured the software supply chain. Read More.

CIO Business Intelligence
NOVEMBER 13, 2023
No matter the industry, organizations are increasingly looking for ways to optimize mission-critical software development processes. As development teams grapple with the challenge of modernizing their DevOps toolchains, a number of concerns and challenges have followed closely behind. Chief among those challenges?

Tech Republic Security
DECEMBER 20, 2022
Open source software development service has made it easier for developers using its public repositories to keep coding secrets and tokens close to the chest. The post GitHub offers secret scanning for free appeared first on TechRepublic.

CTOvision
NOVEMBER 12, 2014
Dealing with the scale that the internet can deliver, has unfortunately left us with a series of other non-optimal cyber security approaches and solutions. Out of all the problems to deal with subverting bureaucracy to enable security scaling is the hardest. In cybersecurity we’re have a hard time dealing with scale.

IT Toolbox
AUGUST 17, 2022
Smart firms maintain an up-to-date, credible SBOM for their projects that includes a list of all the open source and third-party components that are used to create high-quality, ethical, and secure code. This article discusses SBOM in greater detail.

Network World
MARCH 3, 2017
HackerOne, the company behind one of the most popular vulnerability coordination and bug bounty platforms, has decided to make its professional service available to open-source projects for free. Here at HackerOne, open source runs through our veins," the company's representatives said in a blog post.

SecureWorld News
DECEMBER 13, 2023
Log4j is a widely-used open source Java logging library, and the vulnerability allowed threat actors to execute remote code on servers, potentially leading to unauthorized access and data breaches. Despite widespread awareness and patches issued by software developers, the vulnerability's exploitation remains a persistent threat.

Network World
JULY 11, 2016
Companies that develop enterprise applications download over 200,000 open-source components on average every year and one in every 16 of those components has security vulnerabilities.

ForAllSecure
MAY 4, 2023
Upcoming Events We have two upcoming events planned for May 2023: Webinar: How to Uncover and Address Vulnerabilities in Open-Source Libraries GlueCon Read on to learn more about May’s events. While they provide access to pre-built components and tools, they can also introduce security vulnerabilities into your code.
Tech Republic
OCTOBER 17, 2023
Sonatype's 9th annual State of the Software Supply Chain also covers regulations and how AI could help developers protect organizations from security risks.

CIO Business Intelligence
MARCH 9, 2023
It’s completely intuitive, allows me to perform most tasks in less than 3 clicks, has all the functions that I need to perform banking on-the-go, is constantly updated with new features, comes with great performance and stability and most of all is very secure. Today its offerings include deliveries, mobility, financial services among others.

Tech Republic
AUGUST 29, 2023
GitLab's CISO Josh Lemos on securing CI/CD of software with generative AI tools and how automation enables continuous security in the software development supply chain.

ForAllSecure
JUNE 7, 2023
Last month, we participated in GlueCon and hosted a webinar on uncovering vulnerabilities in open source software. Mayhem Unleashed Webinar: Discover our Next Generation Security Testing Solution Are you ready to revolutionize your DevSecOps workflows? Stay tuned! We hope to see you there! Look no further! The challenge?

The Verge
MARCH 21, 2022
As the Russian invasion of Ukraine draws on, consequences are being felt by many parts of the technology sector, including open-source software development. In addition, various content and malicious code can be embedded in freely distributed libraries used for software development.

SecureWorld News
JULY 14, 2022
The Department of Homeland Security's (DHS) Cyber Safety Review Board (CSRB) has released its first report , providing detailed information on the Log4j vulnerability. The Board was created to " review and assess significant cybersecurity events" so that both the public and private sector can improve their security posture.

SecureWorld News
MAY 19, 2022
Meanwhile, legacy AppSec systems and processes have impeded security teams from being able to scale at the speed of DevOps with very little visibility or control over security risks. Security teams are entirely unprepared to govern and secure the modern SDLC in this agile world. What are security guardrails?

The Verge
FEBRUARY 10, 2021
Security researcher Alex Birsan has found a security vulnerability that allowed him to run code on servers owned by Apple, Microsoft, PayPal, and over 30 other companies ( via Bleeping Computer ). Illustration by Alex Castro / The Verge. For example, I’ve worked on websites that had to convert text files to webpages in real time.

CIO Business Intelligence
MAY 1, 2023
Software agility also means that if the organization would like to leverage a new technology to innovate and remain competitive, teams can easily deliver an app that does just that. This will help in optimizing application development and operations, and strengthening security and compliance. Software Development

CIO Business Intelligence
FEBRUARY 24, 2023
By Zachary Malone, SE Academy Manager at Palo Alto Networks The term “shift left” is a reference to the Software Development Lifecycle (SDLC) that describes the phases of the process developers follow to create an application. How did the term shift-left security originate?

CIO Business Intelligence
JULY 13, 2022
Shadare, along with Orca Security advisory CISO Andy Ellis and Spire Security Vice President of Research Pete Lindstrom, will share cybersecurity metrics that matter as part of CSO’s Future of Cybersecurity Summit , taking place virtually July 19-20. One risk mitigation strategy is to move away from passwords to more secure protocols.

ForAllSecure
MAY 30, 2023
DevSecOps is more than just a buzzword—it's a game-changing approach for modern software development teams. Gone are the days of slapping security on as an afterthought. The only way to ensure software is safe is to integrate security testing into your DevOps process. The problem?
GeekWire
APRIL 4, 2024
Allen Institute for AI is a finalist for its Open Language Model, or OLMo. The Seattle-based institute released the open-source large language model in February along with the underlying data and code, meant to significantly improve understanding of how generative AI actually works.

GeekWire
SEPTEMBER 19, 2023
(LinkedIn Photos) A pair of Amazon alum is raising cash for a new startup that helps enterprises build and deploy secure artificial intelligence applications, preventing company data from slipping through the cracks. Founded earlier this year, Griptape is developing an open-source Python framework and cloud platform.

GeekWire
JULY 27, 2023
Augmend Photo) A new artificial intelligence startup wants to help software development teams capture, store, and query their company data and knowledge. Founded earlier this year, the 5-person startup is led by CEO Diamond Bishop , a former engineering leader at Meta that led teams on the open-source machine learning project PyTorch.
ForAllSecure
JANUARY 12, 2022
With more applications being built every day, the need for robust Application Security Testing (AST) has never been greater. In this blog post, we'll cover the roles DAST and SAST play in Application Security Testing and discuss how fuzzing fits into it all. Similarly, Software Composition Analysis (SCA) looks at open source code.

ForAllSecure
MARCH 21, 2022
Strong demand for application security that supports DevSecOps initiatives drives investment from Koch Disruptive Technologies and New Enterprise Associates. “We believe manual testing is too slow, expensive, and error-prone to scale with the modern speed of development. . The time to fully automate application security is now.”

ForAllSecure
FEBRUARY 15, 2023
In the rush to comply with various standards, such as addressing the OWASP Top 10 API , companies are looking at API security with renewed interest. Some organizations have begun using Web Application Firewalls (WAFs) to protect their APIs, but this isn’t a true solution to API security. Are WAFs Enough for API Security?

ForAllSecure
JANUARY 10, 2023
By launching a free version of Mayhem, we are one step closer to our mission of making security testing available to everyone. That’s countless developer hours saved, vulnerabilities and bugs identified, and safer applications shipped. Mayhem Heroes secured over 1,400 open source projects.

CTOvision
NOVEMBER 21, 2014
This webinar will examine how to economically enhance security and functionality by leveraging Cloudera and Intel. Enhance security. Previously, Webster held positions in sales and services at companies like Microsoft and FAST Search and Transfer and in software development at firms like Time Inc.

ForAllSecure
AUGUST 17, 2021
It's important to understand that there is no 100% in security. Frankly, it is impossible to secure everything all the time. Maybe you put a security system in place, but are there blind spots. SOFTWARE IS ASSEMBLED. This allows developers to release faster without having to code features from scratch.

CIO Business Intelligence
SEPTEMBER 14, 2022
Demand has increased so much that IT job postings in manufacturing doubled between May 2021 and 2022, according to Dice.com, with increased demand for skills such as agile development, Python, software development, automation, C++, SQL, and Java, among others. Software developer. DevSecOps engineer.

ForAllSecure
OCTOBER 9, 2019
But how exactly will artificial intelligence help bridge the information security skills gap? And even with the help of machine learning algorithms, what kinds of security work is still best left to humans? We also talk about what’s driving the adoption of AI and machine learning technologies in the information security field.

ForAllSecure
OCTOBER 19, 2022
Over the next several weeks, Capuano and the combined groups of ASU students contributed over 300 GitHub Open Source Software integrations for our Mayhem Heroes program. How did you first get into software development? From then onwards, I knew I’d want to do software development professionally.

CIO Business Intelligence
APRIL 17, 2024
Helping software developers write and test code Similarly in tech, companies are currently open about some of their use cases, but protective of others. So far, Castillo has been publishing her work with open-source licenses. And unit tests are too tedious for humans to build reliably.

Kitaboo
MAY 23, 2023
In this comprehensive guide, we will delve into the fascinating world of Digital Rights Management (DRM) and explore how it is implemented in software applications. Table of Contents: What is Software-based DRM? How Does Software-based DRM Work? Can software-based DRM be used in open-source software?
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content