Linux malware is on the rise—6 types of attacks to look for
Network World
MAY 30, 2022
Malware targeting Linux environments has increased massively in the past year, with threat actors using a variety of techniques to carry out operations.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Network World
MAY 30, 2022
Malware targeting Linux environments has increased massively in the past year, with threat actors using a variety of techniques to carry out operations.

Tech Republic
SEPTEMBER 9, 2022
Jack Wallen ponders the rising tide of Linux malware and offers advice on how to help mitigate the issue. The post The rise of Linux malware: 9 tips for securing the OSS appeared first on TechRepublic.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

TechSpot
JUNE 29, 2022
Last year, cyberattacks against corporate networks reached record-setting levels in terms of frequency and size, mostly because of the Log4J vulnerability that was left unpatched by many organizations for several months.

SecureWorld News
MAY 4, 2023
Its malware is specifically geared toward ESXi hosts, as it contains two related commands. The post adds, "This is the first time the group has created a Linux binary. Its locker ransomware infects Linux, NAS, and ESXi hosts and appears to be inspired by Babuk ransomware's leaked source code."

SecureWorld News
JULY 27, 2023
A new study from Uptycs has uncovered an increase in the distribution of information stealing malware. According to the new Uptycs whitepaper, Detecting the Silent Threat: 'Stealers are Organization Killers' (gated link), a variety of new info stealers have emerged this year, preying on Windows, Linux, and macOS systems.

Scott Lowe
MARCH 15, 2024
Networking Lee Briggs (formerly of Pulumi, now with Tailscale) shows how to use the Tailscale Operator to create “free” Kubernetes load balancers (“free” as in no additional charge above and beyond what it would normally cost to operate a Kubernetes cluster). Ivan Pepelnjak dives deep on DHCP relaying on a Linux host.

Network World
MAY 26, 2022
Cheerscript plants double-extortion malware on ESXi servers.

Linux Academy
APRIL 30, 2019
By adding free cloud training to our Community Membership, students have the opportunity to develop their Linux and Cloud skills further. Each month, we will kick off our community content with a live study group allowing members of the Linux Academy community to come together and share their insights in order to learn from one another.

Network World
JUNE 30, 2016
LizardStresser, the DDoS malware for Linux systems written by the infamous Lizard Squad attacker group, was used over the past year to create over 100 botnets, some built almost exclusively from compromised Internet-of-Things devices. To read this article in full or to leave a comment, please click here

Network World
SEPTEMBER 10, 2021
Palo Alto Networks has rolled out a Wi-Fi based package that the company says provides remote workers with enterprise-class security features. The package also offers malware and ransomware prevention, phishing protection, infected device detection, and suspicious-activity monitoring and control, the company said.

Network World
JANUARY 17, 2017
Preventing the spread of malware and/or dealing with the consequences of infection are a fact of life when using computers. If you’ve migrated to Linux or Mac seeking refuge from the never-ending stream of threats that seems to target Windows, you can breath a lungful of fresh air—just don’t let your guard down.

Linux Academy
APRIL 29, 2019
By adding free cloud training to our Community Membership, students have the opportunity to develop their Linux and Cloud skills further. Each month, we will kick off our community content with a live study group allowing members of the Linux Academy community to come together and share their insights in order to learn from one another.

Network World
SEPTEMBER 6, 2016
Security researchers have identified a new family of Linux rootkits that, despite running from user mode, can be hard to detect and remove. It targets Linux-based systems on the x86, x86-64 and ARM architectures, including many embedded devices such as routers. To read this article in full or to leave a comment, please click here
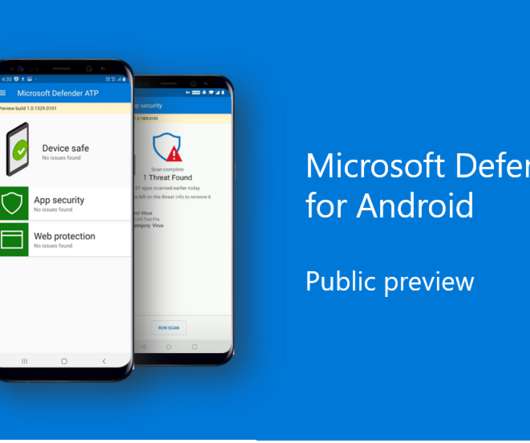
The Verge
JUNE 23, 2020
The public preview for Android will include protection against phishing and go a step further than Google’s built-in malware protection to offer signature-based malware detection. We’re now getting a good idea of exactly why Microsoft thinks Android needs antivirus protection.

SecureWorld News
OCTOBER 21, 2021
In the investigation, it was uncovered that LightBasin put energy towards Linux and Solaris systems, avoiding the more robust monitoring systems by Windows. ". LightBasin also uses a long list of malware and other techniques to carry out their devious deeds. Huawei ), potentially helping to facilitate the initial compromise.".

Scott Lowe
AUGUST 27, 2021
I have a fairly diverse set of links for readers this time around, covering topics from microchips to improving your writing, with stops along the way in topics like Kubernetes, virtualization, Linux, and the popular JSON-parsing tool jq. Networking. Michael Kashin shares the journey of containerizing NVIDIA Cumulus Linux.

Scott Lowe
AUGUST 27, 2021
I have a fairly diverse set of links for readers this time around, covering topics from microchips to improving your writing, with stops along the way in topics like Kubernetes, virtualization, Linux, and the popular JSON-parsing tool jq along the way. Networking. I hope you find something useful! Servers/Hardware. Plastic microchips

Network World
FEBRUARY 9, 2017
Attackers have started to use Windows and Android malware to hack into embedded devices, dispelling the widely held belief that if such devices are not directly exposed to the Internet they're less vulnerable.

Scott Lowe
AUGUST 12, 2022
DNS, BGP, hardware-based security, Kubernetes, Linux—they’re all in here. Networking. A “highly evasive” Linux malware named OrBit has emerged; see here for more details. Hopefully I’ve managed to find something useful for someone.

Scott Lowe
JANUARY 27, 2023
I’ve got another collection of links to articles on networking, security, cloud, programming, and career development—hopefully you find something useful! Networking William Morgan’s 2022 service mesh recap captures some of the significant events in service mesh in 2022, although through a Linkerd-colored lens.

Network World
AUGUST 31, 2016
SentinelOne Endpoint Protection Platform (EPP) is an antimalware solution that protects against targeted attacks, malware, and zero-day threats through behavioral analysis and process whitelisting and blacklisting. To read this article in full or to leave a comment, please click here (Insider Story)

CIO Business Intelligence
AUGUST 25, 2022
What’s different now is that the concept of what will comprise a network node is changing rapidly, along with the number of interconnected devices. After all, you wouldn’t want your haptic glove to misbehave in the metaverse or your autonomous vehicle sensors to be hijacked by malware. Some form(s) of “the metaverse” and Web 3.0

Network World
FEBRUARY 22, 2017
Just what the world needs, another Linux distro. But does the fact it came from a top anti-malware vendor give it a competitive edge in the quest for security? Eugene Kaspersky, CEO of the antivirus company that bears his name, took to his blog to announce KasperskyOS , a project that has been in the works for 14 years.

Network World
SEPTEMBER 14, 2016
Adobe Systems has fixed more than 30 vulnerabilities in its Flash Player and Digital Editions products, most of which could be exploited to remotely install malware on computers. The bulk of the flaws, 26, were patched in Flash Player on all supported platforms: Windows, Mac and Linux.

Network World
MARCH 29, 2017
And while distributed denial of service, or DDoS, attacks are still a leading form of cyber warfare, ransomware and malware attacks, targeting users of smartphones and internet of things (IoT) devices, as well as PCs and systems running on Macs and Linux, are also a big threat to small businesses.

Scott Lowe
JANUARY 21, 2022
Networking. Cross-platform malware. Dennis Felsing shares some thoughts on switching to macOS after 15 years on Linux. BIOS updates without a reboot , and under Linux first? I have a few more links than normal this time around, although I didn’t find articles in a couple categories. And now for the content!

Network World
JANUARY 10, 2017
Adobe Systems released security updates for its Flash Player, Adobe Reader and Acrobat products fixing critical vulnerabilities that could allow attackers to install malware on computers. Users are advised to upgrade to Flash Player version 24.0.0.194 on Windows, Mac and Linux.

Scott Lowe
MAY 27, 2022
Networking. network virtualization). Is the relationship between network virtualization and service mesh closer than some folks might wish to admit? now has a follow-up exploit that exposes Aruba and Avaya network switches to remote code execution. I certainly hope not! Servers/Hardware.

Linux Academy
MAY 5, 2019
When command and control (CNC) malware is installed it needs to phone home. This year number five is is Secure configurations for hardware and software on devices , and number 11 is Secure configuration for network devices. The post May Intro | Roadmap to Securing Your Infrastructure appeared first on Linux Academy.

Linux Academy
MAY 5, 2019
When command and control (CNC) malware is installed it needs to phone home. This year number five is is Secure configurations for hardware and software on devices , and number 11 is Secure configuration for network devices. The post May Intro | Roadmap to Securing Your Infrastructure appeared first on Linux Academy.

Linux Academy
MAY 6, 2019
When command and control (CNC) malware is installed it needs to phone home. This year number five is is Secure configurations for hardware and software on devices , and number 11 is Secure configuration for network devices. The post May Intro | Roadmap to Securing Your Infrastructure appeared first on Linux Academy Blog.

Galido
MARCH 19, 2019
Malwarebytes is a leader of malware prevention and protection. Zone Alarm Cybersecurity blog offers information on malware and protecting yourself online. They offer malware alerts, practical online security tips, and more. Network Computing. They offer useful relevant topics on security for various platforms.

Galido
OCTOBER 4, 2018
In this way, they perform what is commonly called cyberbullying, the purpose is to generate different types of content on behalf of the victim, with the intention that the rest of users of that service – email, social network, blog.- Blocks ads, trackers, and malware. form a negative idea/image of the victim.

Galido
MAY 1, 2019
Malwarebytes is a leader of malware prevention and protection. Zone Alarm Cybersecurity blog offers information on malware and protecting yourself online. They offer malware alerts, practical online security tips, and more. Network Computing. They offer useful relevant topics on security for various platforms.

Galido
MARCH 22, 2019
Malwarebytes is a leader of malware prevention and protection. Zone Alarm Cybersecurity blog offers information on malware and protecting yourself online. They offer malware alerts, practical online security tips, and more. Network Computing. They offer useful relevant topics on security for various platforms.

Galido
MARCH 19, 2019
Malwarebytes is a leader of malware prevention and protection. Zone Alarm Cybersecurity blog offers information on malware and protecting yourself online. They offer malware alerts, practical online security tips, and more. Network Computing. They offer useful relevant topics on security for various platforms.

Galido
SEPTEMBER 25, 2019
Malwarebytes is a leader of malware prevention and protection. Zone Alarm Cybersecurity blog offers information on malware and protecting yourself online. They offer malware alerts, practical online security tips, and more. Network Computing. They offer useful relevant topics on security for various platforms.

CTOvision
FEBRUARY 4, 2015
Attendees will have the opportunity to attend expert briefings, learn from and network with experienced practitioners, and ask questions to advance their agency data analytics initiatives and save their organization’s time, funding, and staff resources. Registration & Networking Breakfast. Networking Break. Register here.

CTOvision
JANUARY 18, 2015
Attendees will have the opportunity to attend expert briefings, learn from and network with experienced practitioners, and ask questions to advance their agency data analytics initiatives and save their organization’s time, funding, and staff resources. Registration & Networking Breakfast. Networking Break. Register here.

ForAllSecure
FEBRUARY 23, 2021
In this episode, though, I’m going to focus on the much more common digital pentesters side, you know, the people who are hired to break into the digital organization, the networks, the software -- and this they can do pretty much anywhere, often without much travel. This episode dives into vulnerabilities discovered in web servers.

ForAllSecure
FEBRUARY 23, 2021
In this episode, though, I’m going to focus on the much more common digital pentesters side, you know, the people who are hired to break into the digital organization, the networks, the software -- and this they can do pretty much anywhere, often without much travel. Which brings up a very basic question: What exactly is pentesting?

Social, Agile and Transformation
JULY 14, 2009
I cover topics for Technologists from CIOs to Developers - agile development, agile portfolio management, leadership, business intelligence, big data, startups, social networking, SaaS, content management, media, enterprise 2.0 Business minded, Agile CIO with strong Big Data, Business Intelligence, Search, and Social Networking background.

Linux Academy
MAY 20, 2019
This is filtering provided at the network edge by a firewall with rules (ACLs) restricting what internal users are allowed to access. There are several reasons for wanting to restrict outbound communications, such as defeating malware, making data exfiltration harder, and the detection of infected hosts. Defeat Malware.

ForAllSecure
NOVEMBER 2, 2021
Traditional anti-malware research relies on customer systems but what if a particular malware wasn’t on the same platform as your solution software? éveillé from ESET joins The Hacker Mind podcast to talk about the challenges of building his own internet scanner to scan for elusive malware. Marc-Etienne M.Léveillé
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content