The crucial role of data security management in the digital age
Dataconomy
JANUARY 10, 2024
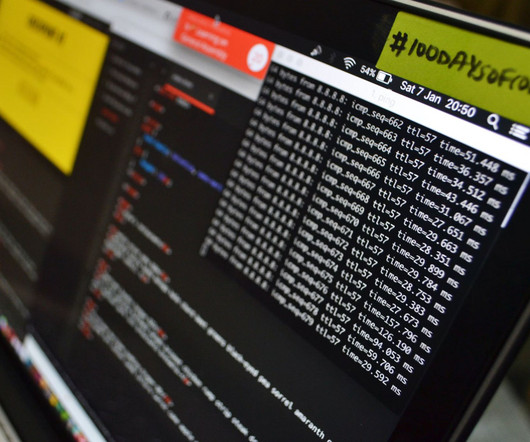
However, given the increasing reliance on technology and the growing number of cyber threats, ensuring data security has become crucial. In this post, we will explore the role of managing data security in the landscape. The importance of data security Data security is not just an option but a necessity for businesses.






















Let's personalize your content