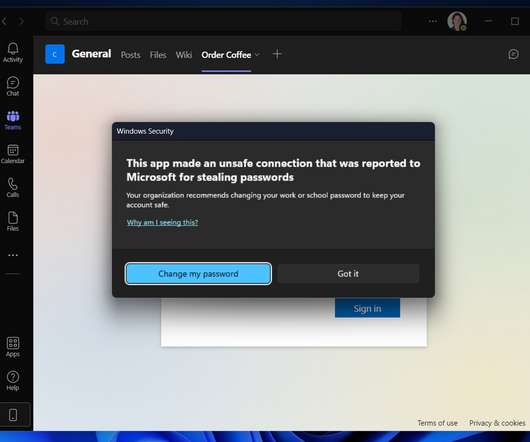
Microsoft announces major new Windows 11 security features for 2022
Venture Beast
APRIL 5, 2022
Microsoft says new Windows 11 security features for 2022 will include new phishing and malware prevention, along with default VBS features. Read More.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Dataconomy
FEBRUARY 12, 2024
Malware continues to plague organizations and individuals alike and one of the more insidious strains in recent times is the Raspberry Robin malware. Cybercriminals tirelessly devise new technologies and strategies to infiltrate systems, steal data, and disrupt lives.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

SecureWorld News
AUGUST 8, 2022
Cybersecurity and Infrastructure Security Agency (CISA) and the Australian Cyber Security Centre (ACSC) released a joint Cybersecurity Advisory (CSA) providing details on the top malware strains of 2021. The top malware strains in 2021 included remote access Trojans (RATs), banking Trojans, information stealers, and ransomware.

The Verge
SEPTEMBER 13, 2021
Mozilla has quietly made it easier to switch to Firefox on Windows recently. While Microsoft offers a method to switch default browsers on Windows 10, it’s more cumbersome than the simple one-click process to switch to Edge. Microsoft tells us this is not supported in Windows. Illustration by Alex Castro / The Verge.

CTOvision
MARCH 17, 2015
Last year, Enterprise IT was dramatically shaped by the influx of security breaches, data leaks and a new wave of hackers. But optimism came in the form of Microsoft as word began to spread that the company had solved the problems they experienced with Windows 8/8.1 Security Spending. Windows 10.

SecureWorld News
APRIL 21, 2023
To our knowledge, this is the first public mention of this major North Korea-aligned threat actor using Linux malware as part of this operation." If the payload is being sent to an unknown number of users, the operating system with the highest chance of success is Windows, by a large margin.

Network World
MAY 17, 2019
Microsoft took the rare step of issuing security fixes for both the server and desktop versions of Windows that are long out of support, so you know this is serious. The vulnerability ( CVE-2019-0708 ) is in the Remote Desktop Services component built into all versions of Windows.

CTOvision
FEBRUARY 5, 2014
Securing these devices is nearly impossible because they are not corporate controlled. XP Will Cause Significant Security Issues. The end of support for Windows XP, slated for April 8, 2014, is a dangerous security issue. CTO Cyber Security DoD and IC Mobile' Companies should plan accordingly. About the Author: .
Dataconomy
DECEMBER 5, 2023
Cybersecurity threats are evolving, and the latest menace targeting Mac users involves sophisticated proxy trojan malware. This malicious software lurks within seemingly harmless downloads of popular macOS applications, posing a significant risk to the security of your device. Stay wary and protected.

The Verge
JANUARY 21, 2022
Ransomware — malware that prevents you from accessing your files unless you pay the hacker that infected your computer — has been an issue plaguing computer users and businesses for years. Starting with Windows 10 , Microsoft has added features to its built-in Windows Security software that can help keep your computer safe from ransomware.

The Verge
JUNE 25, 2021
Windows 11 is arriving later this year as a free upgrade for Windows 10 users , but many are discovering that their hardware isn’t compatible. Windows 11 will only officially support 8th Gen and newer Intel Core processors, alongside Apollo Lake and newer Pentium and Celeron processors. Windows 11 support for AMD.

Forrester IT
MAY 15, 2017
For years, many of us in the cybersecurity industry have been jumping up and down on desks and trying to get the world (writ large) to pay attention to managing and patching outdated systems and operating systems that have been running legacy software, to no avail. cyber security. Read more Categories: #big data.

Tech Republic Security
JUNE 14, 2017
To limit the number of machines at risk from self-replicating malware like WannaCry, Microsoft yesterday patched vulnerabilities on Windows XP and other unsupported operating systems.

Network World
OCTOBER 28, 2016
Security researchers have discovered a new way that allows malware to inject malicious code into other processes without being detected by antivirus programs and other endpoint security systems. These special tables are provided by the operating system and can be used to share data between applications.

Computerworld Vertical IT
JANUARY 4, 2022
Microsoft Defender is the built-in anti-malware package that’s included with modern Windows operating systems. It’s alternatively known as Windows Security (it shows up under Settings as Windows Security) or Windows Defender (sometimes with Antivirus at the end of the name, as in this Microsoft Docs page ).

Scott Lowe
MARCH 15, 2024
This Tech Short Take is a bit heavy on security-related links, but there’s still some additional content in a number of other areas, so you should be able to find something useful—or at least interesting—in here. Security In early February a vulnerability was uncovered in a key component of the Linux boot process.

SecureWorld News
JULY 11, 2023
Apple has issued a new round of Rapid Security Response (RSR) updates to address a Zero-Day bug exploited in attacks and impacting fully-patched iPhones, Macs, and iPads. By default, your device automatically applies Rapid Security Responses. Mac: Choose Apple menu > System Settings.

Galido
JANUARY 12, 2017
Each computer system may have a malware or viruses, including Linux. It is recommended that users install these antivirus softwares on the Linux operating system that can be downloaded via Internet. In order to better understand antivirus programs, it may be beneficial to firstly understand the malware itself.

SecureWorld News
DECEMBER 6, 2022
Security researchers from Kaspersky have discovered a previously unidentified data wiper, which they have named CryWiper, that was used to attack Russian government agencies, including mayors' offices and courts. The malware was developed in C++ and compiled using the MinGW-w64 toolkit and the GCC compiler. dll", "lnk", ".sys",

The Verge
JUNE 29, 2021
Microsoft’s big security push is complicated Microsoft has had six years to prepare for the launch of Windows 11, but the company is still struggling to explain its new hardware requirements. It’s an unusual surprise if you purchased a new PC for Windows 10, or perhaps you have a perfectly capable machine that’s even older.

Galido
FEBRUARY 10, 2017
Malware is an abbreviated term that stands for “malicious software.” Spyware is an abbreviated term that stands for “spy software” Malicious, spy software is designed for the purpose of gaining access to your computer and often damaging a computer and spreading the malware without the owner knowing. What is Malware?

CIO Business Intelligence
JANUARY 20, 2023
By Anand Oswal, Senior Vice President and GM at cyber security leader Palo Alto Networks Connected medical devices, also known as the Internet of Medical Things or IoMT, are revolutionizing healthcare, not only from an operational standpoint but related to patient care. Many connected devices ship with inherent vulnerabilities.

Galido
FEBRUARY 19, 2017
Malware means a malicious or intrusive software application that is coded for executing on the targeted device without notifying its user or the owner. Affecting a mobile phone, a computer, a laptop, or a network server, malware interrupts computing operations, hijacks networks, or access systems. Update your browser.

Galido
AUGUST 3, 2016
Malware is an abbreviated term that stands for “malicious software.” What is Malware? There are various types of malware. Malware creation has become popular in recent times due to the the lure of money that can be made through organized Internet crime. Tips for Spotting Malware. How to Remove Malware.

SecureWorld News
JUNE 1, 2023
This discovery raises concerns about system integrity, the installation of undeletable malware, and the potential compromise of private user data. Microsoft promptly reported the issue to Apple, resulting in the release of security updates to address the vulnerability. Occasionally, even those built-in protections are breached.

SecureWorld News
DECEMBER 18, 2023
This immediate action represents a shift in the modus operandi of attackers, highlighting their growing efficiency and the ever-decreasing window for response by defenders. This timeline offers a crucial window for organizations to prioritize and address the most critical vulnerabilities. 15 exploited by malware and botnets.

CIO Business Intelligence
NOVEMBER 23, 2022
A recent spate of high-profile security breaches at some of the largest enterprises in Australia has reminded everyone of the importance of security. The biggest challenge when it comes to cyber crime is that there are so many different security risks to manage. vPro also boosts security for virtualised environments.
Gizmodo
APRIL 9, 2021
The app is actually a trojan designed to inject malware into your computer. Cybercriminals have been pushing Facebook users to download a Clubhouse app “for PC,” something that doesn’t exist. The popular new invite-only chat app is only available on iPhone but worldwide interest in the platform has risen and users are… Read more.

SecureWorld News
APRIL 28, 2021
In January 2021, the FBI and other international law enforcement agencies worked together to take down one of the world's most notorious malware strains, Emotet. I personally use Microsoft Defender which is free, built into Windows 10, and updates automatically via Windows Update. Keep operating systems and software patched.".

SecureWorld News
JUNE 13, 2023
The report also includes actionable insights to help organizations strengthen their security posture and proactively mitigate potential risk. The new Beep malware is top of mind for organizations and individuals. After a brief hiatus, Emotet threat actors resumed their operations in early March 2023.
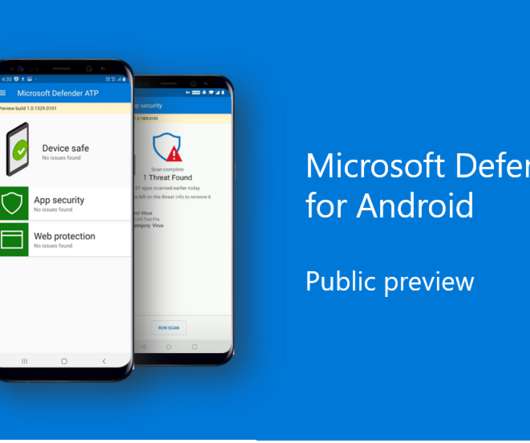
The Verge
JUNE 23, 2020
The software giant revealed that Windows Defender was making its way to both iOS and Android earlier this year , but didn’t fully detail what to expect. The public preview for Android will include protection against phishing and go a step further than Google’s built-in malware protection to offer signature-based malware detection.

The Accidental Successful CIO
FEBRUARY 3, 2016
Windows software can be a gateway for bad people to gain access to your company Image Credit: Alexander Popov. How much Microsoft windows software is being used at your company? What is starting to be realized by the person with the CIO job and security experts everywhere is that there is a reason for these repeated attacks.

CTOvision
APRIL 7, 2014
In the first quarter of 2014, the company’s advanced research division—Invincea Labs—secured $8.1M in new contracts for advanced cybersecurity projects for defense and federal government agencies in the areas of cloud-based advanced malware analysis, spear-phishing attacks against Android, and big data analytics for compromise detection.

SecureWorld News
JULY 1, 2020
The stance from Eclypsium is clear: when a driver is screwed, so is security. In a recent study, "Screwed Drivers Open ATMs to Attack," Eclypsium dove into the discussion about the risks that malicious or insecure drivers pose to Windows-based systems. How drivers contribute to ATM attacks. Interested in this research?

Galido
DECEMBER 28, 2018
Information Technology Blog - - Data Security and its Importance on the Internet - Information Technology Blog. Users are partly responsible for their own safety, and often the lack of security updates and knowledge of security protocol has made them vulnerable to malicious attacks. Why Should You Care?

SecureWorld News
APRIL 21, 2022
Cybersecurity and Infrastructure Security Agency (CISA) has issued a joint cybersecurity advisory with the Federal Bureau of Investigation (FBI) and the U.S. The threat actors use social engineering to encourage individuals to download trojanized cryptocurrency applications on Windows or macOS operating systems.

SecureWorld News
OCTOBER 21, 2021
In the investigation, it was uncovered that LightBasin put energy towards Linux and Solaris systems, avoiding the more robust monitoring systems by Windows. ". LightBasin also uses a long list of malware and other techniques to carry out their devious deeds.

Galido
SEPTEMBER 12, 2016
A virus is a self- replicating, malicious application that can easily penetrate an operating system with the sole purpose of spreading harmful programming codes. They can also utilize the errors in a network configuration as well as the loopholes of the security application and operating systems.

SecureWorld News
MARCH 2, 2021
However, unlike Hermes, Ryuk was never made available on the forum, and CryptoTech has since ceased all of its activities, so there is some doubt regarding the origins of the malware. Once launched, it will thus spread itself on every reachable machine on which Windows RPC accesses are possible.

Galido
OCTOBER 31, 2018
To be noted is the fact that a vulnerability scanner is as important as a malware scanner today. While a malware scanner helps check for malware and clear them, the vulnerability scanning tool could help prevent malware threats and attacks. After all, it’s all for the security of your business!

Scott Lowe
AUGUST 27, 2021
Teri Radichel uses some basketball analogies to explain why defensive (proactive) security strategies are more desirable than reactive security strategies. Sentinel Labs outlines a major malware push that is bypassing Apple’s malware protections. Operating Systems/Applications. A severity score of 9.9

Galido
MARCH 19, 2019
Information technology is the use of any tech devices, infrastructure, software and processes to create and process, store, secure and exchange all forms of digital data. Our articles are typically focused on software recommendations, business, security, interesting topics and search engine optimization and marketing. Search Security.

Scott Lowe
AUGUST 27, 2021
Teri Radichel uses some basketball analogies to explain why defensive (proactive) security strategies are more desirable than reactive security strategies. Sentinel Labs outlines a major malware push that is bypassing Apple’s malware protections. Operating Systems/Applications. A severity score of 9.9

ForAllSecure
APRIL 19, 2023
It’s time to evolve beyond the UNIX operating system. So while I was editing this podcast on self-healing operating systems, I was reminded of an article that I never finished for Fobes.com. It’s a radical rethinking of how we even view our current choices of UNIX-derived operating systems.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content