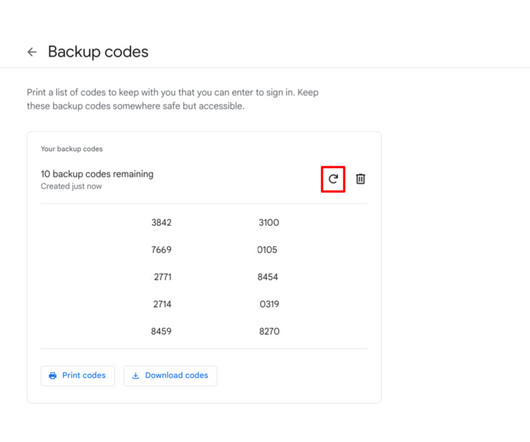
How to Retrieve and Generate Google 2FA Backup Codes
Tech Republic
AUGUST 17, 2023
Learn how to retrieve and generate Google 2FA backup codes with this easy-to-follow, step-by-step tutorial.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Tech Republic
AUGUST 17, 2023
Learn how to retrieve and generate Google 2FA backup codes with this easy-to-follow, step-by-step tutorial.

The Verge
SEPTEMBER 2, 2020
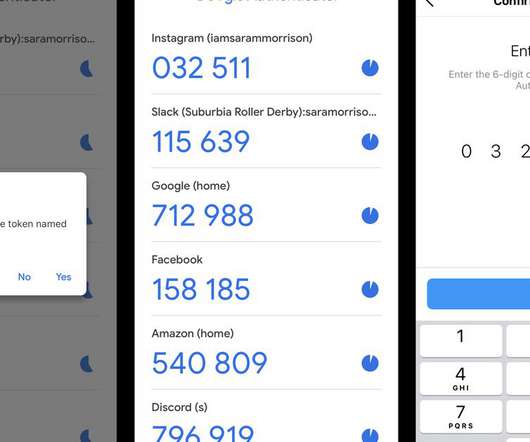
Two-factor authentication (2FA) is one of the best and easiest ways to keep your online accounts secure. They work by issuing an authentication code on your phone when somebody tries to access the account; if that person doesn’t have the code, they (or you) don’t get in. Transfer your Authenticator keys via Android.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Generative AI Deep Dive: Advancing from Proof of Concept to Production
Reimagining Cybersecurity Training: Driving Real Impact on Security Culture

Tech Republic
JUNE 17, 2022
In this step-by-step guide, learn how to enable the backup feature within the two-factor authentication application Authy. The post How to back up your Authy app appeared first on TechRepublic.
The Verge
OCTOBER 7, 2020
Tesla accounts can now be secured with two-factor authentication (2FA), giving owners an extra layer of security around their cars’ connected services, Electrek reports. A support page on Tesla’s website outlining how to set up the feature says any third-party authenticator apps can be used to provide the passcodes.

SecureWorld News
AUGUST 5, 2023
Multi-factor authentication (MFA) is a fundamental component of best practices for account security. Traditionally, this approach to authentication delivers a unique code to a user's email or phone, which is then inputted following the account password. SMS-based MFA MFA via SMS (i.e.,

Vox
NOVEMBER 12, 2023
Access to just about everything I wasn’t already logged into on my computer was dependent on access to my phone, with my mobile-device-only password manager and multifactor authentication apps and text messages. Didn’t I delete my backups to free up storage space? Backup of data in the digital reality we’re in now is paramount.

CIO Business Intelligence
MARCH 15, 2023
Multifactor authentication fatigue and biometrics shortcomings Multifactor authentication (MFA) is a popular technique for strengthening the security around logins. Some of these components have professional teams that test and maintain them, releasing security patches as needed. And how do you tell?
Vox
MAY 6, 2021
Authenticator apps like Google Authenticator might seem intimidating, but they’re easy to use and safer than texts. If you’re using texts for two-factor authentication, it’s time to change to an app. When people ask me for security tips, I give them the basics. And you always use two-factor authentication, or 2FA.

Linux Academy
MAY 31, 2019
This week, we’re discussing secure configurations, and why they matter. Our friends at the Center for Internet Security (CIS) listed “Secure Configurations” as the No. 5 most important security control on this year’s Top 20 hit list. Of course, I need to securely configure my devices.

SecureWorld News
MARCH 12, 2024
This situation demands immediate action to mitigate damage and restore security. While the WordPress Core is generally secure, thanks to frequent security updates, hackers can often easily exploit third-party plugins and themes. Let's explore the warning signs and discuss how to repair the damage.

CIO Business Intelligence
SEPTEMBER 21, 2023
With the CSO50 Conference + Awards coming to the We-Ko-Pa Casino Resort in Fort McDowell, Arizona, October 2-4, we asked Bill Tsoukatos, Information Technology Director at Fort McDowell Enterprises, which owns the resort, to tell us what it’s like to manage IT security at a casino property.

SecureWorld News
OCTOBER 8, 2023
However, many end-users do not recognize their home networks as extensions of their company's security boundaries. They often feel that using a company-provided laptop linked to the corporate security system is sufficient. As a result, they might not take enough measures to secure their other home devices.

SecureWorld News
AUGUST 22, 2022
Control social media access for more security. Hackers don't need much of an invitation to try to infiltrate a company network, so businesses must put measures in place to secure their data. Humans are emotional beings rather than robots programmed to behave with security at the top of their minds.

SecureWorld News
AUGUST 22, 2023
70 percent of web applications have severe security gaps, like lacking WAF protection or an encrypted connection like HTTPS, while 25 percent of all web applications (web apps) lacked both. However, the specific data points mentioned in the report might come as a surprise, even to seasoned security professionals.

Linux Academy
APRIL 15, 2019
Welcome back to our weekly blog post as we look at how to better secure your infrastructure. Last week, we discussed the use of password managers and multi-factor authentication (MFA). Early on in my security days, I was introduced to policies, which, at the time, I thought were a waste of time.

ForAllSecure
APRIL 26, 2023
Social Engineering According to Carnegie Mellon University’s Information Security Office , “Social engineering is the tactic of manipulating, influencing, or deceiving a victim in order to gain control over a computer system, or to steal personal and financial information.

Vox
DECEMBER 8, 2022
How to encrypt most of your iCloud data — and why you should. Which means that almost everything you upload to Apple’s cloud — from backups to photos — can only be accessed by you. Apple’s new security feature will also prevent law enforcement from accessing the data you have in iCloud. A woman takes a photo of an iPhone.

Dataconomy
NOVEMBER 21, 2023
We have over 1.5TB of documents leaked + 3 full backups of CRM for branches (eu, na and au),” boasts the ransomware group on their dark web data leak site. They rang the alarm bells for the Canadian Centre for Cyber Security and the Office of the Privacy Commissioner, keeping the big guns in the loop.

Galido
AUGUST 30, 2019
Passwords & Authentication. Additionally, you can add another layer of protection with two-factor authentication. provide advanced firewalls which can greatly enhance your business security. Backup Data. This encrypts the data before it leaves the device so it is kept secure until it reaches the recipient’s device.

SecureWorld News
FEBRUARY 19, 2024
Its relative simplicity of use, SEO friendliness, customization potential, flexibility, and built-in security setup are just some of the reasons why web developers and marketing professionals choose it to power their websites. However, even experienced coders can make mistakes when assessing and bolstering a site's security.

The Verge
JUNE 9, 2021
Two-factor authentication is a good way to add an extra layer of security to online accounts. Hardware security keys can offer an additional layer of security to password-protected online accounts and, in turn, your identity. Here’s how to set them up for your Google account, Facebook, and Twitter.

CIO Business Intelligence
FEBRUARY 1, 2024
When organizations buy a shiny new piece of software, attention is typically focused on the benefits: streamlined business processes, improved productivity, automation, better security, faster time-to-market, digital transformation. Backup: Application data doesn’t simply live in one place. Then there’s backups and disaster recovery.

Linux Academy
MAY 7, 2019
Identity and security. Implement authentication. Implement secure data solutions. They should be proficient in developing apps and services by using Azure tools and technologies, including storage, security, compute, and communications. Manage and secure web apps with backup, restore, snapshot, and cloning.

Linux Academy
MAY 7, 2019
Identity and security. Implement authentication. Implement secure data solutions. They should be proficient in developing apps and services by using Azure tools and technologies, including storage, security, compute, and communications. Manage and secure web apps with backup, restore, snapshot, and cloning.

CIO Business Intelligence
MAY 18, 2022
That requires enterprise architects to work more closely with risk management and security staff to understand dependencies among the components in the architecture to better understand the likelihood and severity of disruptions and formulate plans to cope with them. Planning for supply chain disruption.

Linux Academy
MAY 7, 2019
Identity and security. Implement authentication. Implement secure data solutions. They should be proficient in developing apps and services by using Azure tools and technologies, including storage, security, compute, and communications. Manage and secure web apps with backup, restore, snapshot, and cloning.

Sean Daniel
JANUARY 3, 2012
How to use your Home Server as an AirPrint server for only $10. I’m also not a big fan of Jail-Breaking (I guess I know too much about security to allow a hacker full access to my device). Hi Dave, My guess is you've somehow managed to add some authentication to who can print. Online Backup. (5). Online Backup.

Sean Daniel
FEBRUARY 1, 2011
How to set the Default Printer for All Users in your Small Business Server 2011 Standard or Essentials Network. Here is how to create the default policy: Click Start , Administrative Tools , and then Group Policy Management. Select Authenticated Users , and click Remove. This is a useful instruction on how to set the default.

Dataconomy
FEBRUARY 7, 2024
The platform includes secure documentation storage, user management tools, activity tracking mechanisms, and collaboration features. Image credit ) How virtual data rooms help You get a secure way to share data with potential buyers and investors , which can facilitate discussions around optimizing the capital stack.

The Verge
FEBRUARY 23, 2021
What follows are instructions on how to download your LastPass data, and where to find instructions from several popular password managers that will help you upload that data to their services. Here’s how. Paid features start at $10 / year and include file storage, authenticator, two-step login, others. Free version?

Galido
MAY 23, 2019
Information Technology Blog - - How to Protect Your WooCommerce Site from Hackers and Secure Your Customer Data? How Can I Secure My WooCommerce Store? With a shocking number of hacking incidences taking place in the world every day, security has become the top priority for any website. Secure DDoS Defense.

Chief Seattle Greek Blog
AUGUST 14, 2012
My friend Glenn Fleischman of Seattle exposed his answers to all the common security questions, thereby saving hackers the trouble of a brute force attack on his own Internet presence. Always reboot without saving your files and never make take time to make those pesky backups. Turn on six factor authentication immediately.

SecureWorld News
SEPTEMBER 15, 2023
Looking at the disastrous Colonial Pipeline hack as a glaring example of the importance of stringent safeguards—not to mention the growth in ransomware attacks on enterprises—implementing robust security measures is a must. What threats do digital media assets face?

Galido
NOVEMBER 7, 2018
Information Technology Blog - - How to Transfer Data from Android to Android in One Click - Information Technology Blog. Read on and learn how to transfer data from Android to Android without any hassle. Now, you can just connect both the Android devices to the system using authentic USB cables.

Sean Daniel
JANUARY 14, 2010
Certificates provide two purposes: Authenticating the server to the client Providing encryption between the server and the client I will cover the authenticating the server to the client in this part 1 post, and will write a part 2 post that handles the second part of encryption. Sure, I trust the state government.
Galido
NOVEMBER 24, 2019
Information Technology Blog - - 6 Internet Security Tips For 2020 - Information Technology Blog. Let’s take a look at some popular internet security tips for 2020. Secure Passwords. If you receive a threatening email, contact the merchant directly by typing in their link to confirm the authenticity of the email.

ForAllSecure
DECEMBER 2, 2021
And my background is pretty straightforward with cyber security for the past 16 years on many different levels. Vamosi: At SecTor, an annual security conference in Toronto, Paua gave not one but two talks this year. And eventually, when we compare that one with the initial point of entry security log.

Linux Academy
APRIL 1, 2019
Why do I bring up car care when this is an information security blog? How can we provide care to our infrastructure you ask? More secure passwords. The individual topics for this month are: More Secure Passwords. Security challenges. Our end goal in this is to get C-level buy-in on secure password practices.

Sean Daniel
MAY 17, 2010
In this post I talked primarily about how the server is authenticated to the client by using a “root” certificate that the client already trusts, thus establishing a trust relationship with a website you are at without actually having been there before. There are pros and cons to each approach, but both are just as secure.

Sean Daniel
JUNE 14, 2011
View the backup status that every device last reported to the server. Start or stop a backup for any computer or the server (from the contextual menu). How To Install Windows Home Server 2011 on your MediaSmart or DataVault Hardware. Online Backup. (5). Online Backup. Subscribe to this feed. Cloud Computing. (10).

ForAllSecure
NOVEMBER 18, 2021
Vamosi: How do we know who’s on the other end of a connection, who it is that is logging into a computer or an account online? So we include other telemetry that seeks to authenticate that the entity logging in is who they say they are. I’m just not convinced that a fingerprint or an image of my face is secure enough.

Dataconomy
APRIL 25, 2023
In this post, we focus on MSP cyber security, including main challenges, threats and practices. Read on to find out: Why an MSP should care about cyber security Which threats you need to counter the most How to protect your and clients’ data and infrastructures from possible failures MSP Security: Why is it important?

CIO Business Intelligence
MAY 30, 2023
In fact, Uzupis says he has seen over his years in IT how leadership has become more security aware and, with that, more enthusiastic supporters of security-related initiatives. People are coming to the conclusion that compliance isn’t security,” he says. And all that, he adds, rolls up into creating value.

SecureWorld News
APRIL 30, 2023
One of the most important responsibilities of security professionals is to avoid data breaches. Many advanced security systems cannot prevent a scenario in which a user takes a screenshot from a confidential document and then sends it via Telegram to an unauthorized recipient. What is Data-Centric Audit and Protection?
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content