Digital Rights Management: The eBook DRM Revolution
Kitaboo
MARCH 26, 2024
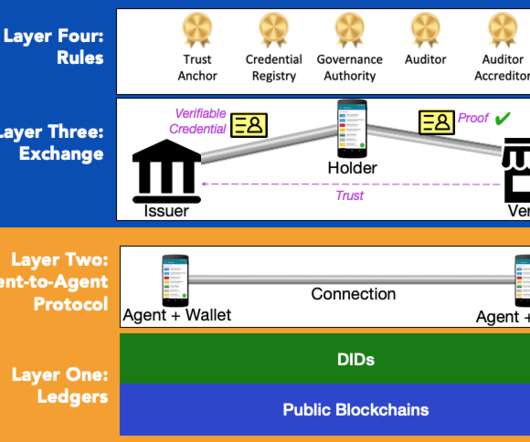
eBook DRM implements total control over resources using technologies such as encryption and authentication. It includes methods like user authentication, verification, licensing of eBooks, encryption, etc. Methods such as licensing and encryption prevent the published materials from being copied, redistributed, or pirated.
































Let's personalize your content