Red Hat Enterprise Linux 9 offers new solution to verify the integrity of OS’s
Venture Beast
MAY 10, 2022
Red Hat launches the Red Hat Enterprise Linux 9 with a unique new solution to verify the integrity of operating systems. Read More.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Venture Beast
MAY 10, 2022
Red Hat launches the Red Hat Enterprise Linux 9 with a unique new solution to verify the integrity of operating systems. Read More.

Linux Academy
MAY 16, 2019
Linux Academy is happy to announce that the new Red Hat Enterprise Linux 8 Distribution is available in the Linux Academy Cloud Playground. Cloud Playground is included in both individual Linux Academy memberships , as well as business memberships. How To Launch Red Hat Enterprise Linux 8 in Cloud Playground.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Venture Beast
APRIL 27, 2021
Red Hat is set to launch a new Linux-based operating system for road vehicles, with a focus squarely on safety and certification. Read More.

CIO Business Intelligence
OCTOBER 6, 2023
When you’re tasked with migrating 200,000 servers to a new operating system, a helping hand is very welcome indeed. With CentOS now part of the Red Hat Enterprise Linux beta stream chain, RHEL was a logical choice for Salesforce, which conducted a rigorous selection process, deciding on RHEL last December.

Linux Academy
APRIL 30, 2019
By adding free cloud training to our Community Membership, students have the opportunity to develop their Linux and Cloud skills further. Each month, we will kick off our community content with a live study group allowing members of the Linux Academy community to come together and share their insights in order to learn from one another.
Venture Beast
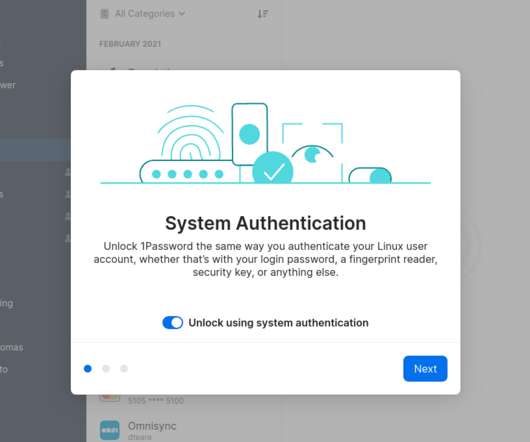
MAY 18, 2021
1Password has launched a desktop app for Linux. The company introduced the app in beta last October, but now it's available for one and all. Read More.

Linux Academy
MAY 28, 2019
By adding free cloud training to our Community Membership, students have the opportunity to develop their Linux and Cloud skills further. Each month we will kick off our community content with a live study group allowing members of the Linux Academy community to come together and share their insights in order to learn from one another.

Venture Beast
SEPTEMBER 22, 2020
At Ignite 2020 today, Microsoft announced that Edge for Linux will be available in the Dev preview channel starting in October. Read More.
The Verge
NOVEMBER 17, 2020
Microsoft is creating a new security chip that’s designed to protect future Windows PCs. Microsoft Pluton is a security processor that is built directly into future CPUs and will replace the existing Trusted Platform Module (TPM), a chip that’s currently used to secure hardware and cryptographic keys. so you just get it.”

Network World
MAY 20, 2016
Schools and enterprises choose Chromebooks for their very streamlined use case: low cost, fast boot security, simplicity and ease of administration. With first-quarter shipments exceeding Macs in the United States, Chromebooks are very popular. To read this article in full or to leave a comment, please click here

GeekWire
NOVEMBER 26, 2023
The new Amazon WorkSpaces Thin Client, a “reinvented” Amazon Fire TV Cube, will sell for $195, designed for enterprise customers to offer to their employees. Amazon Web Services executives say they decided to take the approach after hearing from enterprise customers that they wanted a low-priced device.

Linux Academy
APRIL 29, 2019
By adding free cloud training to our Community Membership, students have the opportunity to develop their Linux and Cloud skills further. Each month, we will kick off our community content with a live study group allowing members of the Linux Academy community to come together and share their insights in order to learn from one another.

GeekWire
DECEMBER 15, 2021
“We have observed these groups attempting exploitation on both Linux and Windows systems, which may lead to an increase in human-operated ransomware impact on both of these operating system platforms.” Apache has released two security updates to address the flaws discovered in Log4j.

CIO Business Intelligence
AUGUST 25, 2022
This raises new questions about managing and operating these devices in a consistent, reliable, and secure manner. Operating Systems for the edge. As more devices come online, their management and security will be front-of-mind for administrators. Secure code for the edge.

CIO Business Intelligence
JANUARY 4, 2024
In the fast-evolving world of finance, data security is of paramount importance. The Payment Card Industry Data Security Standard (PCI DSS) is a crucial framework to which financial institutions must adhere. The Payment Card Industry Data Security Standard (PCI DSS) is a crucial framework to which financial institutions must adhere.

The Verge
JULY 31, 2020
Google is positioning this new Windows app support in Chrome OS as a big incentive for enterprises considering switching employees over to Chromebooks. At first, Parallels Desktop will boot a full copy of Windows, allowing Microsoft’s operating system to sit side by side with Chrome OS and Android apps.

Kitaboo
NOVEMBER 17, 2023
If you’re an enterprise or independent author looking for ways to enhance your eBook sales, now is the best time to capitalize on the pros of ePUB file formatting. All in all, KITABOO is a one-stop solution for authors and enterprises looking to build a comprehensive eBook library from scratch. Trust Convertio to do the job.

ForAllSecure
JUNE 16, 2020
With the increasing numbers of remote workers, it’s even more critical to make sure the software agencies develop and use is secure. By incorporating a quality assurance technique called fuzzing into their software vulnerability testing and assurance processes to uncover coding errors and security loopholes. How to get started?

ForAllSecure
JUNE 16, 2020
With the increasing numbers of remote workers, it’s even more critical to make sure the software agencies develop and use is secure. By incorporating a quality assurance technique called fuzzing into their software vulnerability testing and assurance processes to uncover coding errors and security loopholes. How to get started?

ForAllSecure
JUNE 16, 2020
With the increasing numbers of remote workers, it’s even more critical to make sure the software agencies develop and use is secure. By incorporating a quality assurance technique called fuzzing into their software vulnerability testing and assurance processes to uncover coding errors and security loopholes. How to get started?

CIO Business Intelligence
JUNE 8, 2022
VMware Cloud Universal empowers RCIT with a flexible multi-cloud environment designed for security, scale, and innovation. To comply with data sovereignty regulations, the group’s IT division, Schibsted Enterprise Technology, operated 1,500 servers running on-premises in local data centers before the outbreak of the COVID-19 pandemic.

Scott Lowe
APRIL 6, 2017
Humair Ahmed of VMware shares some details on a new control plane resiliency feature recently added to VMware NSX: Controller Disconnected Operation (CDO) mode. Here’s a handy list of deprecated Linux network commands and their replacements. Konstantin Ryabitsev has a series going on securing a SysAdmin Linux workstation.

SecureWorld News
JUNE 12, 2023
Some courses are tailored to a specific discipline, while others may be broader, covering areas such as network security , ethical hacking, and more. For example, on mobile devices, an attack is launched every 39 seconds , so it is vital to know how to secure a range of endpoints. based on reviews on Coursera) Cost: Free [link] 2.

Linux Academy
MARCH 28, 2019
To ensure ongoing security site reliability engineers must work hand-in-hand with the CISO’s (Chief Information Security Officer) office to implement Kubernetes security. Vulnerabilities at the operating system level may be exploited by rogue container workloads if not hardened. Server Hardening. Implement RBAC.

Scott Lowe
JULY 17, 2020
This is a great read overall, but one sentence in particular really caught my eye: “30 years ago I was able to write a complete multitasking operating system in Z80 assembly code. Jon Langemak is blogging again, and he jumps back into the “blogging saddle” with a post on working with tc on Linux systems.

Scott Lowe
AUGUST 11, 2023
Security Backdoors in SSH public keys ? Operating Systems/Applications There’s been a ton of coverage about the Red Hat changes around RHEL sources and such, so I won’t bother going into any detail on that. Be wary, friends. Alessandro Brucato updates on SCARLETEEL 2.0 enhancements and changes.

Linux Academy
SEPTEMBER 5, 2019
Puppet Enterprise 2018.1 We will be learning from the ground up, starting with the installation process for Puppet Enterprise (PE). Microsoft SQL Server on Linux Quick Start : This course teaches learners how to install and configure an SQL Server on Linux, whether using a traditional machine, containers, or an Azure SQL VM.

Dataconomy
APRIL 13, 2023
The VNC protocol also supports encryption of the VNC traffic, which is done using a secure variant of the VNC protocol known as VNC over Secure Shell (VNC over SSH). This protocol uses port 22, the standard port for SSH, for establishing a secure connection between the VNC server and client.

Galido
MARCH 19, 2019
Information technology is the use of any tech devices, infrastructure, software and processes to create and process, store, secure and exchange all forms of digital data. Our articles are typically focused on software recommendations, business, security, interesting topics and search engine optimization and marketing. Search Security.

ForAllSecure
APRIL 30, 2020
The Decipher Security podcast by Duo Security analyzes the news, explores the impact of the latest risks, and provides informative and educational material for readers intent on understanding how security affects our world. He posits that security, particularly secure software, is a value add to businesses.

ForAllSecure
APRIL 30, 2020
The Decipher Security podcast by Duo Security analyzes the news, explores the impact of the latest risks, and provides informative and educational material for readers intent on understanding how security affects our world. He posits that security, particularly secure software, is a value add to businesses.

ForAllSecure
APRIL 30, 2020
The Decipher Security podcast by Duo Security analyzes the news, explores the impact of the latest risks, and provides informative and educational material for readers intent on understanding how security affects our world. He posits that security, particularly secure software, is a value add to businesses.

Scott Lowe
MAY 29, 2020
Bruce Schneier weighs in on the security and privacy implications of Zoom. Some security vulnerabilities with Thunderbolt were recently discovered and disclosed. Looking for some security tools? Jason Price shares a fully fleshed-out example of Kubernetes Pod Security Policies. Operating Systems/Applications.

Cloud Musings
DECEMBER 19, 2017
The enterprise data storage marketplace is poised to become a battlefield. Before 2007 and the birth of the cloud computing market we are witnessing today, the on-premise model hosted in large local data centers dominated enterprise storage. Data security, legal and regulatory concerns, for the most part, were very localized.

Galido
MAY 1, 2019
These areas of tech include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Security Tech Blogs. Techworld Security Blog. They offer useful relevant topics on security and tech security news.

Galido
MARCH 22, 2019
These areas of tech include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Security Tech Blogs. Techworld Security Blog. They offer useful relevant topics on security and tech security news.

Scott Lowe
FEBRUARY 11, 2021
I recently mentioned on Twitter that I was considering building out a new Linux PC to replace my aging Mac Pro (it’s a 2012 model, so going on 9 years old). Kaizhe Huang examines Falco versus AuditD from a host intrusion detection system (HIDS) perspective. Eclypsium discusses ways of protecting system firmware storage.

Galido
SEPTEMBER 25, 2019
These areas of tech include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Security Tech Blogs. Techworld Security Blog. They offer useful relevant topics on security and tech security news.

Galido
MARCH 19, 2019
Information technology is the use of any tech devices, infrastructure, software and processes to create and process, store, secure and exchange all forms of digital data. Our articles are typically focused on software recommendations, business, security, interesting topics and search engine optimization and marketing. Search Security.

Linux Academy
MARCH 26, 2019
By adding free cloud training to our Community Membership, students have the opportunity to develop their Linux and Cloud skills further. Each month, we will kick off our community content with a live study group allowing members of the Linux Academy community to come together and share their insights in order to learn from one another.

Scott Lowe
SEPTEMBER 27, 2019
Chip Zoller has a write-up on doing HTTPS ingress with Enterprise PKS. The Kubernetes project recently underwent a security audit; more information on the audit, along with links to the findings and other details, is available here. Daniel Sagi of Aqua Security explains the mechanics behind a Pod escape using file system mounts.

Scott Lowe
JANUARY 7, 2016
His journey started in June 2014 as a result of the Microsoft announcement regarding support for Linux and Kubernetes on Azure—this really indicated a shift in the industry. DevOps Enterprise Summit would be a good conference to attend (he couldn’t make it this past year). GitHub is a great way to share. List of Resources.
The Verge
JUNE 25, 2021
POSIX, which is a set of operating system standards. WSL, which is the part of Windows that lets you run Linux. In 2019, I think you had said to Wired , “The operating system is no longer the most important layer for us. ” PWAs, which are progressive web apps. UWPs, which are Universal Windows Platform apps.

Scott Lowe
NOVEMBER 7, 2014
It was good to read this post on Cumulus Linux first impressions by Jeremy Stretch. I’m a fan of Cumulus, but I’m admittedly a Linux guy (see here ) so you might say I’m a bit biased. Jeremy is a “hard-core” networking professional, and so hearing his feedback on Cumulus Linux was, in my opinion, useful.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content