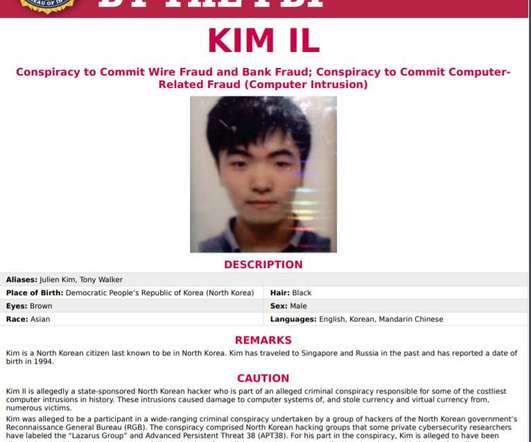
NotPetya and Olympic Destroyer Malware: 6 Russian Officers Charged
SecureWorld News
OCTOBER 20, 2020
But the GRU members being charged in this case started with other strains of malware and a narrow target: Ukraine's power grid. Assistant Attorney General For National Security, John Demers, says the power grid attacks in 2015 and 2016 were the first known destructive attacks against civilian critical infrastructure. and a large U.S.

























Let's personalize your content