Guarding the gates: a look at critical infrastructure security in 2023
CIO Business Intelligence
NOVEMBER 7, 2023
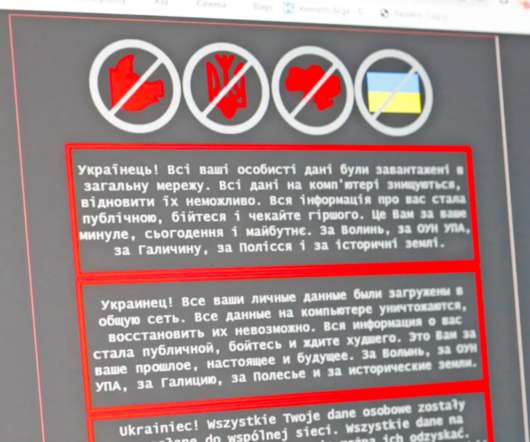
This analysis isn’t just a statistical exercise but a crucial necessity in our interconnected world, where the security of our digital infrastructure is intertwined with our physical safety and economic stability. It’s easy to envision the outcomes that could arise from a major assault on our vital infrastructure.


































Let's personalize your content