What You Need to Know About Neuromorphic Computing
Information Week
MAY 1, 2023
Concerned by recent AI news? Then get ready for computing that mimics the human brain.
Information Week
MAY 1, 2023
Concerned by recent AI news? Then get ready for computing that mimics the human brain.

IT Toolbox
MAY 3, 2023
How to create a roadmap to use data to manage utilities better. The post Why Data Is the New Currency for Utilities, and How To Use It appeared first on Spiceworks.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Forrester IT
MAY 2, 2023
RSAC 2023 is a wrap! The Forrester security and risk team had 11 attendees at the RSA Conference last week. We really enjoyed meeting with clients and colleagues old and new — and now we’re *exhausted.* It’s no mystery why; as a team, we collectively participated in over 230 meetings and took more than 1.
Information Week
MAY 3, 2023
Stakeholders from the war-torn country shared their stories of cybersecurity and data resilience at RSA Conference.

Advertisement
With its unparalleled flexibility, rapid development and cost-saving capabilities, open source is proving time and again that it’s the leader in data management. But as the growth in open source adoption increases, so does the complexity of your data infrastructure. In this Analyst Brief developed with IDC, discover how and why the best solution to this complexity is a managed service, including: Streamlined compliance with some of the most complex regulatory guidelines Simplified operations, li

IT Toolbox
MAY 2, 2023
The breach, discovered on March 27, occurred between February 24 and March 30. The post T-Mobile Suffers Data Breach Yet Again appeared first on Spiceworks.

Forrester IT
MAY 1, 2023
Cybersecurity threats continue to plague organizations, multiplying like Mogwai in the 1984 hit movie “Gremlins” (just don’t feed them after midnight). Forrester data shows that almost three-quarters of organizations reported one or more data breaches in the past 12 months.
Information Technology Zone brings together the best content for IT professionals from the widest variety of industry thought leaders.

TechSpot
APRIL 30, 2023
Sometimes, the most important insight seem obvious once said. CPUs, the core chip for PCs and servers, were once the king of compute. This was just a given, a fundamental assumption of the semiconductor industry.

IT Toolbox
MAY 2, 2023
Join experts worldwide on World Password Day 2023 to understand the key threats and best practices in password creation and management. The post World Password Day 2023: Tech Leaders Discuss Critical Threats and Best Practices appeared first on Spiceworks.

Association of Information Technology Professional
MAY 3, 2023
We’ve been getting a lot of questions about the new CompTIA CySA+, and we want to make sure you have the answers you need to decide whether or not it’s right for you.
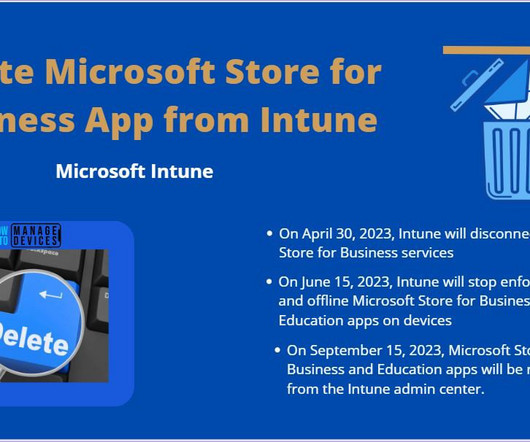
Anoop
MAY 5, 2023
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link] and Facebook Page to get the latest updates [link]. Read More The post Delete Microsoft Store for Business App from Intune appeared first on HTMD Community Blog #1 Modern Device Management Guides by Jitesh Kumar.

Advertisement
The complexity of financial data, the need for real-time insight, and the demand for user-friendly visualizations can seem daunting when it comes to analytics - but there is an easier way. With Logi Symphony, we aim to turn these challenges into opportunities. Our platform empowers you to seamlessly integrate advanced data analytics, generative AI, data visualization, and pixel-perfect reporting into your applications, transforming raw data into actionable insights.

Information Week
MAY 5, 2023
By taking a smart, measured, and calculated approach to cybersecurity, companies can effectively traverse the tough cyber waters while reducing their risk and exposure.

IT Toolbox
MAY 4, 2023
Innovation in AI is making accounting a lucrative profession for accountants who can leverage its value. The post The Very Real Impact of AI on the Future of Accounting appeared first on Spiceworks.
Association of Information Technology Professional
MAY 5, 2023
You’ll want to ensure you are fully prepared before you undertake the IT certification process. Here’s our advice on how to study for the new CompTIA CySA+ (CS0-003) exam.
Anoop
MAY 5, 2023
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link] and Facebook Page to get the latest updates [link]. Read More The post Disable or Enable New Monthly Features Enablement via Monthly Patches using Intune appeared first on HTMD Community Blog #1 Modern Device Management Guides by Vidya M A.

Advertisement
Adding high-quality entity resolution capabilities to enterprise applications, services, data fabrics or data pipelines can be daunting and expensive. Organizations often invest millions of dollars and years of effort to achieve subpar results. This guide will walk you through the requirements and challenges of implementing entity resolution. By the end, you'll understand what to look for, the most common mistakes and pitfalls to avoid, and your options.

Tech Republic Security
MAY 4, 2023
Drawing from a recent HackerOne event, HackerOne study and GitLab survey, learn how economic uncertainties are driving budget cuts, layoffs and hiring freezes across the cybersecurity industry. The post HackerOne: How the economy is impacting cybersecurity teams appeared first on TechRepublic.

IT Toolbox
MAY 4, 2023
Community in bloom indeed as the cloud-native community keeps growing. The post Kubernetes Blooms at KubeCon + CloudNativeCon 2023 in Amsterdam appeared first on Spiceworks.

Association of Information Technology Professional
MAY 4, 2023
Embedding a cyber-first approach within your company (and your customers) will better protect your business and should even lower day-to-day costs.
Information Week
MAY 5, 2023
International adversaries present ever more aggressive risks to cybersecurity while generative AI might accelerate attacks -- and possibly defense efforts.

Advertiser: Procom Services
From streamlining the job search process to efficiently navigating the influx of applications, AI-powered tools can revolutionize your recruitment efforts. By combining the efficiency of AI with the expertise of experienced recruiters, you can identify the ideal candidates who not only possess the necessary skills but also align with your company culture.

Tech Republic Security
MAY 4, 2023
Storing passkeys directly on devices will cut down on successful phishing, Google suggests. Is it the beginning of the end for passwords? The post Google adds passkey option to replace passwords on Gmail and other account services appeared first on TechRepublic.

IT Toolbox
MAY 4, 2023
Check out how developer teams can more effectively implement devsecops models. The post Tightening Security in the Production Process by Shifting Left appeared first on Spiceworks.

Association of Information Technology Professional
MAY 1, 2023
Confidently apply for IT jobs you feel are out of your league by effectively positioning your skill set.

Information Week
MAY 5, 2023
Ransomware Vulnerability Warning Pilot program is designed to alert critical infrastructure organizations to common exploits for ransomware attacks.

Speaker: Kat Conner
The challenge of delivering the right product at the right time while aligning with strategic objectives is more pressing than ever. Product management is evolving and gaining greater recognition as the means to creating this connection. Join our upcoming webinar and learn how to streamline your product development processes, infuse product thinking across the organization, and bridge the gap between vision and delivery.

Tech Republic Security
MAY 4, 2023
The U.K. government has released its annual Cyber Security Breaches Survey. Top cybersecurity threats, supply chain risks, incident responses and more are covered. The post Survey: State of cybersecurity in the UK appeared first on TechRepublic.

IT Toolbox
MAY 5, 2023
Passkeys for Google accounts are supported on Chrome OS, Windows, macOS, Android, and iOS platforms and Chrome, Safari, and Edge browsers. The post World Password Day or Passwordless Day? appeared first on Spiceworks.

Association of Information Technology Professional
MAY 2, 2023
Having trouble convincing work-from-home employees to leave their house? Try these strategies from fellow MSPs.

Information Week
MAY 2, 2023
As organizations embark on complex digital transformation efforts, their corporate boards are struggling with strategy. Better communication between IT leaders and the board is required.

Advertisement
In the fast-moving manufacturing sector, delivering mission-critical data insights to empower your end users or customers can be a challenge. Traditional BI tools can be cumbersome and difficult to integrate - but it doesn't have to be this way. Logi Symphony offers a powerful and user-friendly solution, allowing you to seamlessly embed self-service analytics, generative AI, data visualization, and pixel-perfect reporting directly into your applications.

Tech Republic Security
MAY 5, 2023
Google, Apple, Microsoft and other tech giants, as well as the FIDO Alliance, password managers and identity management vendors are all moving to passkeys, thanks to FIDO2. The post RIP World Password Day appeared first on TechRepublic.

IT Toolbox
MAY 4, 2023
Check out how organizations can generate value in the midst of an oncoming recession and layoffs. The post How to Create a Business Strategy to Thrive in 2023 appeared first on Spiceworks.
Anoop
MAY 4, 2023
Hello - Here is the new HTMD Blog Article for you. Enjoy reading it. Subscribe to YouTube Channel [link] and Facebook Page to get the latest updates [link]. Read More The post Free Azure Lab Setup and Azure for Students Lab Setup appeared first on HTMD Community Blog #1 Modern Device Management Guides by Vidya M A.

Information Week
MAY 2, 2023
The former Cisco boss discusses at RSA Conference his work with Nile, a startup he co-founded, and what he foresees for the networking sector.

Advertisement
It’s no surprise that Apache Cassandra has emerged as a popular choice for organizations of all sizes seeking a powerful solution to manage their data at a scale—but with great power comes great responsibility. Due to the inherent complexity of distributed databases, this white paper will uncover the 10 rules you’ll want to know when managing Apache Cassandra.
Let's personalize your content