6 Best Open Source IAM Tools in 2024
Tech Republic Security
FEBRUARY 22, 2024
Explore the top open source IAM (Identity and Access Management) tools, their features and how they can enhance your organization's security and access control.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
FEBRUARY 22, 2024
Explore the top open source IAM (Identity and Access Management) tools, their features and how they can enhance your organization's security and access control.

Tech Republic Security
MARCH 13, 2024
Learn about open-source password managers, the benefits, and the potential drawbacks of using these tools for managing your passwords securely.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CIO Business Intelligence
NOVEMBER 13, 2023
Open source has seen a great deal of momentum among mainframers, making collaboration easier and providing greater transparency. But for all of its benefits, open source is not without risks. By its very nature, open-source code is accessible to whoever wants to see it—including potential attackers.

SecureWorld News
NOVEMBER 6, 2023
In the interconnected digital landscape, vast amounts of valuable intelligence can be gleaned from publicly available open sources on the internet. Enter open-source intelligence (OSINT), the practice of legally collecting, analyzing, and making decisions based on public data.

CIO Business Intelligence
NOVEMBER 3, 2022
But in order to be successful in today’s technology-driven world, businesses that rely on the mainframe must modernize their operations and integrate the latest tools and technologies. One technology that modern mainframes need is secure open-source software.

TechSpot
OCTOBER 1, 2020
On Thursday, GitHub announced that after extensive testing, it launched a native code scanner that can detect security flaws in posted programs or code as it is being entered. The tool is powered by CodeQL—an open-source semantic code analyzer.

Network World
APRIL 7, 2022
Picking just 10 Linux open source security tools isn’t easy, especially when network professionals and security experts have dozens if not several hundred tools available to them. There are different sets of tools for just about every task—network tunneling, sniffing, scanning, mapping.
Dataconomy
MARCH 26, 2024
Runa Capital’s ROSS Index highlights the growing market for AI and open-source technologies, tracking the rapid expansion of this sector. These efforts showcase the diverse, evolving nature of AI and open-source ventures. It reflects an increasingly vibrant ecosystem fueled by technological advancements.
Venture Beast
FEBRUARY 3, 2022
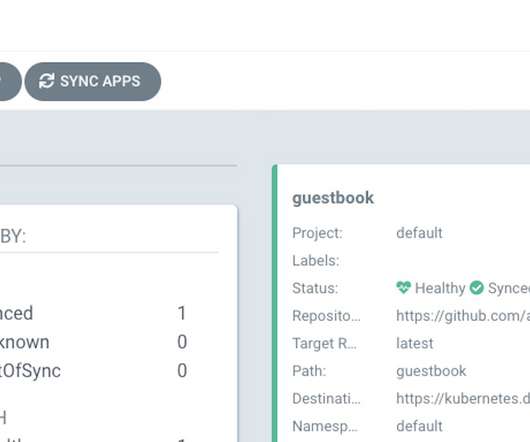
A zero day vulnerability with a "high" severity rating affects Argo CD, an open source developer tool for Kubernetes, Apiiro researchers said. Read More.

Venture Beast
OCTOBER 20, 2021
ControlFlag, an AI-powered tool developed by Intel to spot potential issues in software code, has been released in open source. Read More.

Venture Beast
NOVEMBER 11, 2021
Google has launched a new open source "fuzzing" project called ClusterFuzzLite, based on its existing ClusterFuzz tool. Read More.

Venture Beast
APRIL 9, 2021
Microsoft released CyberBattleSim, an open-source toolkit to let researchers create attack simulations and use AI to develop network defenses. Read More.

Venture Beast
AUGUST 2, 2021
GitLab's Package Hunter is an open source tool that helps developers detect malicious code in open source software components. Read More.

Venture Beast
MAY 4, 2021
Microsoft's Counterfit toolkit aims to enable security teams to more easily test the robustness of AI systems both in and prior to production. Read More.
CIO Business Intelligence
APRIL 24, 2024
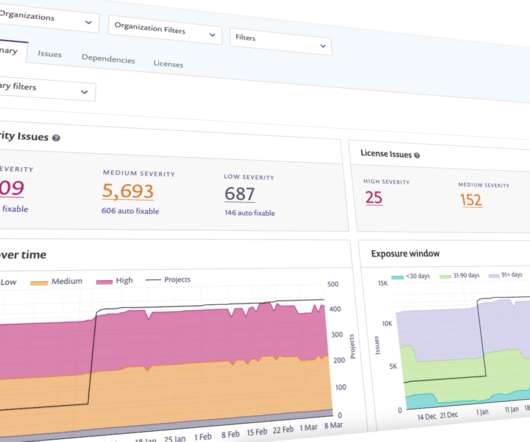
In today’s fast-paced software development landscape, managing and securing the software supply chain is crucial for delivering reliable and trusted software releases. For large companies especially, managing the secure use of 10+ technologies can be a nightmare without the right tools and processes in place.

CTOvision
NOVEMBER 26, 2014
Here is their press release : NSA Releases First in Series of Software Products to Open Source Community. The National Security Agency announced today the public release of its new technology that automates data flows among multiple computer networks, even when data formats and protocols differ. private sector in various ways.

Venture Beast
AUGUST 11, 2021
Allstar, a new tool released by the Open Source Security Foundation, aims to automatically fix vulnerabilities in open source projects. Read More.

Tech Republic
AUGUST 14, 2023
With security schema, Splunk and collaborators aim to transform alert telemetry from cacophony to chorus with one taxonomy across vendors and tools.

Tech Republic Security
DECEMBER 1, 2021
This won't replace antivirus software, but it can help you detect problems much more efficiently and allows more customization. Here's how to install it on Mac, Windows and Linux.

Venture Beast
OCTOBER 13, 2021
Cloud-native security observability platform Deepfence has open-sourced a tool that automatically finds and ranks software vulnerabilities. Read More.
Venture Beast
MAY 12, 2021
Snyk has acquired FossID, a startup that develops a software composition analysis tool for open source code. Read More.

Network World
FEBRUARY 21, 2017
Open source is a wonderful thing. A significant chunk of today’s enterprise IT and personal technology depends on open source software. But even while open source software is widely used in networking, operating systems, and virtualization, enterprise security platforms still tend to be proprietary and vendor-locked.

The Verge
JANUARY 9, 2022
A developer appears to have purposefully corrupted a pair of open-source libraries on GitHub and software registry npm — “ faker.js ” and “ colors.js ” — that thousands of users depend on, rendering any project that contains these libraries useless, as reported by Bleeping Computer. Illustration by Alex Castro / The Verge.

Forrester IT
AUGUST 18, 2021
Whether through infiltrating the software delivery pipeline, deliberately uploading malicious components to popular repositories, or taking advantage of existing vulnerabilities in open source components, attackers are leveraging gaps in supply chain controls to compromise […].

CTOvision
DECEMBER 15, 2020
Sonatype, the leading provider of innovation-friendly open source security tools, announced the appointment of a key addition to its executive management team, Jon Mellon, who joins the company in the […].

SecureWorld News
SEPTEMBER 22, 2022
A 15-year-old vulnerability in the Python programming language is making headlines again as new research shows that the vulnerability is estimated to be present in over 350,000 open source projects and some closed source projects, according to the Trellix Advanced Research Center.

IT Toolbox
OCTOBER 19, 2022
Dubbed Text4Shell or Act4Shell, the vulnerability is eliciting some disconcerting responses from the security and tech communities, possibly due to its name and the fact that, like Log4Shell, it resides in another open-source Java-based tool.

CIO Business Intelligence
APRIL 25, 2024
The dynamic nature of the cloud — and the need for continually optimize operations — often drives requirements unique to a CIO’s enterprise, meaning that even some popular third-party cloud cost optimization tools may no longer fit an enterprise’s specific requirements. Garcia gives the example of the AWS cURL file, written three times daily.

Tech Republic Security
MARCH 11, 2021
sigstore could eliminate the headaches associated with current software signing technology through public ledgers.

CIO Business Intelligence
NOVEMBER 13, 2023
Mainframe developers face unique challenges when ensuring their IT environments are secure. Tools like open source have helped give a boost to software development, but it also means security needs to always be top of mind. Chief among those challenges? What’s the state of DevSecOps today?

Tech Republic Security
AUGUST 3, 2020
One of the first announcements at BlackHat USA 2020 is an open-source tool to fight malware that BlackBerry first used internally and is now making available to everyone.

Tech Republic Security
FEBRUARY 28, 2020
If your desktop of choice is Linux, you don't have to be without a 2FA tool, thanks to OTPClient.

ForAllSecure
MAY 4, 2022
For the next three hours they integrated Mayhem Free into various open source software GitHub repositories. The purpose is to help ForAllSecure secure open source software. He then introduced a CMake example before giving the students exercises using open source fuzz testing tools such as AFL and libfuzzer.

TM Forum
MARCH 17, 2022
Configuration as code is the best available approach to secure and modernize cloud infrastructure. By leveraging cloud-based productivity and collaboration tools, employees can work from anywhere while remaining hyper-connected to business processes. The first is by using open-source tooling. Microsoft 365 DSC.

GeekWire
JUNE 27, 2023
Expanso provides managed services on top of Bacalhau, an open-source platform that enables efficient and secure distributed computation. He was previously the lead product manager for Kubernetes and Google Kubernetes Engine at Google, and head of Open Source Machine Learning Strategy at Microsoft.
The Verge
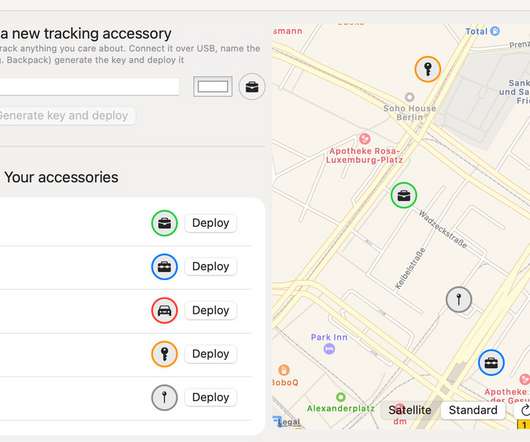
MARCH 4, 2021
Apple has promised to open up its Find My app to third-party accessory makers. But ahead of that, there’s a new tool that will let anybody make their own Bluetooth tracking tag to use with the Find My network so they can track its location. It is, in short, a way to create your own DIY AirTags today.

Kitaboo
OCTOBER 20, 2023
Before we jump to the various tools and resources available for teaching data management, let’s understand what it is first. Table of Contents: What are Data Management Skills? Importance of Teaching Data Management Skills Tools for Teaching Data Management Skills Resources for Educators Wrapping Up!

ForAllSecure
MAY 30, 2023
Gone are the days of slapping security on as an afterthought. The only way to ensure software is safe is to integrate security testing into your DevOps process. Software security testing is time-consuming for development teams. Security testing tools can help save time, especially if they help automate your process.

CIO Business Intelligence
MARCH 15, 2023
Multifactor authentication fatigue and biometrics shortcomings Multifactor authentication (MFA) is a popular technique for strengthening the security around logins. Securing the software supply chain The Log4j vulnerability that reared its ugly head in late 2021 showed a bright light on the problem of software supply chain security.

The Verge
AUGUST 7, 2020
But nearly all of those password checkup tools owe something to Troy Hunt’s Have I Been Pwned , which was kind of a novel idea when it first launched 7 years ago — and Hunt is now open-sourcing his website codebase so the idea can spread even further. Illustration by Alex Castro / The Verge.

CTOvision
MAY 9, 2014
Following the June 2013 Edward Snowden leaks we observe an increased pace of innovation, specifically new competing jihadist platforms and three (3) major new encryption tools from three (3) different organizations – GIMF, Al-Fajr Technical Committee, and ISIS – within a three to five-month time frame of the leaks.

Tech Republic Security
MARCH 11, 2022
Developers are exploring new tools and methodologies to ensure the next log4j doesn’t happen. The post Log4j postmortem: Developers are taking a hard look at software supply-chain security gaps appeared first on TechRepublic. Will it work?

Tech Republic Security
MAY 27, 2021
Jack Wallen shows you how to install and use this handy tool. MOSH makes it possible for SSH connection to persist, even as you roam from one network to another.

CIO Business Intelligence
JUNE 16, 2022
BPM tools help organizations create, execute, optimize, and monitor business processes. There are dozens of tools that fall into this category, including homegrown systems built by the local IT staff. Some of these low-code or no-code enhancements enable people with no formal programming training to use BPM tools successfully.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content