How ZTNA and the Right Network Hardware Drives IoT Security
IT Toolbox
OCTOBER 3, 2023
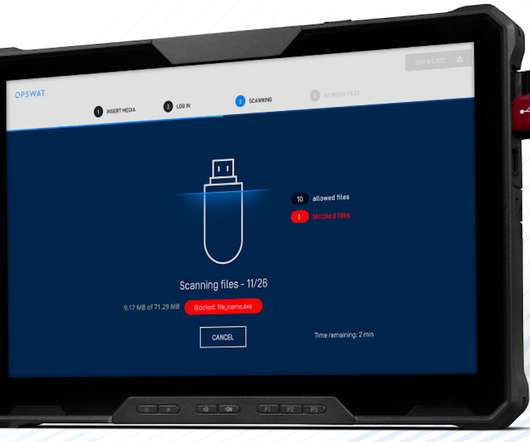
The right network hardware and ZTNA can protect your IoT environment. The post How ZTNA and the Right Network Hardware Drives IoT Security appeared first on Spiceworks.


















































Let's personalize your content