Cisco Talos Reports Microsoft Windows Policy Loophole Being Exploited by Threat Actor
Tech Republic Security
JULY 11, 2023
Learn how a malicious driver exploits a loophole in the Windows operating system to run at kernel level.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
JULY 11, 2023
Learn how a malicious driver exploits a loophole in the Windows operating system to run at kernel level.

Dataconomy
MARCH 25, 2024
processors from government-operated computers and servers, thereby excluding chips manufactured by Intel and AMD, according to a report by the Financial Times. Authorities above the township level are mandated to acquire processors and operating systems deemed “safe and reliable” as per the Financial Times. and China.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

SecureWorld News
JUNE 13, 2023
Critical Start today released its biannual Cyber Intelligence Report, featuring the top threats observed in the first half of 2023 and emerging cybersecurity trends impacting the healthcare, financial services, and state and local government industries.

GeekWire
NOVEMBER 9, 2023
Back in June, Asus also offered its $599/$699 ROG Ally, a portable PC with both TV and desktop compatibilities that’s powered by Windows 11. -based Valve has not offered any information regarding what motivated its decision to give the Steam Deck a hardware refresh.

CIO Business Intelligence
DECEMBER 4, 2023
Its versatility, reliability, stability, and open-source and third-party libraries and frameworks make developing and running applications very efficient. According to State of Java Survey and Report 2023 , an independently run study of more than 2,000 Java users, Java users have taken notice.

SecureWorld News
AUGUST 10, 2020
When technology companies close the support door on their old systems and software, it opens the gates for cybercriminals. The most recent example of this is for organizations using Windows 7. Windows 7 'End of Life' is a cybercrime opportunity. An unsupported operating system grants hackers easier pickings.

Kitaboo
MARCH 26, 2024
Determine Your Primary Goal Consider Your Operating System Evaluate Your Budget Assess Your Technical Expertise Choose Software Based On Your Desired Output Formats Check For Additional Features Test the Software Research User Reviews Plan for Future Updates and Support III.

Dataconomy
DECEMBER 25, 2023
Soon, custom firmware emerged, expanding the attack canvas to Android and Windows, spamming users with unwanted advertisements, and potentially compromising device security. Pen-testing tool Flipper Zero was eventually used for Bluetooth spam attacks on the iOS operating system ( Image credit ) What is Wall of Flippers?

ForAllSecure
OCTOBER 13, 2020
It required that I install PPP which stands for Point to Point Protocol, which was missing in native Windows 3.1. One year after Netscape Navigator launched, Microsoft released, as part of Windows 95, a browser called Internet Explorer, launching the infamous browser wars. Tim: I would say it's almost always in the open source code.

ForAllSecure
OCTOBER 13, 2020
It required that I install PPP which stands for Point to Point Protocol, which was missing in native Windows 3.1. One year after Netscape Navigator launched, Microsoft released, as part of Windows 95, a browser called Internet Explorer, launching the infamous browser wars. Tim: I would say it's almost always in the open source code.

ForAllSecure
OCTOBER 13, 2020
It required that I install PPP which stands for Point to Point Protocol, which was missing in native Windows 3.1. One year after Netscape Navigator launched, Microsoft released, as part of Windows 95, a browser called Internet Explorer, launching the infamous browser wars. Tim: I would say it's almost always in the open source code.

Galido
AUGUST 22, 2016
Asterisk turns an ordinary computer into a communications server and powers IP PBX systems, VoIP gateways, conference servers and is in use today by small businesses, large businesses, call centers, carriers and governments worldwide. It’s been around since 1999, so it’s no fly by night operation. Compatibility with CRMs.
Kitaboo
MAY 19, 2020
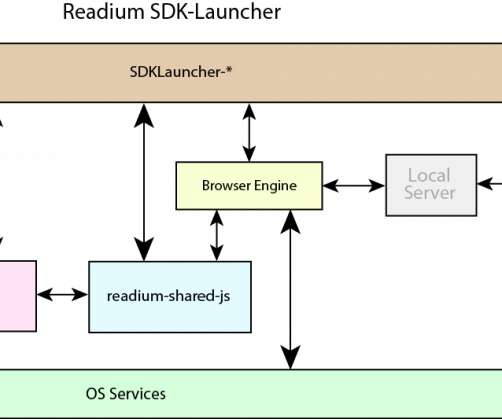
The Open Source Foundation aims to develop technology for expediting the adoption of ePUB3 and the Open Web Platform by the Digital Publishing Industry. It strives to deliver leading-edge functionality that is fully specified, free, open, and interoperable. It is designed for publishers to create and deliver eBooks.

ForAllSecure
JUNE 16, 2020
The Google Chrome web browser, for example, is used on billions of devices and is completely open source, allowing any attacker to review exactly how the software works. In 2019, Google reported finding over 20,000 vulnerabilities automatically with its in-house fuzzing toolchain. Google isn’t alone. How to get started?

ForAllSecure
JUNE 16, 2020
The Google Chrome web browser, for example, is used on billions of devices and is completely open source, allowing any attacker to review exactly how the software works. In 2019, Google reported finding over 20,000 vulnerabilities automatically with its in-house fuzzing toolchain. Google isn’t alone. How to get started?

ForAllSecure
JUNE 16, 2020
The Google Chrome web browser, for example, is used on billions of devices and is completely open source, allowing any attacker to review exactly how the software works. In 2019, Google reported finding over 20,000 vulnerabilities automatically with its in-house fuzzing toolchain. Google isn’t alone. How to get started?

Galido
MARCH 19, 2019
These areas of IT include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Operating System & Software Blogs. Find the links to these blogs in the descriptions below. CIO Dashboard. CloudTweaks.

SPF13
MARCH 20, 2015
In the last few years open source has transformed the software industry. From Android to Wikipedia, open source is everywhere, but how does one succeed in it? What Every Successful Open Source Project Needs. spf13 Chief Operator @ Docker? Open Source is taking over the world. Transcript.

Galido
MAY 1, 2019
These areas of tech include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Below are 50+ of our favorite Tech Blogs – great suggested reads and follows to help stay ahead of the curve. CIO Dashboard.

Galido
MARCH 22, 2019
These areas of tech include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Below are 50+ of our favorite Tech Blogs – great suggested reads and follows to help stay ahead of the curve. CIO Dashboard.

Galido
MARCH 19, 2019
These areas of IT include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Operating System & Software Blogs. Find the links to these blogs in the descriptions below. CIO Dashboard. CloudTweaks.

Galido
SEPTEMBER 25, 2019
These areas of tech include general IT and technology, security, IT feeds, cloud computing, data center, mobile, social media, tips and tricks, virtualization, and operating system and software blogs. Below are 50+ of our favorite Tech Blogs – great suggested reads and follows to help stay ahead of the curve. CIO Dashboard.

Scott Lowe
APRIL 24, 2020
I recently stumbled across this regular list of AWS open source news and updates by Ricardo Sueiras. Operating Systems/Applications. I recently learned about the Johari window , an aid for understanding the self. Dustin has done a good job of including some useful details in this post. Career/Soft Skills.

ForAllSecure
DECEMBER 2, 2021
You’ll want someone with years of pen testing experience, some one who knows the operating system like no other. So in general, an operating system that eventually allows you to gain more information about the context within which attack was made. Maybe your first concern is to make sure the company is functional.

Galido
DECEMBER 28, 2018
Hacking and data breaches are a common thing today, especially with the rise of open source platforms and electronic transactions. While the majority of people may be lucky to date, there are numerous reports issues over the past few years reporting the large financial cost of security breaches. Why Should You Care?

ForAllSecure
AUGUST 12, 2019
Open Source Security Podcast helps listeners better understand security topics of the day. Hosted by Kurt Seifried and Josh Bressers, the pair covers a wide range of topics including IoT, application security, operational security, cloud, devops, and security news of the day. The full transcript is also available below.

ForAllSecure
MARCH 24, 2021
How could open source software be vulnerable for so long? So I reported this flaw to the vendor … and the response was not what I expected. In a moment I’ll tell you about a flaw discovered only through fuzz testing in a very old open source product. And I was able to repeat the process over and over.

ForAllSecure
MARCH 24, 2021
How could open source software be vulnerable for so long? So I reported this flaw to the vendor … and the response was not what I expected. In a moment I’ll tell you about a flaw discovered only through fuzz testing in a very old open source product. And I was able to repeat the process over and over.

ForAllSecure
AUGUST 12, 2019
Open Source Security Podcast helps listeners better understand security topics of the day. Hosted by Kurt Seifried and Josh Bressers, the pair covers a wide range of topics including IoT, application security, operational security, cloud, devops, and security news of the day. The full transcript is also available below.

ForAllSecure
AUGUST 12, 2019
Open Source Security Podcast helps listeners better understand security topics of the day. Hosted by Kurt Seifried and Josh Bressers, the pair covers a wide range of topics including IoT, application security, operational security, cloud, devops, and security news of the day. The full transcript is also available below.

ForAllSecure
APRIL 22, 2021
Calderon: And even when we wrote the book it got tricky because some of the cool findings that we had, couldn't be mentioned in the book so we had to you know work on open source boards and come up, use open source laboratories instead of doing real life examples. And it's not just stories from the authors themselves.

ForAllSecure
APRIL 22, 2021
Calderon: And even when we wrote the book it got tricky because some of the cool findings that we had, couldn't be mentioned in the book so we had to you know work on open source boards and come up, use open source laboratories instead of doing real life examples. And it's not just stories from the authors themselves.

Data Center Knowledge
JULY 15, 2013
For Google has released data suggesting it has at least 900,000 servers under management, and media reports suggest they have deployed at least one million servers over the life of the company. Microsoft’s ‘Cloud Operating System’ 218,000 Servers in Microsoft Data Centers? Posted July 16th, 2013.

ForAllSecure
OCTOBER 29, 2020
Clearly having individual vendors provide the security wasn’t working, so the state moved toward adopting open source software. It also lead to even more testing of election system devices in other states. We even rigged the system to play the Michigan Fight Song every time somebody voted. That’s security 101.

ForAllSecure
OCTOBER 29, 2020
Clearly having individual vendors provide the security wasn’t working, so the state moved toward adopting open source software. It also lead to even more testing of election system devices in other states. We even rigged the system to play the Michigan Fight Song every time somebody voted. That’s security 101.

ForAllSecure
OCTOBER 20, 2020
Clearly having individual vendors provide the security wasn’t working, so the state moved toward adopting open source software. It also lead to even more testing of election system devices in other states. We even rigged the system to play the Michigan Fight Song every time somebody voted. That’s security 101.
Vox
MARCH 4, 2023
TikTok has a generative AI text-to-image system. And the open-source model Stable Diffusion can generate detailed and specific images in all kinds of styles from text prompts. Bing also told an AP reporter that he was acting like Hitler. Design platform Canva has one , too.
ForAllSecure
AUGUST 26, 2021
It's the software that emulates a physical computer virtually to run programs operating systems stored data connected networks and do other typical computing functions. Peleg: If you take a look of the windows. Virtual machines allow the cloud to be elastic ever changing to grow as demand requires, and to shrink if needed.

Scott Lowe
SEPTEMBER 8, 2016
Intel has finally started shipping silicon photonics gear, according to this report from El Reg (news coming out of IDF16). This blog post on shielded VMs in Windows Server 2016 is a bit light on details, but the embedded video may be more informative (I didn’t watch it). Operating Systems/Applications. Servers/Hardware.

ForAllSecure
AUGUST 16, 2022
In some cases they’re taking open source, community-based tools and leveraging them in creative new ways against common threats. They're the long game operations where something as small as a single phishing email could escalate into millions of IDs being exfiltrated. Is this just another report?

ForAllSecure
MARCH 30, 2022
I’m happy to report that Microsoft addressed both quickly. And I remember calling Symantec and reporting a serious bug in an early version of their password manager. ” Why indeed, the fact of the matter is that it opened the password manager without any password so anyone could see in clear text its content.

Vox
JULY 8, 2020
Apple and Android offer operating system SDKs so developers can build their apps for their respective devices, and third parties offer SDKs that allow developers to add certain features to those apps quickly and with minimal effort. Over the years, app stores and operating systems have cracked down on some of this tracking.

ForAllSecure
MAY 4, 2021
Vamosi: ATT&CK started as a workshop exercise to document common tactics, techniques and procedures, T TPS that advanced persistent threats used against Windows Enterprise environments, advanced persistent threats are just as they seem. It has operated since 2008. So it's it's a fun time. Vamosi: they chose APT 29.

ForAllSecure
MAY 4, 2021
Vamosi: ATT&CK started as a workshop exercise to document common tactics, techniques and procedures, T TPS that advanced persistent threats used against Windows Enterprise environments, advanced persistent threats are just as they seem. It has operated since 2008. So it's it's a fun time. Vamosi: they chose APT 29.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content