Governance and Fighting the Curse of Complexity
CIO Business Intelligence
MARCH 20, 2024
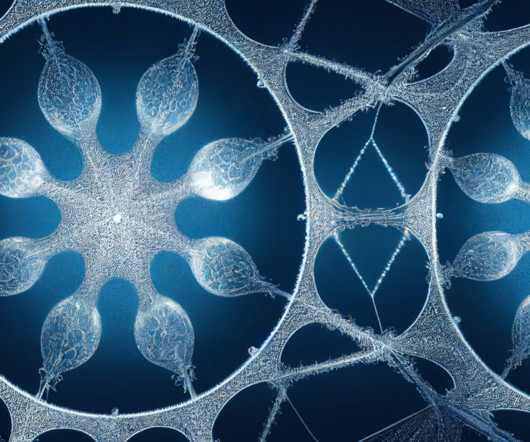
The boulder is made from complex infrastructure, network connections, data stores, and devices. The road other is paved with disciplined IT and business governance. Shadow IT introduces systems and applications that are often outside of an enterprise’s catalog of IT tools. The task is Sisyphean. The mountain is IT complexity.
















































Let's personalize your content